当前位置:网站首页>Threshold-based filtering buffer management scheme in a shared buffer packet switch core part of the paper
Threshold-based filtering buffer management scheme in a shared buffer packet switch core part of the paper
2022-08-10 12:06:00 【is blooming】
TF cache management solution:
The TF scheme aims to use shared buffers efficiently and fairly, that is, to minimize the overall packet loss probability and guarantee fair buffer usage among different output ports.Output ports are classified as active or inactive output ports based on queue length, and the classification is based on a dedicated buffer allocation factor (B/N), where B is the total buffer size and N is the number of output ports in Definition 1.By reserving sufficient buffer size for all inactive output ports in overload mode in Definition 2, TF can protect arriving packets destined for inactive output ports from being dropped.
Definition 1: If the queue length of output port i is greater than B/N, output port i is called an active output port; otherwise, it is called an inactive output port.
Definition 2: If the total queue length is greater than B-T, the state of packet exchange is called overload mode; otherwise, it is called non-overload mode, where T is the TF threshold factor in this scheme.
The value of T should be kept as small as possible so that all output ports can share and use more buffer space.This can increase buffer utilization.However, a very small value of T will cause most incoming packets to inactive output ports to be dropped due to insufficient buffer space reserved.In this case, the buffering behavior of TF is similar to the drop-tail of CS, so the overall packet loss probability is greatly increased.Next, we show the operation of the TF scheme in non-reload mode.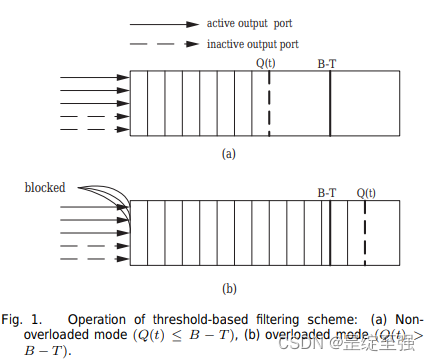
Where Xi(t) is the maximum allowable buffer size for output port i at time t and Ai(t) is the number of all incoming packets destined for output port i at time t.When the switch state is in the non-overload mode, the operation of the TF is shown in Fig. 1(a).In Figure 1(a), all arriving packets are admitted into the buffer regardless of whether their destination is an active or inactive output port, where Q(t) is denoted as the total queue length at time t.Therefore, the maximum allowable buffer size for output port i at time t is equal to the number of all incoming packets destined for output port i at time t.Subsequently, (2) is used to show the operation of the TF scheme in reload mode.

where Sa(t) is the set of active output ports at time t and Sin(t) is the set of inactive output ports at time t.When the switch state is in overload mode, the operation of TF is shown in Fig. 1(b).In Figure 1(b), TF starts filtering arriving packets based on their destination.If the destination of incoming packets is an active output port, the filter simply blocks all incoming packets.On the other hand, if the destination of incoming packets is an inactive output port, then all those packets are allowed into the buffer.With a sufficient value of T, TF can guarantee that packets arriving at inactive output ports go into the buffer.This means that TF will not limit the length increase of inactive output ports unless they are diverted to active output ports.Therefore, TF is able to provide fairness and an overall low packet loss rate.
边栏推荐
猜你喜欢

LeetCode50天刷题计划(Day 17—— 下一个序列(14.50-16.30)

dedecms支持Word内容一键导入

一文读懂NFT数字藏品为何风靡全球?

怎么加入自媒体,了解这5种变现模式,让账号快速变现

Since the media hot style title how to write?Taught you how to write the title
Database management tool: dynamic read-write separation

How to join We Media, learn about these 5 monetization modes, and make your account quickly monetize

第六届”蓝帽杯“全国大学生网络安全技能大赛半决赛部分WriteUp

Article take you understand interrupt the key driver of polling mechanism

项目部署、
随机推荐
Centos7 environment uses Mysql offline installation package to install Mysql5.7
HDU 6040 Hints of sd0061 (技巧)
力扣练习——61 根据字符出现频率排序
可视化服务编排在金融APP中的实践
LeetCode 445. 两数相加 II
自媒体爆款标题怎么写?手把手教你写热门标题
mpf6_Time Series Data_quandl_correct kernel PCA_AIC_BIC_trend_log_return_seasonal_decompose_sARIMAx_ADFull
第六届”蓝帽杯“全国大学生网络安全技能大赛半决赛部分WriteUp
rider内Mono脚本找不到引用资源
jlink and swd interface definition
LeetCode 83. 删除排序链表中的重复元素
孩子自律性不够?猿辅导:计划表要注意“留白”给孩子更多掌控感
WeChat applet, global variables change in one place and the state in other places also changes.
LeetCode 237. Delete a node in a linked list
怎么加入自媒体,了解这5种变现模式,让账号快速变现
英特尔推送20220809 CPU微码更新 修补Intel-SA-00657安全漏洞
AutoCAD Map 3D功能之一暴力处理悬挂点(延伸)
Centos7环境使用Mysql离线安装包安装Mysql5.7
Do self-media monthly income tens of thousands?Several self-media tools that bloggers are using
LeetCode 146. LRU 缓存
