当前位置:网站首页>Thoughts on Technology Sharing
Thoughts on Technology Sharing
2022-08-10 18:18:00 【51CTO】
Story Reason
Tell a story about yourself, at the request of netizens, help him find a person who has had financial transactions with him through Alipay, and there may be some disputes later,I don't know the specific reason, but his request is: can the mobile phone number of the other party be queried through the transfer record on Alipay.
Due to Alipay's privacy mechanism, if the other party's mobile phone number does not exist in your mobile phone address book, you will not be able to see the other party's full mobile phone number, only the first threeThe first and last two digits, you can see the other party's avatar and nickname when transferring money. When the amount is relatively large, you can still know the other party's name, but you can't see the complete 11-digit mobile phone number
In the above paragraph, there areA very important implicit condition, the other party's mobile phone number is stored in your mobile phone address book, then I can see his complete number through Alipay!
This piqued my interest and thought I could try it, because the idea is to revolve around the above mechanism, the problem will be simplified to add all possible numbers to my mobile communicationrecord.
How do I find all possible numbers?The simple and rude thing is to list all the default 6-digit numbers in the middle in the form of permutation and combination. Anyone who has learned point permutation and combination knows that there are ten possibilities of 0-9 for each digit of 6 digits.There are 10 to the 6th power, that is, one million kinds... Even if it can be listed, the mobile phone will have to explode. Does it have such a large capacity to store 1 million numbers?
The problem has become to narrow the scope as much as possible, not to mention too detailed, for fear of being used by people with ulterior motives.
Then is to use the code to generate all possible numbers, the problem becomes how to import the generated mobile phone number into the mobile phone, this is another problem, I still use the code to solve, and don't say too much, for fear of being used by people with ulterior motives.
As a result, I finally found it for him.
But I'm going to say two other things:
General ideas for problem solving:
When you face a problem, you must first focus on the final result, propose solutions around the final result, and be able to propose a solution, indicating that the problem is theoretically solvable, otherwise there is no feasibility; then gradually dissect the problem around the solution, decompose the transaction into the most basic components, and use various methods to solve every problem in the process of decomposition. The final result in the case is found through Alipay.Someone's number, the solution is to use Alipay's mobile phone address book to add friends, the problem becomes adding the other party's number to the address book, the premise of adding is to get the number, the solution to get the number isViolent traversal, but after analyzing too many violent traversal results, it is almost unfeasible, the problem becomes how to reduce the traversal results, the solution to this problem is *****************Narrowing down the scope, this solution can be implemented after optimization. It can be done with three or two clicks of the code, and a bunch of numbers are obtained. The problem arises again. How to quickly import thousands of numbers into the mobile phone?Think about this problem and find a solution. In short, under the guidance of this kind of thinking, you will be able to slowly approach the final goal.
Consequences of Technology Abuse
In the end, I helped that person achieve his goal. I wanted to record the complete process and share it with everyone, but I thought that if this solution was used by people with ulterior motives,Wouldn't that be a trick of the tiger and help the tyrant to abuse it? This goes back to the old-fashioned question, technology is not guilty of human beings, any technology is neutral, and what it is used for depends on people. Angels can be used to create heaven, and devils can be used to create nightmares.
Summary
Influenced by open source culture, sharing is the virtue of programmers, but for technology sharing, you should be more careful, so as not to be used for evil without your knowledge.
The three views are the same, yes
边栏推荐
- 【ARK UI】HarmonyOS ETS的引导页的实现
- Selenium - 如何使用隐式、显示、强制元素等待?
- 【图像分割】基于元胞自动机实现图像分割附matlab代码
- 【图像去雾】基于颜色衰减先验的图像去雾附matlab代码
- 微服务架构-实现技术之六大基础组件:服务通信+事件驱动+负载均衡+服务路由+API网关+配置管理
- 【FAQ】HarmonyOS ETS如何给组件设置边框
- 【接入指南 之 直接接入】手把手教你快速上手接入HONOR Connect平台(下)
- 【快应用】如何使用命令打包快应用rpk
- Toronto Research Chemicals 双(乙酰丙酮)铂(II)
- WebRTC source code analysis nack detailed explanation
猜你喜欢
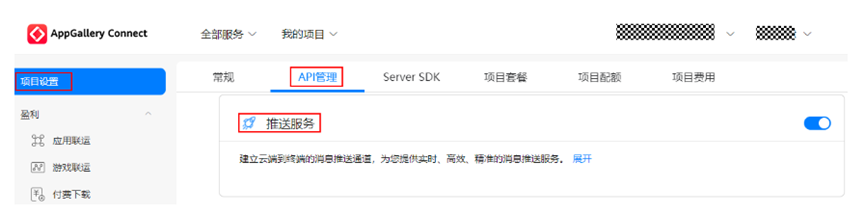
【HMS core】【FAQ】Account Kit、push Kit典型问题合集1
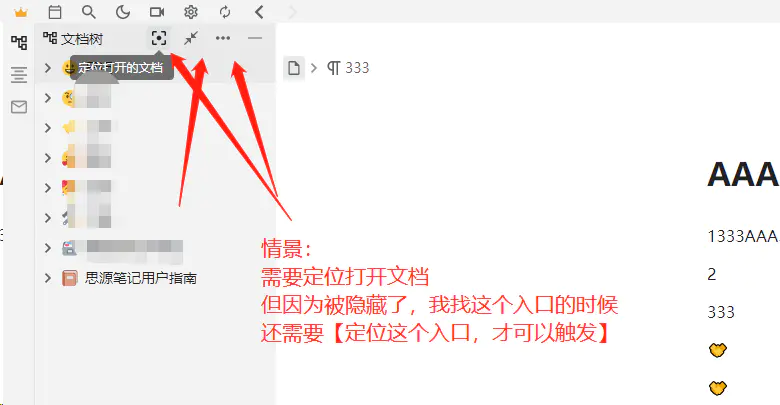
忍不住 - 发个新帖子【为什么把红圈的功能入口隐藏?需要移动到鼠标到位置驻停才显示?】- 请投票
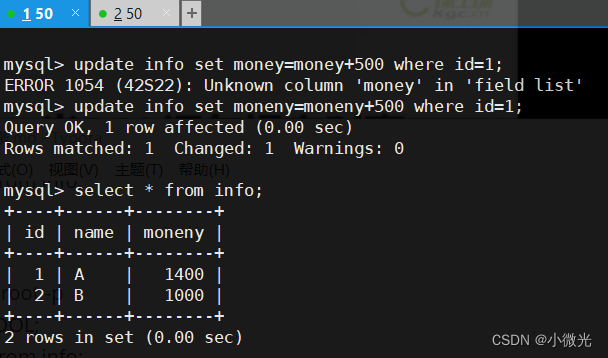
Mysql index, transaction and storage engine
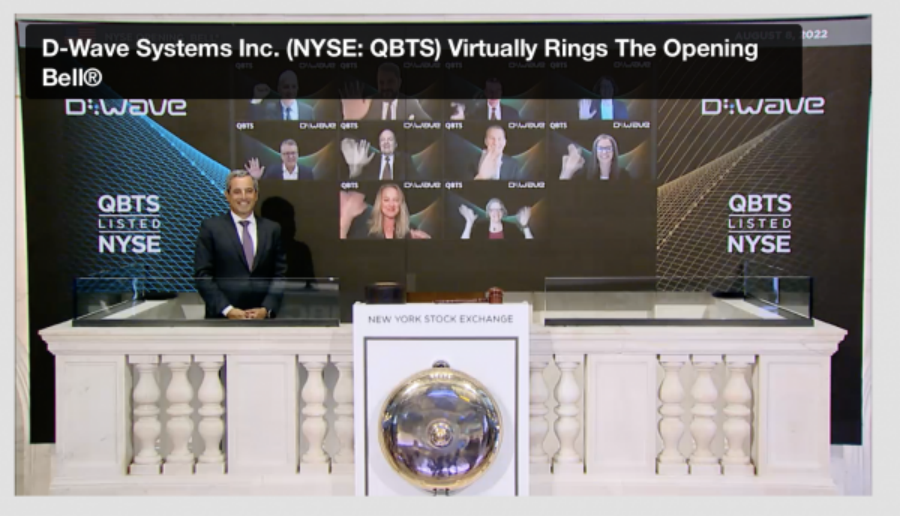
D-Wave成功上市!量子计算商业化正在加速

【独立站运营】做社交媒体营销的两大关键点
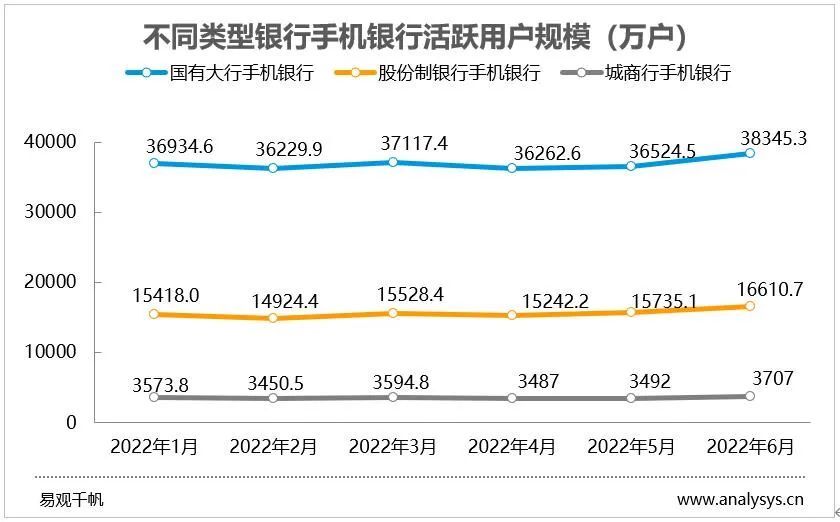
Active users of mobile banking grew rapidly in June, hitting a half-year high

Toronto Research Chemicals BTK抑制剂丨ACP-5197
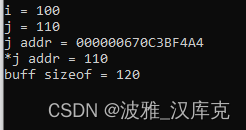
const的自己理解

Toronto Research Chemicals霉菌毒素分析丨T2 四醇
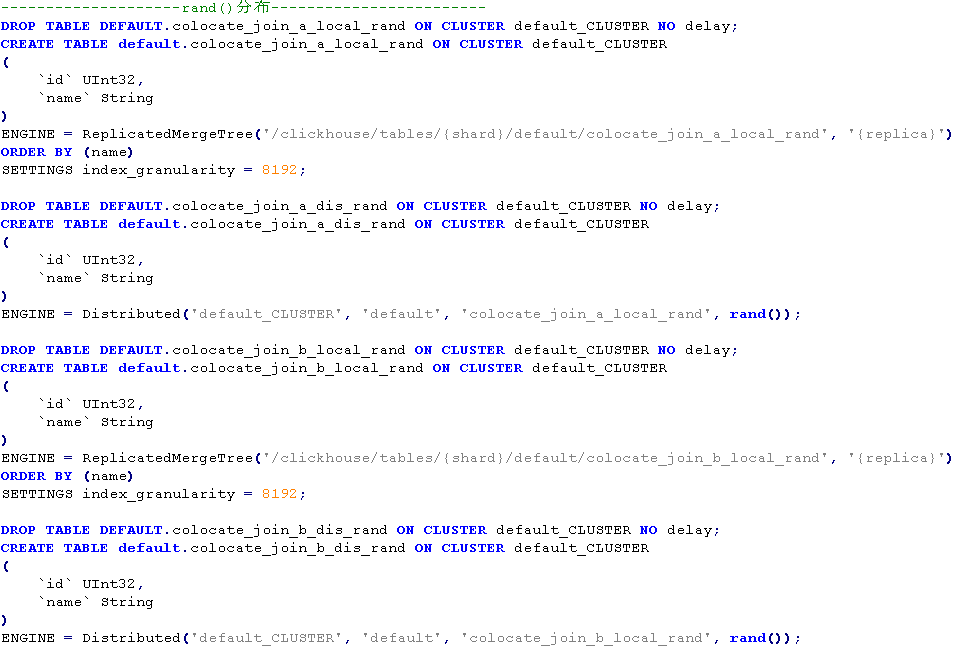
Colocate Join :ClickHouse的一种高性能分布式join查询模型
随机推荐
多线程与高并发(11)——经典面试题之实现一个容器,提供两个方法,add,size。
Before opening a futures account, you must confirm the handling fee as soon as possible
【接入指南 之 直接接入】手把手教你快速上手接入HONOR Connect平台(下)
多线程与高并发(五)—— 源码解析 ReentrantLock
「企业架构」什么是Zachman框架?
oracle11g体系结构
flex使用align-content无效
【图像分割】基于元胞自动机实现图像分割附matlab代码
欧洲核子研究中心首次在量子机器学习研究中取得实效
海思HI3516DV300开发资料
开发模式对测试的影响
文件包含漏洞复习总结
容器化 | 在 S3 实现定时备份
【HMS core】【FAQ】Account Kit、push Kit典型问题合集1
CSV(Comma-Separate-Values)逗号分隔值文件
五菱宏光MINI EV,唯一的缺点就是安全性
1001 A+B Format (string processing)
迪文发布新款2K高清DGUS智能屏
FFmpeg extract H264 nalu from the mp4
【图像去雾】基于颜色衰减先验的图像去雾附matlab代码