当前位置:网站首页>SSH connects to the remote host through the springboard machine
SSH connects to the remote host through the springboard machine
2022-04-23 15:05:00 【Shibao】
There are two ways to choose , Include ProxyJump and ProxyCommand .
ProxyJump It is in the form of port forwarding , The springboard machine is required to support port forwarding .
ProxyCommand It's through SSH Protocol forwarding
In terms of security ,ProxyJump It's higher , Because it's end-to-end encryption , The springboard machine only does forwarding through transmission , Maybe the performance is also good .
Here are two examples , This includes transit through multiple springboards and login with certificates ,Host1 The certificate of the local user has been preset ( This is also the usual way ), By modifying the profile .ssh/config Realization :
Host Host1
HostName 192.168.0.1
Port 22
User yourusername
Host Host2
HostName 192.168.0.2
Port 22
User yourusername
IdentityFile ~/xxx.pem
ProxyJump Host1
Host Host3
HostName 192.168.0.3
Port 22
User yourusername
IdentityFile ~/xxx.pem
ProxyJump Host2
Host Host1
HostName 192.168.0.1
Port 22
User yourusername
Host Host2
HostName 192.168.0.2
Port 22
User yourusername
IdentityFile ~/xxx.pem
ProxyCommand ssh Host1 -W %h:%p
Host Host3
HostName 192.168.0.3
Port 22
User yourusername
IdentityFile ~/xxx.pem
ProxyCommand ssh Host2 -W %h:%p
版权声明
本文为[Shibao]所创,转载请带上原文链接,感谢
https://yzsam.com/2022/04/202204231408547389.html
边栏推荐
- 3、 Gradient descent solution θ
- async void 导致程序崩溃
- UML学习_day2
- Do (local scope), initializer, memory conflict, swift pointer, inout, unsafepointer, unsafebitcast, success
- Ffmpeg installation error: NASM / yasm not found or too old Use --disable-x86asm for a clipped build
- Basic operation of sequential stack
- 小红书 timestamp2 (2022/04/22)
- Detailed explanation of C language knowledge points - data types and variables [2] - integer variables and constants [1]
- Bingbing learning notes: take you step by step to realize the sequence table
- 你還不知道責任鏈模式的使用場景嗎?
猜你喜欢

LeetCode165-比较版本号-双指针-字符串
Reptile exercises (1)
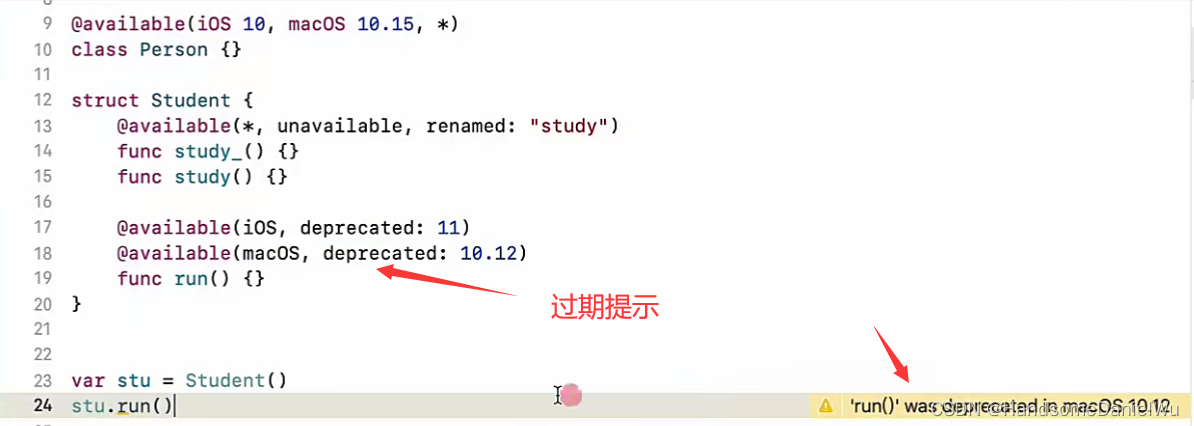
OC to swift conditional compilation, marking, macro, log, version detection, expiration prompt
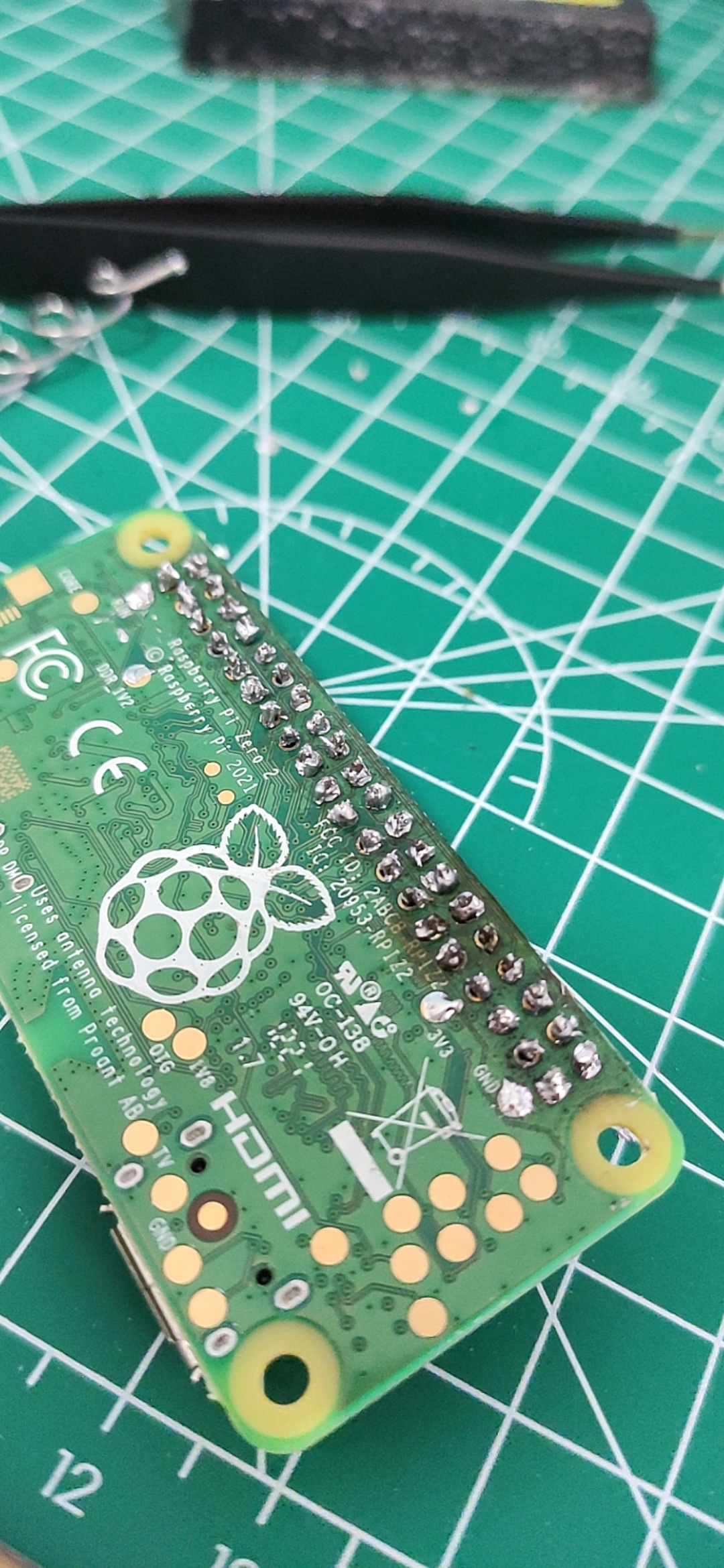
My raspberry PI zero 2W tossing notes record some problems encountered and solutions
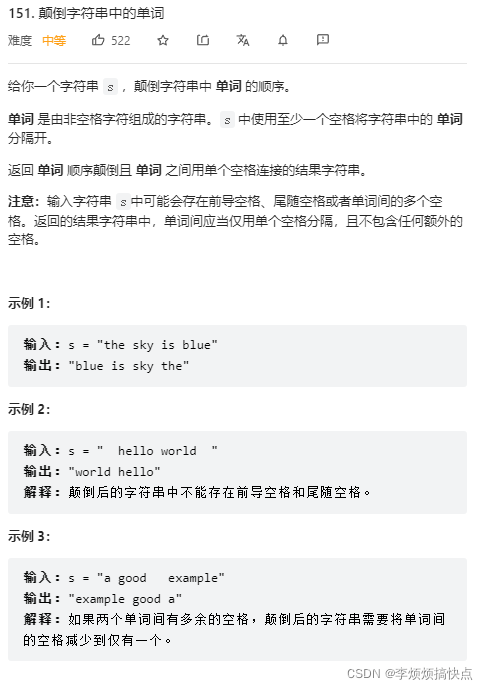
LeetCode151-颠倒字符串中的单词-字符串-模拟
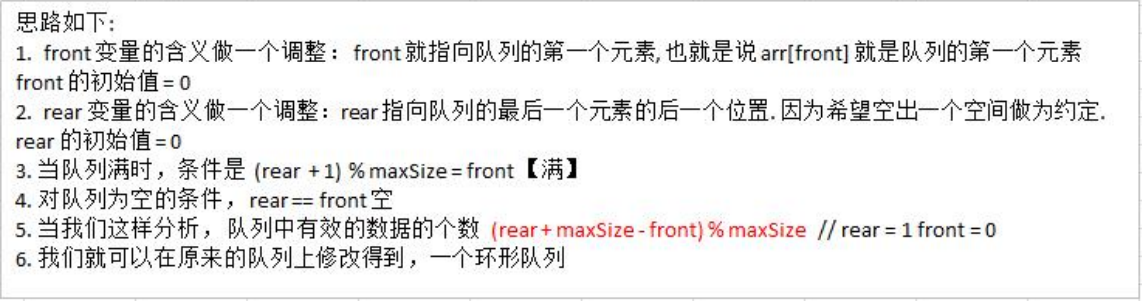
Advanced version of array simulation queue - ring queue (real queuing)

What is the effect of Zhongfu Jinshi wealth class 29800? Walk with professional investors to make investment easier

中富金石财富班29800效果如何?与专业投资者同行让投资更简单

Mds55-16-asemi rectifier module mds55-16
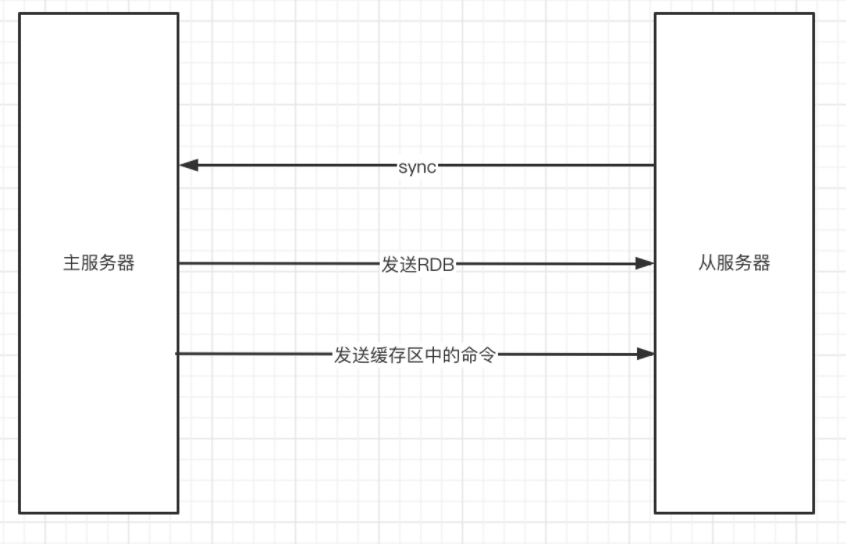
Redis master-slave synchronization
随机推荐
2-GO variable operation
如何设计一个良好的API接口?
Alexnet model
SQLSERVER事物与锁的问题
分布式事务Seata介绍
C语言超全学习路线(收藏让你少走弯路)
Epolloneshot event of epoll -- instance program
The life cycle of key value in redis module programming
Redis master-slave synchronization
[NLP] HMM hidden Markov + Viterbi word segmentation
你還不知道責任鏈模式的使用場景嗎?
Tencent has written a few words, Ali has written them all for a month
8.5 concise implementation of cyclic neural network
Basic operation of sequential stack
The win10 taskbar notification area icon is missing
How to write the keywords in the cover and title? As we media, why is there no video playback
买卖股票的最佳时机系列问题
LeetCode151-颠倒字符串中的单词-字符串-模拟
Leetcode151 - invert words in string - String - simulation
博睿数据携手F5共同构建金融科技从代码到用户的全数据链DNA