当前位置:网站首页>XCTF College War "Epidemic" Network Security Sharing Competition Misc wp
XCTF College War "Epidemic" Network Security Sharing Competition Misc wp
2022-08-09 08:40:00 【z.volcano】
题目地址
题目
2019-nCoV
giveflag
隐藏的信息
I came up first to blast the password of the compressed package,Found this later伪加密,Get one after breaking itwav文件,放到Audacity里分析,查看频谱图,有发现.
There is something in the head and the tail
Here is dial tone steganography,双音多频,用脚本Scroll or look at the table.
Finally get a string of numbers187485618521.
Look back at the QR code again,After inversion processing, complete the locator,You will find that you have been deceived.
用winhex打开,Two strings of characters were found
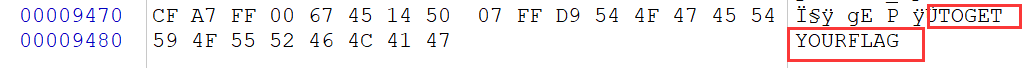
So put the resulting numbersbase64编码一次,再套上flag{},即flag{MTg3NDg1NjE4NTIx}
简单MISC
Also two files
The compressed package is encrypted,先看photo.jpg,winhexAnalysis revealed additional information,foremost分离出一个压缩包,里面有一个txt文件,内容如下
./.–./…/-…/./–/…/-.-./…/…/-/…-/.-/-/…/—/-./—/…-./…-/-./…/…-/./.-./…/…/-/-.–/.–/.-/.-.
Apparently Morse code,解密得到EPIDEMICSITUATIONOFUNIVERSITYWAR,This is the password for the compressed package
There is one in the compressed packagetxt,内容
VGgxc19pc19GbGFHX3lvdV9hUkVfcmlnSFQ=
base64解密得到flag
ez_mem&usb
usb内存取证,The final result needs to be converted to lowercase
Download the attachment to get a data package,扔进wireshark里,导出httpStreams found these things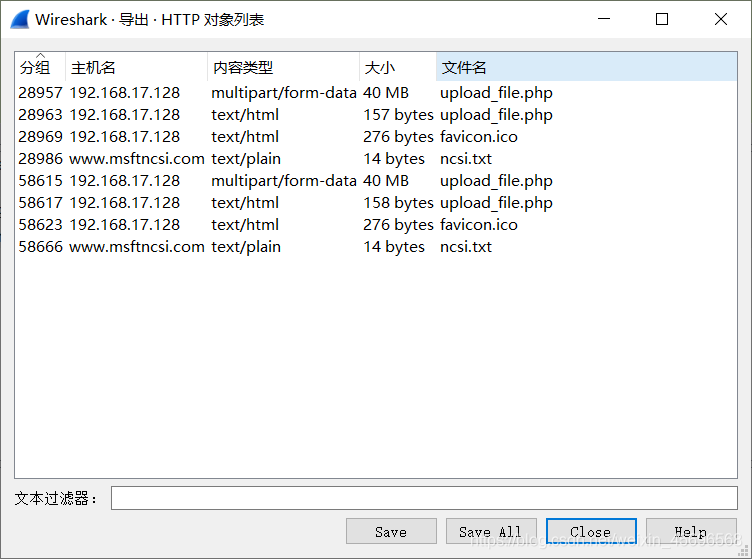
After extracting the file,把upload_file.php扔进010editor里,发现有压缩包,binwalk提取出来,Finally got it in the compressed packagedata.vmem文件
然后掏出volatility进行分析
First look at the system version information: python vol.py -f data.vmem imageinfo
INFO : volatility.debug : Determining profile based on KDBG search...
Suggested Profile(s) : WinXPSP2x86, WinXPSP3x86 (Instantiated with WinXPSP2x86)
AS Layer1 : IA32PagedMemoryPae (Kernel AS)
AS Layer2 : FileAddressSpace (/home/volcano/桌面/volatility-master/data.vmem)
PAE type : PAE
DTB : 0xb18000L
KDBG : 0x80546ae0L
Number of Processors : 1
Image Type (Service Pack) : 3
KPCR for CPU 0 : 0xffdff000L
KUSER_SHARED_DATA : 0xffdf0000L
Image date and time : 2020-02-24 07:56:47 UTC+0000
Image local date and time : 2020-02-24 15:56:47 +0800
Get the most likely architectureWinXPSP2x86
再看看进程:python vol.py --profile=WinXPSP2x86 -f data.vmem pslist
Offset(V) Name PID PPID Thds Hnds Sess Wow64 Start Exit
---------- -------------------- ------ ------ ------ -------- ------ ------ ------------------------------ ------------------------------
0x80ea2660 System 4 0 52 231 ------ 0
0xff57fc28 smss.exe 372 4 3 19 ------ 0 2020-02-23 13:17:13 UTC+0000
0xff432020 csrss.exe 464 372 12 317 0 0 2020-02-23 13:17:13 UTC+0000
0xff435020 winlogon.exe 492 372 20 501 0 0 2020-02-23 13:17:13 UTC+0000
0xff445020 services.exe 668 492 16 253 0 0 2020-02-23 13:17:14 UTC+0000
0xff46b020 lsass.exe 680 492 19 309 0 0 2020-02-23 13:17:14 UTC+0000
0xff510bf0 vmacthlp.exe 836 668 1 25 0 0 2020-02-23 13:17:14 UTC+0000
0xff493568 svchost.exe 848 668 14 189 0 0 2020-02-23 13:17:14 UTC+0000
0xff491a78 svchost.exe 932 668 11 230 0 0 2020-02-23 13:17:14 UTC+0000
0xff416b10 svchost.exe 1024 668 44 939 0 0 2020-02-23 13:17:14 UTC+0000
0x80dac020 svchost.exe 1072 668 4 57 0 0 2020-02-23 13:17:14 UTC+0000
0xff4ca4e0 svchost.exe 1132 668 7 118 0 0 2020-02-23 13:17:14 UTC+0000
0xff30d020 explorer.exe 1476 1400 13 481 0 0 2020-02-23 13:17:15 UTC+0000
0xff51d468 spoolsv.exe 1568 668 10 120 0 0 2020-02-23 13:17:15 UTC+0000
0xff5793d8 VGAuthService.e 1932 668 2 60 0 0 2020-02-23 13:17:33 UTC+0000
0xff576da0 vmtoolsd.exe 2008 668 7 265 0 0 2020-02-23 13:17:40 UTC+0000
0xff4afda0 wmiprvse.exe 540 848 13 242 0 0 2020-02-23 13:17:41 UTC+0000
0xff486da0 vmtoolsd.exe 588 1476 6 229 0 0 2020-02-23 13:17:41 UTC+0000
0xff47dda0 ctfmon.exe 596 1476 1 71 0 0 2020-02-23 13:17:41 UTC+0000
0xff5b57b8 cmd.exe 1396 1476 1 61 0 0 2020-02-23 13:24:09 UTC+0000
0xff4583c0 conime.exe 544 1396 1 38 0 0 2020-02-23 13:24:09 UTC+0000
This is what is more suspiciouscmd.exe了
所以看一下 cmd 命令使用情况:python vol.py --profile=WinXPSP2x86 -f data.vmem cmdscan
**************************************************
CommandProcess: csrss.exe Pid: 464
CommandHistory: 0x556bb8 Application: cmd.exe Flags: Allocated, Reset
CommandCount: 2 LastAdded: 1 LastDisplayed: 1
FirstCommand: 0 CommandCountMax: 50
ProcessHandle: 0x504
Cmd #0 @ 0x3609ea0: passwd:weak_auth_top100
Cmd #1 @ 0x5576d0: start wireshark
Cmd #13 @ 0x9f009f: ??
Cmd #41 @ 0x9f003f: ?\?????????
The first two commands are useful,First get the passwordweak_auth_top100,然后启动了wireshark
Scan the file again:python vol.py --profile=WinXPSP2x86 -f data.vmem filescan
发现可疑文件flag.img,把它导出来:python vol.py --profile=WinXPSP2x86 -f data.vmem dumpfiles -Q 0x0000000001155f90 -n --dump-dir=./,得到文件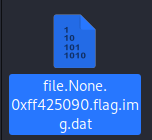
foremostDetach an encrypted compressed package(这里用binwalk可能会出问题),Decrypt with the password obtained earlier.
拿到usbdata.txt,里面是usb流量数据,Obviously keyboard traffic,Use a script found on the Internet,运行之后得到flag
mappings = {
0x04:"A", 0x05:"B", 0x06:"C", 0x07:"D", 0x08:"E", 0x09:"F", 0x0A:"G", 0x0B:"H", 0x0C:"I", 0x0D:"J", 0x0E:"K", 0x0F:"L", 0x10:"M", 0x11:"N",0x12:"O", 0x13:"P", 0x14:"Q", 0x15:"R", 0x16:"S", 0x17:"T", 0x18:"U",0x19:"V", 0x1A:"W", 0x1B:"X", 0x1C:"Y", 0x1D:"Z", 0x1E:"1", 0x1F:"2", 0x20:"3", 0x21:"4", 0x22:"5", 0x23:"6", 0x24:"7", 0x25:"8", 0x26:"9", 0x27:"0", 0x28:"\n", 0x2a:"[DEL]", 0X2B:" ", 0x2C:" ", 0x2D:"-", 0x2E:"=", 0x2F:"[", 0x30:"]", 0x31:"\\", 0x32:"~", 0x33:";", 0x34:"'", 0x36:",", 0x37:"." }
nums = []
keys = open('usbdata.txt')
for line in keys:
if line[0]!='0' or line[1]!='0' or line[3]!='0' or line[4]!='0' or line[9]!='0' or line[10]!='0' or line[12]!='0' or line[13]!='0' or line[15]!='0' or line[16]!='0' or line[18]!='0' or line[19]!='0' or line[21]!='0' or line[22]!='0':
continue
nums.append(int(line[6:8],16))
keys.close()
output = ""
for n in nums:
if n == 0 :
continue
if n in mappings:
output += mappings[n]
else:
output += '[unknown]'
print ('output :\n' + output)
武汉加油

binwalk分离出一个压缩包,里面是flag.exe文件
Open a wave of tests,发现每输入6个字符,它会返回一个字符串
Should be to enter specific characters,返回flag,Too bad I can't reverse it…
It shouldn't be a hard guess,Change direction to see if there are any hints,因为是jpg图片,所以使用outguess和steghide查看一下
Found that a password is requiredsteghide加密
steghideBlasting is not supported natively,这里借助https://github.com/Va5c0/Steghide-Brute-Force-Tool
具体用法:
python steg_brute.py -b -d [字典] -f [jpg_file]
A library needs to be installed here:
pip install progressbar2
Finally got the password isctf,提取steghide extract -p 'ctf' -sf 1.jpg
得到flag.txt
The outbreak of pneumonia caused by the new coronavirus has touched the hearts of the whole country,大家守望相助、众志成城、共克时艰,Let's help Wuhan together.Believe in the party center、国务院的领导下,We will surely win this battle of epidemic prevention and control without gunpowder smoke.
’ 武 汉 加 油 ! --HEUctfer
很明显,flag.exe需要的6个字符就是' 武 汉 加 油 !
边栏推荐
猜你喜欢
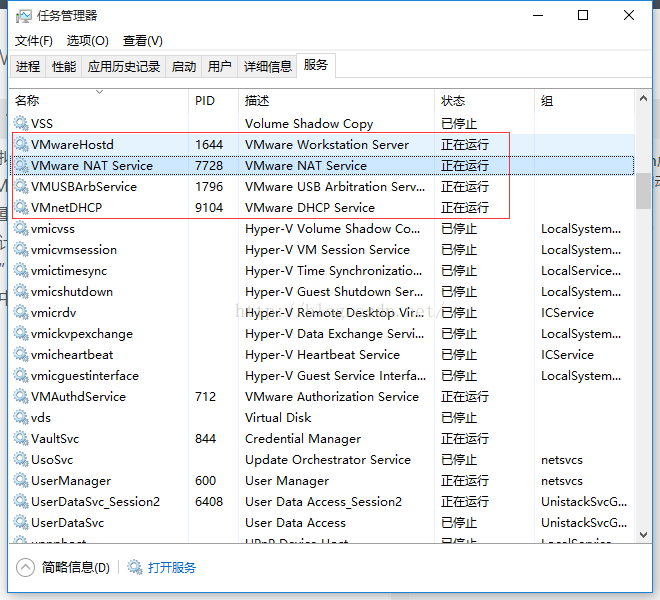
VMware virtual machine cannot be connected to the Internet after forced shutdown
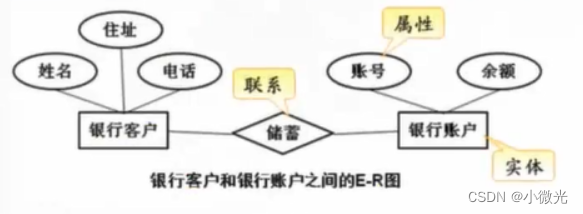
MySQL数据库
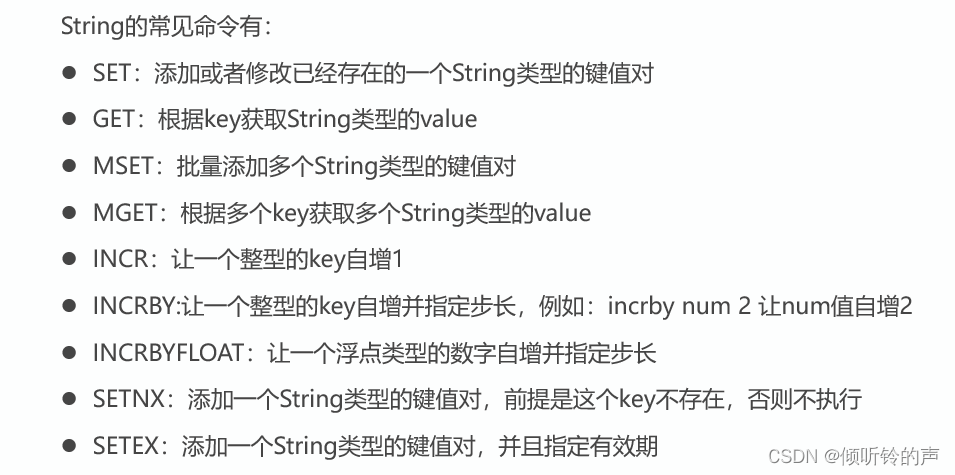
Dark Horse 2022 latest redis course notes and knowledge points (for interview)
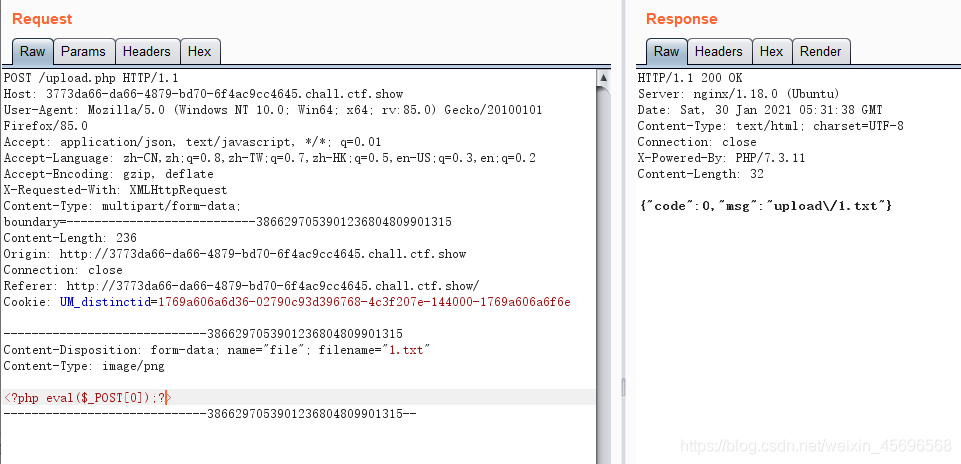
ctfshow-web入门 文件上传篇部分题解
正则表达式基础介绍
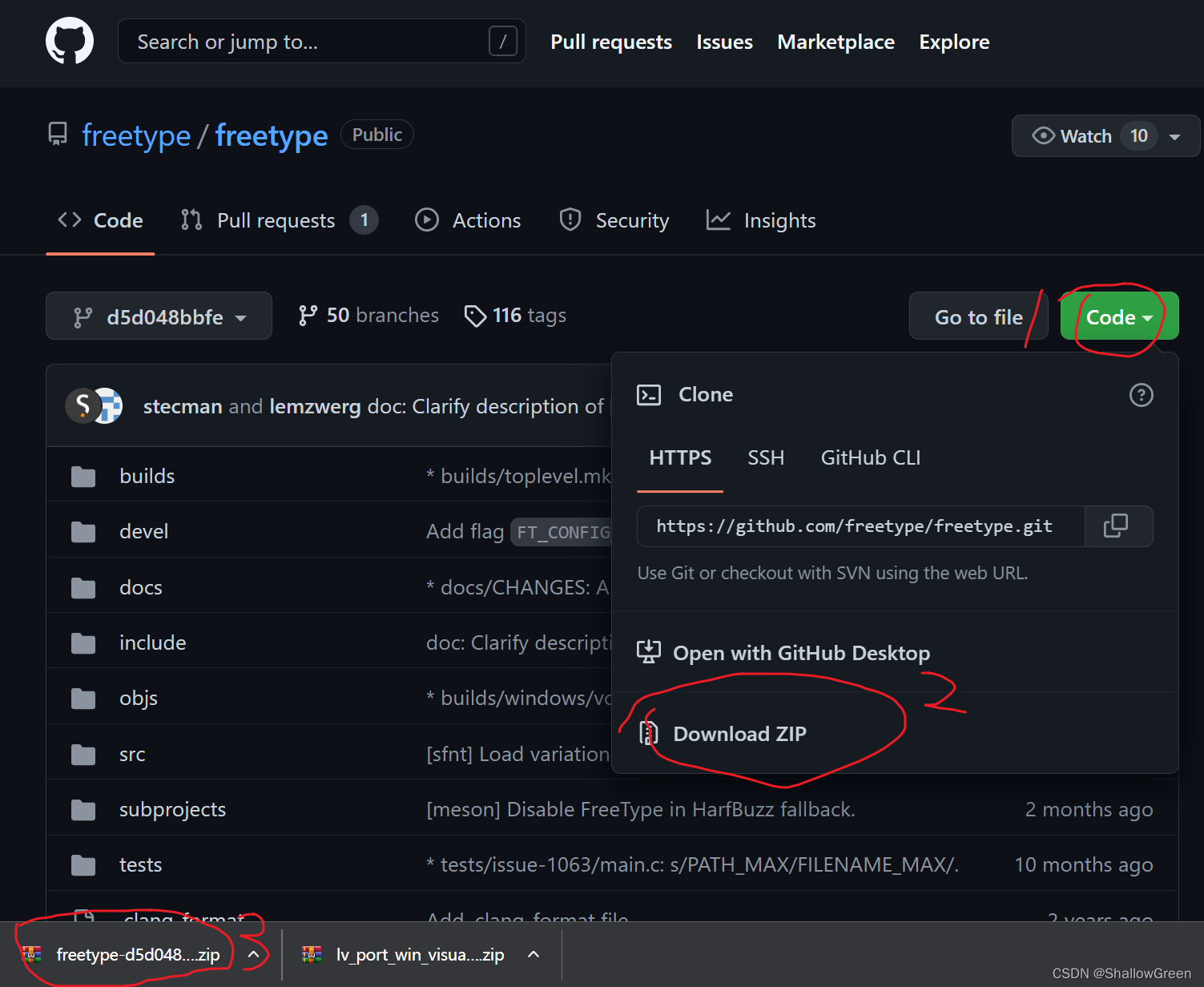
1. LVGL 8.3 在 Visual Studio 2019 模拟器中的环境搭建
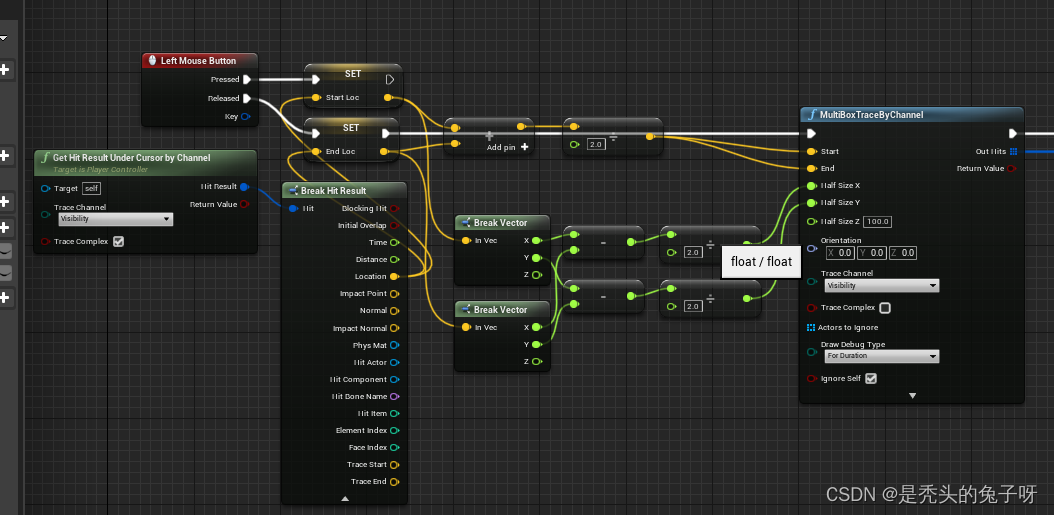
UE4 RTS 框选功能实现
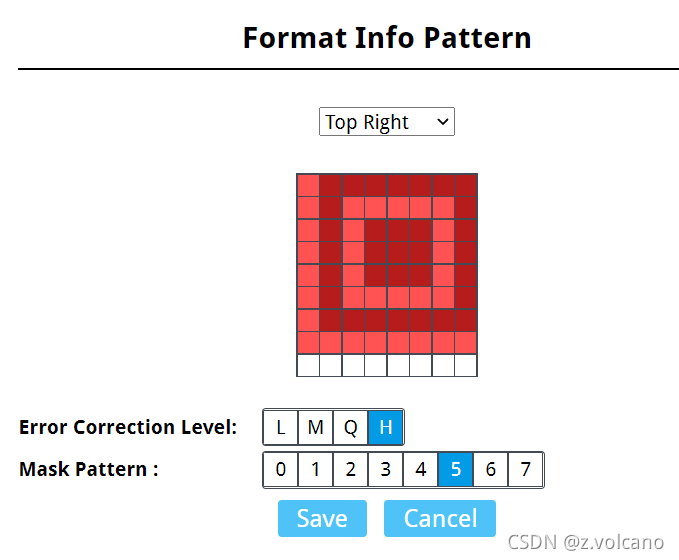
ctf misc 图片题知识点

Notes on OpenHarmony Open Source Meeting (Nanjing Station)

ASEMI整流桥GBJ810参数,GBJ810封装,GBJ810重量
随机推荐
requests之防盗链学习
磁盘管理与挂载
The Servlet,
elder blind date
Shell编程之循环语句与函数
Matlab, and nonlinear equations solving linear equations
数据解析之bs4学习
数据库中的操作(语法)
get一个小技巧,教你如何在typora写文章上传图片到博客上
LAN Technology - 6MSTP
The story of the disappearing WLAN of Windows 10 computers
PID控制电机输出作为电机PWM占空比输入的理解
204. 数素数
基于appinventor与EasyDL物体检测API的物体检测app
内存监控以及优化
The MySQL database
网络层协议介绍
Different styles of Flask-restful
Redis redis 】 【 the expiration of listening
IO byte stream reads text Chinese garbled