当前位置:网站首页>On World Book Day, Tencent safety recommends a charging book list
On World Book Day, Tencent safety recommends a charging book list
2022-04-23 22:06:00 【Tencent security】
Today is world reading day , Tencent security and wechat reading 、 Tencent research institute , Recommended a charging book list .
This book list interviewed many leaders of Tencent security Joint Laboratory 、 Experts from Tencent Research Institute 、 Tencent security experts and industry experts , Hope to help network security enthusiasts and practitioners learn better 、 Understand the world of cybersecurity .
The private book list of the head of the laboratory
Safety is a martial art , Only hand ripe ; Safety is a philosophy , It needs thinking . Safety is a painter , Using Tao to control skills ; Security is a game , Test logic .
What books does the head of Tencent security joint laboratory usually read ? What are the private book lists and recommendations ? Let's take a look at it today !
References : Wu Shi Head of Tencent security Cohen Laboratory
Recommended books 1:《CTF Competition authority guide 》
Recommended reasons : Before the book was published , Several small partners in Cohen lab participated in the review , I think the quality of this book is very good , The threshold for entry is relatively low , Logic and writing are also good , Of course, a small part of the content is a little outdated now . In most people's eyes , Hackers seem to be Wulin experts , Can easily take people " chopped-off head " Thousands of miles away . After reading this book, you will understand , So-called “ Hacker's peerless martial arts ” It can be learned , It's a technology ,“ Only hand ripe ” nothing more . For practical technology , Of course, the most important thing is to practice , It's no use just reading , The gap between the so-called master and the low hand is here .
Recommended books 2:《 What philosophers have done 》
Recommended reasons : This book is very interesting , A relatively complete introduction to the influential philosophical schools in the whole world and their origin and development , The language is humorous , It belongs to the kind of book that can't stop reading . Classical philosophy is similar to theology , There is no logic , But by the mathematician Descartes and beyond , Philosophy seems to have become a branch of Mathematics , From different postulates 、 Start with justice , Through rigorous logical reasoning, we can establish a completely different world outlook and outlook on life , And it is logically self consistent , This is very fascinating . This book can be used as an introductory book for friends who want to know the answers to the three major questions of life , It's worth taking some time to appreciate .
References : Yu Min Head of Tencent security Xuanwu Laboratory
Recommended books 1:《Python Black hat : Hacking and penetration testing programming ( The first 2 edition )》
Recommended reasons : The book translated by the students of Xuanwu laboratory has been published recently . This book is written with Python As a clue , In the process of introducing the implementation methods of various blue army tools , Guide readers to learn various blue army technologies , as well as Web/ System / Basic knowledge related to network . So the biggest feature of this book is that it is not boring , It is very suitable as an introductory learning material for the blue army's technical direction .
Recommended books 2:《 Formal logic 》
Recommended reasons : Logic is the element of constructing thought , Is a tool to understand the world , It is the basis of effective communication . If there is a multiverse , Then the physical laws of different universes may be different , But the logic is probably the same . Unfortunately, most people have not received systematic logic education . This book is very classic , It's not hard to understand . Read it , There must be gains .
References : Ma Jinsong Head of Tencent security anti-virus Laboratory
Recommended books 1:《Windows Programming Apocalypse 》
Recommended reasons : This is a book about Windows strange stories 、 A collection of essays related to program development 、 Miscellany , Told a lot of interesting stories and technical details , For example, what deceptive methods developers will use to obtain the driver's WHQL authentication . Another section is about ExtTextOut Function to draw a solid rectangle , Speed super fast , It is interesting to …… The author's blog is always updated , Will discuss Windows The latest technical problems of development , Recommended attention .
Recommended books 2:《 The great Chinese industrial revolution 》
Recommended reasons : Not too much of a title ! Just read the preface , Can stimulate a strong interest in reading . The book was finished in 2015 year , Data up to 2014 end of the year , It has its historical background , As for the connection with the current economy and society , That's a matter of opinion . This book has a strong academic flavor , The textual research is detailed , Rigorous discussion , But for ordinary readers , Some places read too long , Suggest combining your own interests , Choose its outline .
References : Yang Qing Head of Tencent security Tianma Laboratory
Recommended books 1:《 Hackers and painters 》
Recommended reasons : Recommend this book that seems to have nothing to do with network security technology , Because it leads to the important endowment of network security attack and defense confrontation from a unique perspective - creativity , I hope it can inspire and urge everyone to think independently Hack The essence of , Just like we practice the digital world every day “ A martial art ” At the same time, we are also exploring “ Martial arts ” equally , Using Tao to control skills , The art must be accomplished , The art of departing from the Tao , The art will fail . Want to make continuous breakthroughs in the field of Technology , Just like Picasso , Understand the rules and then break the rules .
Recommended books 2:《 Lifelong growth 》
Recommended reasons : This book can make lifelong growers find some resonance , When we are determined to be outstanding , We have to work harder 、 Work harder 、 The motivation to become smarter and stronger . The brain changes like a muscle , The more you use it , The stronger it becomes . So when you study , The brain will grow and become stronger . I hope you can use growth thinking to drive the continuous improvement of your mind and body , adopt Hack Reach a higher level in your own way .
A selection of books by security experts
Cyber security people are waiting to defend security , It's normal . But there are always people who find time to work hard , Learn from books and recharge yourself .
What books do network security practitioners and experts from all walks of life usually read ? A charging book list for everyone . There are technology and dry goods , There is also logic and thinking , And the anecdotes of the safety circle .
《 code - Language hidden behind computer hardware and software 》
This book starts with childhood games , Step by step , It introduces the basic knowledge of the computer world in simple terms , Both interest and knowledge , Is everyone who wants to have an in-depth understanding of the information world IT Interesting reading materials that must be read by technical practitioners .—— Tencent security Yunding lab Li Bin
《 civilization 、 modernization 、 Value investment and China 》
The intervention of modern science and technology has accelerated the evolution and perfection of free competitive market , Modern civilization 3.0 That is, the stage of scientific and technological civilization led by the industrial revolution . The author also analyzes the relationship between China and the United States from the perspective of the history of civilization , It also predicts the evolution process of China's future modernization .—— Tencent research institute Liu Qiong
《 Stupid Psychology 》
To be exact, it's about how to identify stupidity 、 A pamphlet to prevent stupidity , Gathered dozens of journalists and scholars' cynicism about all kinds of people and things , Of course, there is ubiquitous self mockery . But books with too many golden sentences , There is also a problem , The mark can't be made .—— Tencent research institute Zhou Zhenghua
《 Brief history of safety 》
Security is a low-key and mysterious field , How to use easy to understand language , Clever and appropriate metaphor makes the obscure principle clear 、 Be thorough , It needs more than just language skills , There is also in-depth understanding and practical experience of security and Technology .《 Brief history of safety 》 The first taste is interesting , Then taste it into the heart , It's worth recommending .—— Tencent research institute Zhai you
《 Silicon Valley growth hackers practical notes 》
Put the book C End 、B The playing methods of end growth hackers are systematically expounded , Count as SaaS An introduction to growth , Gave the team a lot of inspiration .—— Tencent security expert Dong Wenhui
《Google System architecture decryption : Build a safe and reliable system 》
Google security team's design of the system 、 structure 、 Share safety practices in maintenance , Translation from Tencent security experts , And now DevSecOps The idea is to fit , It is worth learning and reference for relevant practitioners and enthusiasts .—— Tencent security Yunding lab Zhang Zuyou
《 Social engineering : Human vulnerability in the security system 》
Science and technology are always used and driven by mankind , How can we understand the loopholes of human nature ?—— Tencent security expert Li Guanghui
《 The underlying logic 》
Empathy is the way to alleviate the root causes of all contradictions , With whom , You have his knowledge . The red and blue Legion often mentioned in network security , Through countless attack and defense drills , To seek knowledge is to win a hundred battles .—— Tencent security expert Wang Yu
《 The principle of everything 》
While warning us to fear the richness of the universe , Abandon old instincts , In order to obtain “ be reborn ” The thinking of .
《 From one to infinity 》
This book can let a beginner see that science is not superior , And let ordinary people understand science , Is one of the missions of a scientist .
《 Cognitive Awakening : Start the driving force of self change 》
It is true that social development has its own rules , But your personal behavior will be transferred by will .
《 Limited and infinite games : The competitive world in the eyes of a philosopher 》
Only with intelligence can we constantly break 、 Expand the invisible boundaries you have created , Is the real event player .
Network security is changing with each passing day , Maybe reading is not the only way to improve yourself , Really enrich yourself 、 A great way to build thinking . I hope this list , Can give you different inspiration . today , You might as well pick up your books , Enjoy reading .
版权声明
本文为[Tencent security]所创,转载请带上原文链接,感谢
https://yzsam.com/2022/113/202204232200126250.html
边栏推荐
- Unity制作一个小星球
- JUnit unit test ---- a good tool for testing a single method
- [leetcode sword finger offer 58 - I. flip word order (simple)]
- 降级和熔断总结
- Lightweight project management ideas
- 资本追逐Near生态
- Database experiment VI integrity language experiment
- 2022-04-24日报:在生物科学领域应用深度学习的当前进展和开放挑战
- Opening conditions and process of hystrix circuit breaker and default alternative treatment
- consul 开启健康监控检查
猜你喜欢
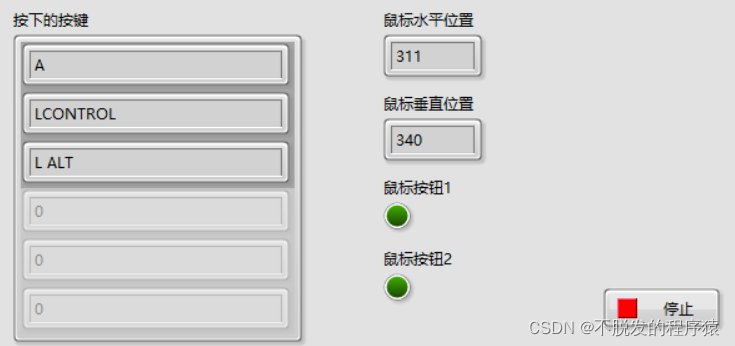
LabVIEW采集鼠标、键盘数据
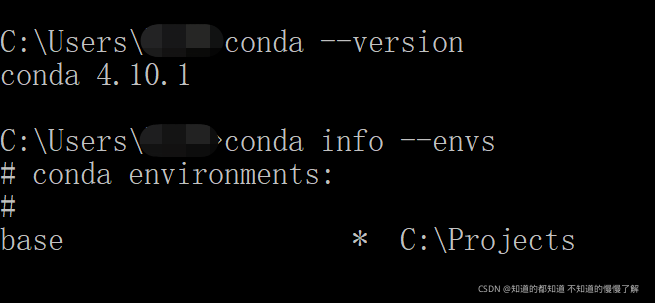
Pytorch installation (personal records)
![[leetcode refers to offer 25. Merge two sorted linked lists (simple)]](/img/7b/b31b1a128e8b48c56493131e0f26c5.png)
[leetcode refers to offer 25. Merge two sorted linked lists (simple)]
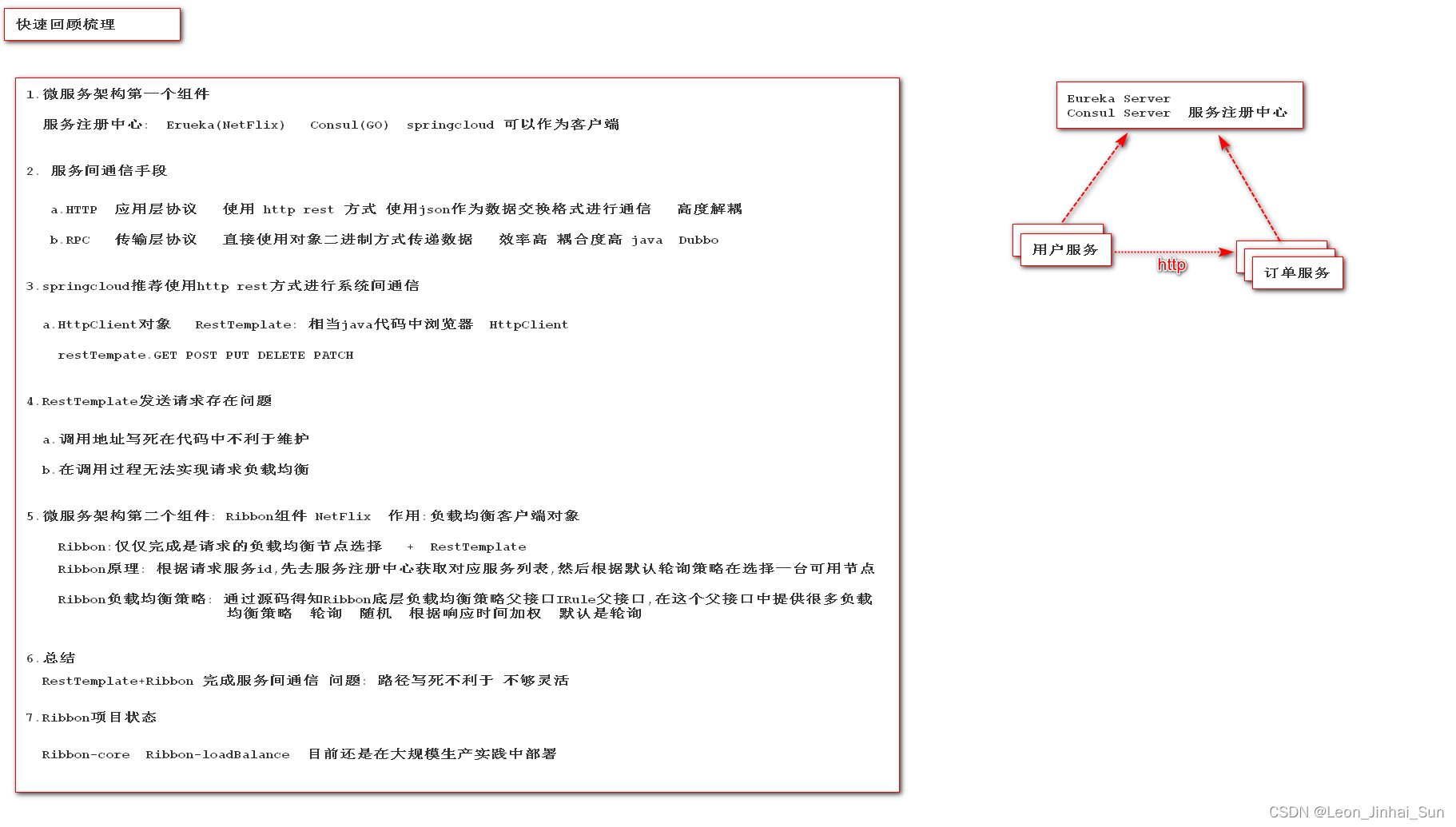
服务注册中心和Ribbon组件回顾
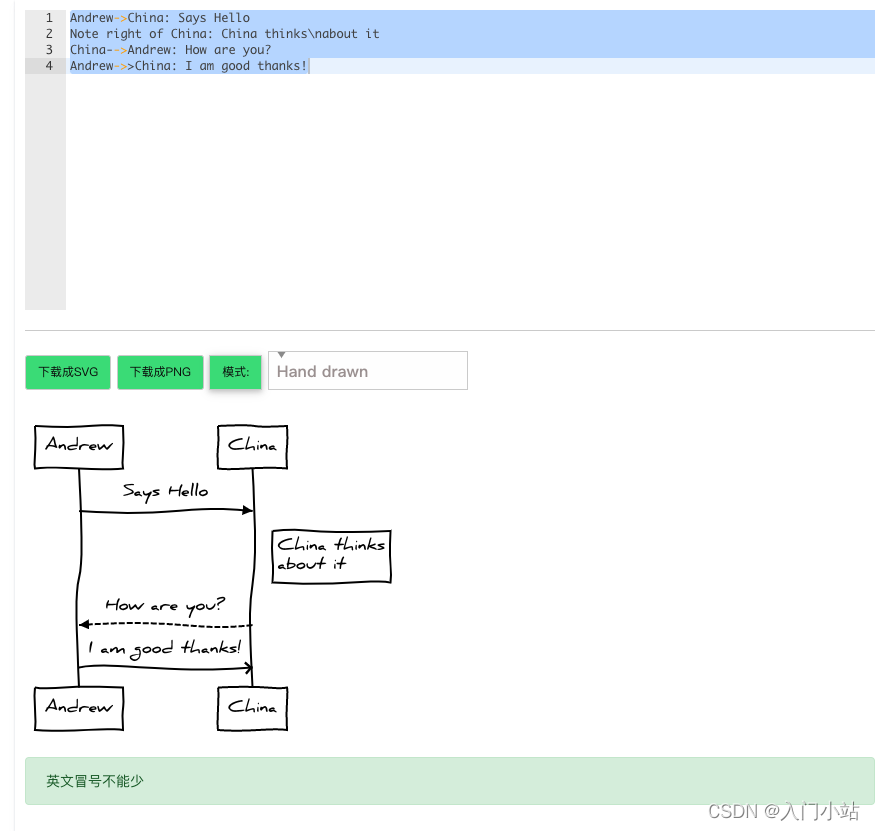
在线时序流程图制作工具
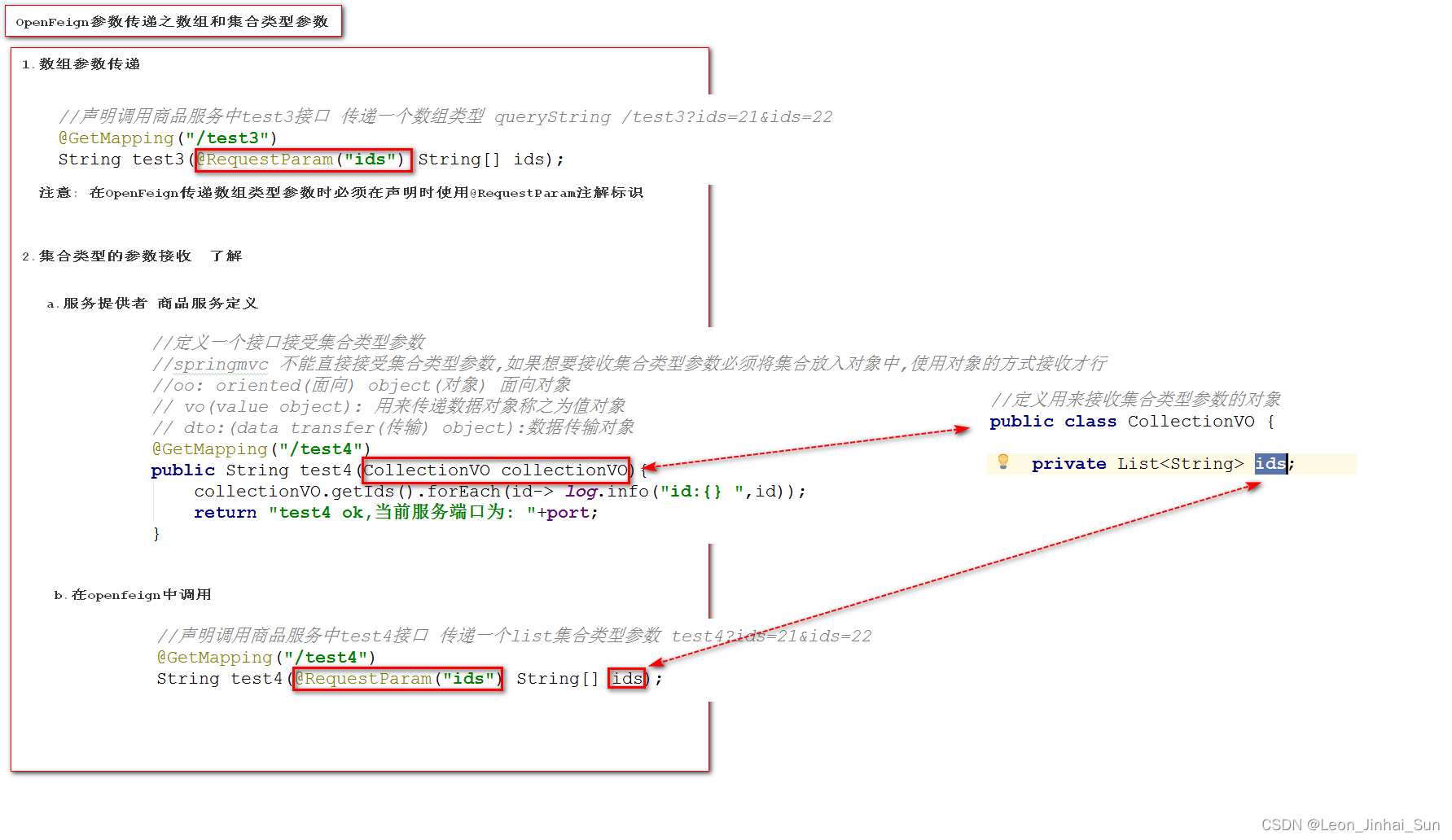
OpenFeign的参数传递之数组和集合类型
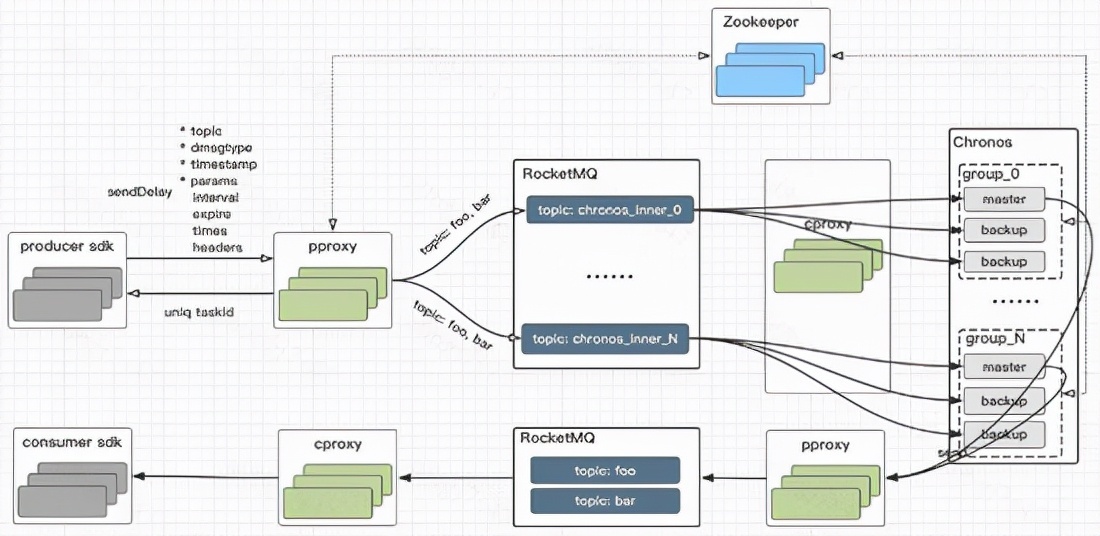
Common implementation schemes of delay message

LabVIEW modify the appearance of the application window
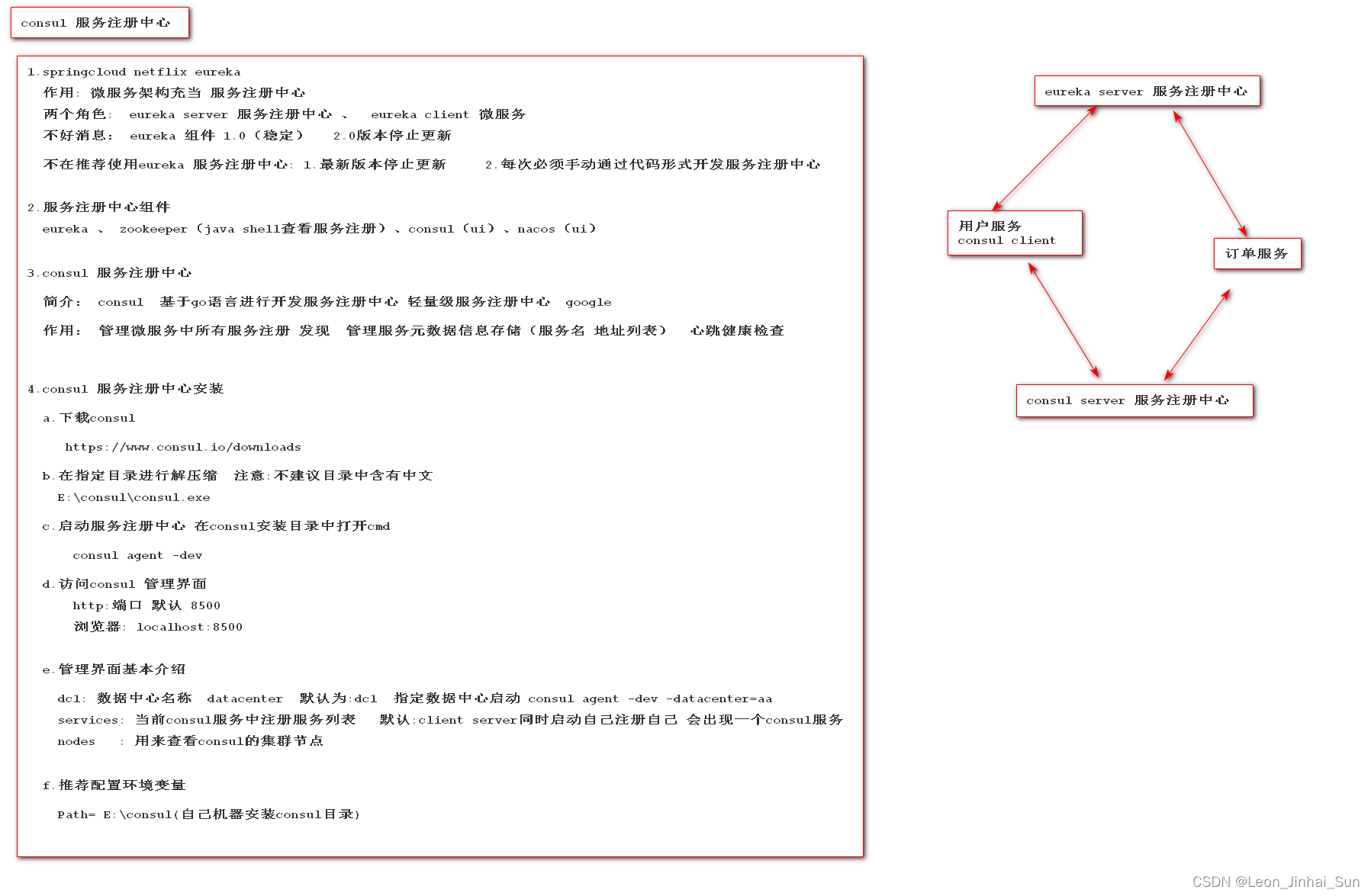
consul server 服务注册中心安装
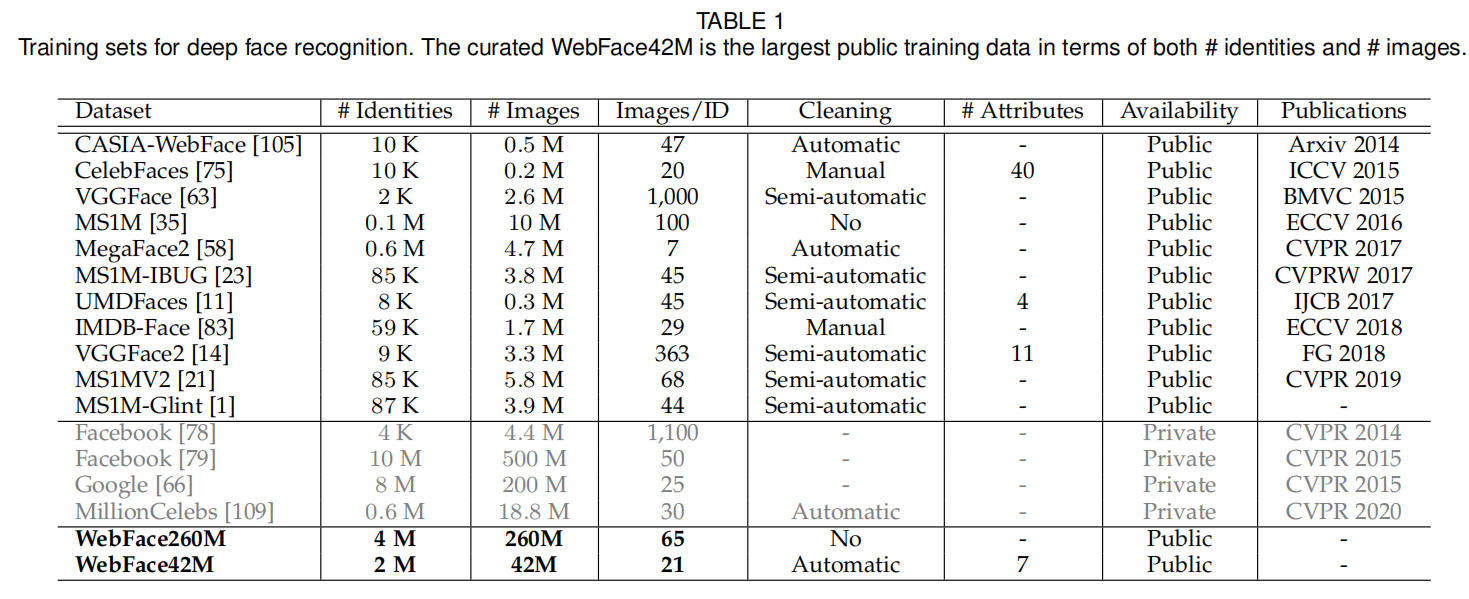
Tsinghua University | webface260m: benchmark for million level deep face recognition (tpami2022)
随机推荐
服务间通信方式
Pytorch installation (personal records)
JUnit unit test ---- a good tool for testing a single method
轻量化项目管理思路
三、zygote启动流程
LabVIEW采集鼠标、键盘数据
Swift import third-party library reports an error no such module““
Hystrix components
Introduction to hystrix and implementation of server fuse
Pytorch deep learning practice (2)
[leetcode sword finger offer 10 - II. Frog jumping steps (simple)]
Keras. Layers introduction to various layers
2022-04-24日报:在生物科学领域应用深度学习的当前进展和开放挑战
JS merge duplicate data in array object
Common implementation schemes of delay message
RestTemplate 服务调用
Hystrix组件
Tsinghua University | webface260m: benchmark for million level deep face recognition (tpami2022)
MySQL back to table
On nanopi M1 (Quanzhi H3) kernel driver programming HelloWorld (compilation mode I)