当前位置:网站首页>About CC Attacks
About CC Attacks
2022-08-11 04:56:00 【Zhongyun Era-Defense Testable-Xiaoyu】
CC attack has certain concealment, so how to determine whether the server is suffering or has been attacked by CC? The following three methods can be used to determine it.
1. When the command line method is generally attacked by CC, the Web server will be closed to the outside world on port 80, because this port has been blocked by a large amount of junk data, and the normal connection will be terminated.It can be viewed by entering the command netstat -an on the command line. "SYN_RECEIVED" is the TCP connection status flag, which means "is in the initial synchronization state of the connection", indicating that the handshake response cannot be established and is in a waiting state.This is the characteristic of an attack. In general, there are many such records, indicating attacks from different proxy IPs.
2. Batch method The above method requires manual input of commands and if there are too many IP connections to the Web server, it seems to be laborious. You can create a batch file and use the script code to determine whether there is a CC attack.The script filters out all current connections to port 80.When you feel that the server is abnormal, you can double-click to run the batch file, and then check all connections in the open log.log file.If the same IP has more connections to the server, it can basically be determined that the IP is performing a CC attack on the server.
3. View system logs Web logs are generally located in the C:\WINDOWS\system32\LogFiles\HTTPERR directory, and a log file similar to httperr1.log is used in this directory. This file is a record of web access errors.The administrator can select the corresponding log to open according to the log time attribute to analyze whether the Web is attacked by CC.
By default, there are not many items recorded in the Web log. You can set it through IIS to allow the Web log to record more items for security analysis.The operation steps are: "Start→Administrative Tools" to open "Internet Information Server", expand the item on the left to locate the corresponding Web site, then right-click and select "Properties" to open the site properties window, under the "Website" tabClick the "Properties" button, and under the "Advanced" tab of the "Logging Properties" window, you can check the corresponding "Extended Properties" to allow Web logs to be recorded.For example, the three items of "bytes sent", "bytes received", and "time used" are not selected by default, but they are very useful in recording and judging CC attacks and can be selected.In addition, if you have high security requirements, you can set the "New Log Schedule" under the "General" tab to log it "hourly" or "every day".In order to determine the time for future analysis, you can check the "Use local time for file naming and creation".
边栏推荐
- Snap - rotate the smallest number of an array
- [FPGA tutorial case 50] Control case 2 - FPGA-based PD controller verilog implementation
- Dry goods: The principle and practice of server network card group technology
- 交换机和路由器技术-26-OSPF末梢区域配置
- 0 Basic software test for career change, self-study for 3 months, 12k*13 salary offer
- send_sig: 内核执行流程
- 如何缓解压力、拒绝内耗【1】
- FPGA工程师面试试题集锦111~120
- 3 模块二:科研工具使用
- The sword refers to offer_abstract modeling capabilities
猜你喜欢

Self-research capability was recognized again, and Tencent Cloud Database was included in the Forrester Translytical report

Embedded Sharing Collection 33

C语言:实用调试技巧

C语言题解:谁是凶手!
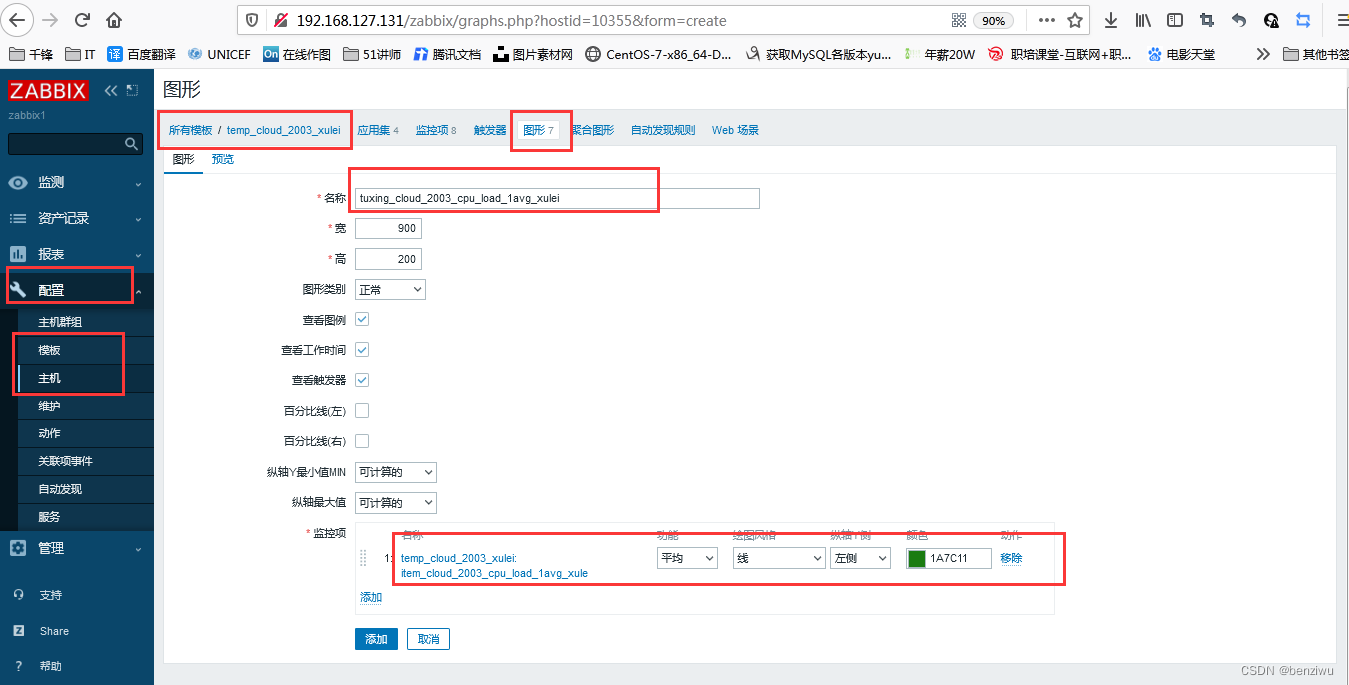
zabbix构建企业级监控告警平台
![ERROR: Could not install packages due to an OSError: [Errno 2] No such file or directory: '/data/xxxx](/img/02/3896b29a955ae84a0f0326f0d2cabf.png)
ERROR: Could not install packages due to an OSError: [Errno 2] No such file or directory: '/data/xxxx

交换机--- 生成树--三层架构总结

交换机和路由器技术-30-标准ACL

【电商运营】社交媒体营销策略该如何制定?

0基础转行软件测试,自学3个月,浅拿12k*13薪offer
随机推荐
Summary of c language fprintf, fscanf, sscanf and sprintf function knowledge points
The basics of binary heap~
vector中resize() 用法排坑
Research on a Consensus Mechanism-Based Anti-Runaway Scheme for Digital Trunking Terminals
svg-icon的使用方法(svg-sprite-loader插件)
网络协议1
Selenium自动化测试框架工作原理你明白了吗?
Zabbix builds enterprise-level monitoring and alarm platform
梅克尔工作室--OpenEuler培训笔记(1)
leetcode 9. 回文数
增加PRODUCT_BOOT_JARS及类 提供jar包给应用
项目实战第二十七讲:状态模式在重名品牌中的应用
Switches and routers technologies - 30 - standard acls
JwsManager service interface implementation class - the jni implementation
Apache初体验
走出迷宫的最短路径
CAD2020 打开错误报告 e06d7363h Exception at 13644F69h
交换机和路由器技术-36-端口镜像
map and set - natural search and lookup semantics
form表单提交数据库中文变成问号