当前位置:网站首页>DAY25: Logic Vulnerability
DAY25: Logic Vulnerability
2022-08-10 08:32:00 【EdmunDJK】
DAY25: Logic Vulnerability
1. Introduction to Logic Vulnerabilities
Logic loopholes refer to the fact that some logic branches cannot properly handle or handle errors due to imprecise program logic or too complicated logic.In layman's terms: After a system has too many functions, it is difficult for program developers to think comprehensively, and there may be omissions in some places, or they may not be handled correctly, resulting in logical loopholes.Logic loopholes can also be said to be errors in the thinking of program developers and loopholes in the logic of program developers.
1.1, Vulnerability Type
(1) traversal
(2) Urban
(3) Payment
(4) Conditional competition
1.2, Features
Very hidden and dangerous
2, unauthorized vulnerability
2.1, Vulnerability Overview
Ultra vires is beyond the scope of authority or power.Most web applications have permission division and control, but if there are flaws in the design of permission control functions, attackers can use these flaws to access unauthorized functions or data, which is what we usually call ultra-privilege vulnerabilities.After the attacker oversteps his authority, he can perform some operations, such as viewing sensitive information, performing some operations such as addition, deletion, modification, and inspection.An unauthorized vulnerability is a very common logical security vulnerability.It is because the server side trusts the data operation request put forward by the client too much and ignores the judgment of the user's operation authority. As a result, modifying the relevant parameters can have the functions of adding, deleting, checking, and changing other accounts, resulting in an unauthorized vulnerability.
2.2, Vulnerability Type
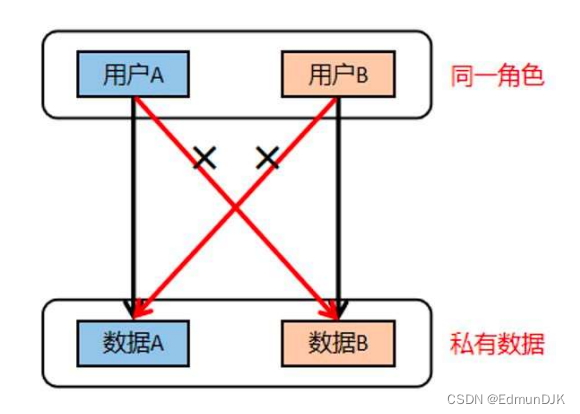
(1) Horizontal override
Refers to an attacker attempting to access a user resource that has the same permissions as him.
(2) Vertical override
Vertical override is a loophole caused by the design flaw of "URL-based access control". Vertical override can be divided into two types, namely upward override and downward override.

3. Payment loopholes
3.1, Vulnerability Overview
Payment loopholes are loopholes at the business logic level in the payment process of the system.There may be payment loopholes in all functions involving purchase, payment, etc.

You can also use some conditional competition or weak type comparison

4, verification code vulnerability
4.1, Vulnerability Overview
As a means of distinguishing between humans and machines, CAPTCHA plays an important role in the field of computer security.Without the verification code, attackers can illegally take over user accounts through brute force cracking, or perform arbitrary user registration on the website.The purpose of setting the verification code is to prevent automatic attacks, but if it is not designed well, it will be useless, so understanding the principle of verification code and the reasons for the loopholes will help to improve the security index of the website in a more comprehensive way
4.2. Mechanism of verification code
Step1: Client initiates a request
Step2: The server responds and creates a new SessionID and generates a random verification code
Step3: Return the verification code and SessionID to the client together
Step4: The client submits the verification code together with the SessionID to the server
Step5: The server verifies the verification code and destroys the current session and returns the result to the client
4.3, verification code classification
(1) Picture verification code
(2) SMS verification code
(3) Behavioral verification code
(4) Voice verification code
(5) Video verification code

4.4. Use of verification code
(1) The verification code can be blasted
(2) The verification code will be echoed back
(3) Fixed verification code
(4) The verification code can be guessed
(5) The verification code can be bypassed
(6) The verification code is invalid
(7) The verification code is generated and verified by the client
5, verification code vulnerability
(1) Use a strong verification code
(2) The verification code should not be generated by the client or returned to the client
(3) During development, the system pays attention to the verification and identification and destroys the verification code in the session
(4) Restricting the verification code submitted by the user cannot be empty, and the server will perform a secondary verification of the verification code on the mobile phone/email. Strong security verification code
(2) The verification code should not be generated by the client or returned to the client
(3) During development, the system pays attention to the verification and identification and destroys the verification code in the session
(4) The verification code submitted by the user is restricted from being empty, and the server performs a secondary verification on the verification code of the mobile phone/email
边栏推荐
猜你喜欢

Linux下载安装MySql

nrm 使用详解

同步锁synchronized追本溯源

NPU architecture and force analysis

J9数字论:关于DAO 特点的宏观分析

Uni-app develops WeChat applet using local images as background images

Relaxation class: the boss will martial arts, who also can not hold up against!The charm of six sigma training
解决win10win7win8系统找不到指定的模块,注册不了大漠插件的问题
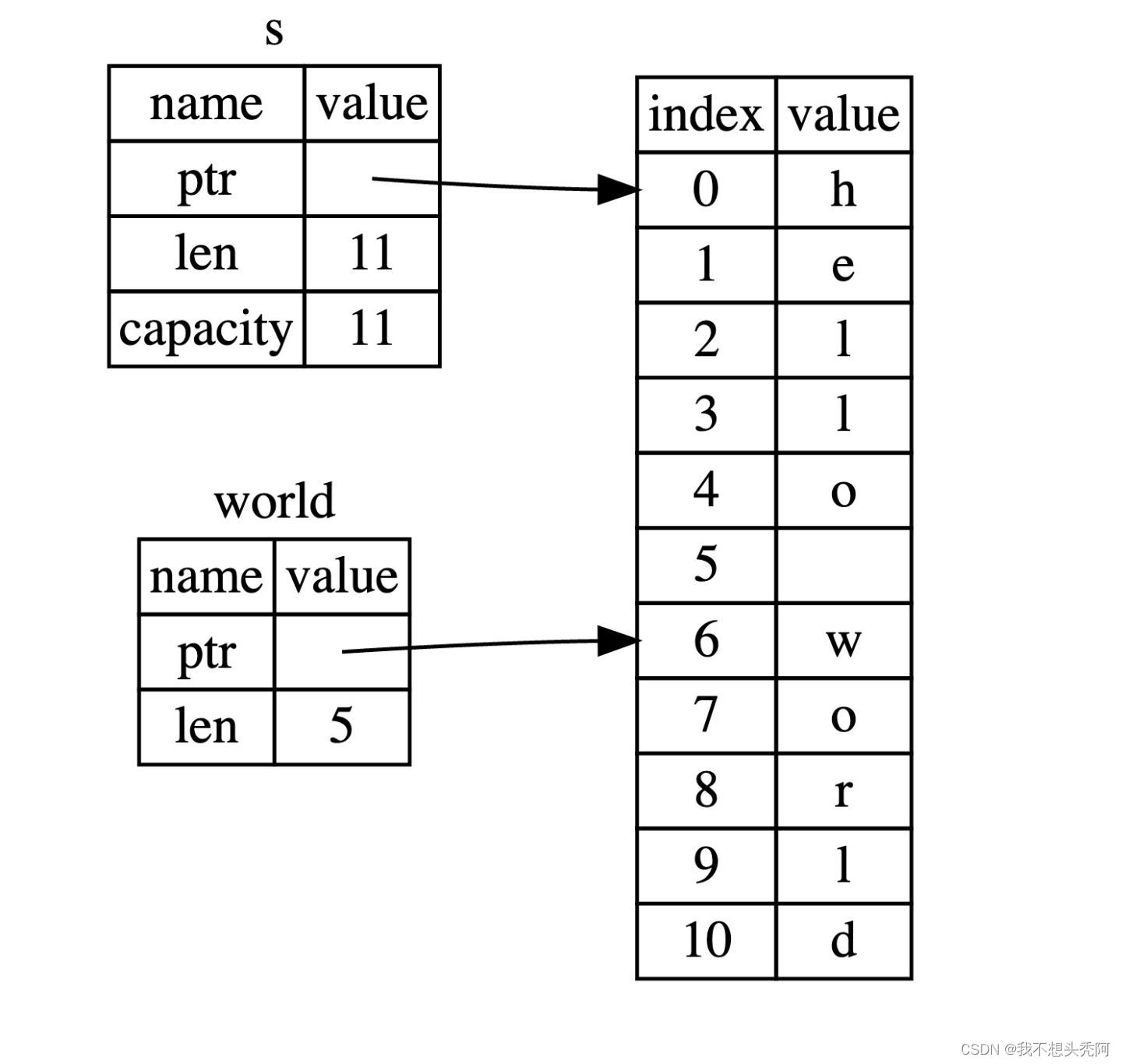
Rust learning: 6.1_Slices of composite types

How AliExpress sellers seize product search weight
随机推荐
Rust learning: 6.5_Array of composite types
The implementation of the seemingly useless component (text gradient) in NaiveUI is so simple
菜鸟、小白在autojs和冰狐智能辅助之间如何选择?
本地生活商家如何通过短视频赛道,提升销量曝光量?
短视频同城流量宣传小魔推有何优势?如何给实体商家带来销量?
js--------对象数组转换成二维数组(excel表格导出)
怎么使用【jmeter正则表达式提取器】解决返回值作参数的问题
详解构建mock服务最方便的神器——Moco
深度剖析“八大排序”(上)_ 探寻一些不为人知的细节
Day37 LeetCode
Different command line styles
It is obvious that a unique index is added, why does it still generate duplicate data?
UGUI—事件,iTween插件
1499. The maximum pile.then/deque
Spotify expresses its architectural design using the C4 model
速卖通卖家如何抓住产品搜索权重
Uni-app开发微信小程序使用本地图片做背景图
Unity—UGUI控件
明明加了唯一索引,为什么还是产生重复数据?
物联网时代下的网络整合推广外包精准化效果-深圳双赢世讯