当前位置:网站首页>配置dns服务
配置dns服务
2022-08-11 05:33:00 【weixin_45512368】
文章目录
配置dns服务。
1、 在两台master,slave服务器上,分别安装
yum install -y bind bind-chroot bind-libs bind-utils
2、 修改master的allow-transfer和zone部分。修改
slave的zone部分分别拷贝到/etc/named.conf。
Master.conf配置文件
//
// named.conf
//
// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS// server as a caching only nameserver (as a localhost DNS resolver only).
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
options {
listen-on port 53 {
any; };
listen-on-v6 port 53 {
any; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db"; statistics-file "/var/named/data/named_stats.txt"; memstatistics-file "/var/named/data/named_mem_stats.txt"; allow-query {
any; }; allow-transfer {
192.168.152.xx(主ip); };
/*
- If you are building an AUTHORITATIVE DNS server, do NOT enable recursion.
- - If you are building a RECURSIVE (caching) DNS server, you need to enable recursion.
- - If your recursive DNS server has a public IP address, you MUST enable access control to limit queries to your legitimate users. Failing to do so will cause your server to become part of large scale DNS amplification attacks. Implementing BCP38 within your network would greatly reduce such attack surface
*/
recursion no;
dnssec-enable yes;
dnssec-validation yes;
/* Path to ISC DLV key */
bindkeys-file "/etc/named.iscdlv.key";
managed-keys-directory "/var/named/dynamic"; pid-file "/run/named/named.pid";
session-keyfile "/run/named/session.key";};
zone "域名" IN {
type master;
file "/var/named/named.(你所写的文件名称)";
allow-transfer {
192.168.xx.xx(ip地址); };
};
zone "XX.168.192(网址前三段倒着写).in-addr.arpa" IN {
type master;
file "/var/named/named.ip段";
allow-transfer {
192.168.162.129; };
};
logging {
channel default_debug {
file "data/named.run"; severity dynamic; };};zone "." IN {
type hint; file "named.ca";};include "/etc/named.rfc1912.zones";include "/etc/named.root.key";
Slave.conf的配置文件
//
// named.conf
//
// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS
// server as a caching only nameserver (as a localhost DNS resolver only).
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
options {
listen-on port 53 {
any; };
listen-on-v6 port 53 {
any; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt"; memstatistics-file "/var/named/data/named_mem_stats.txt"; allow-query {
any; };
/*
- If you are building an AUTHORITATIVE DNS server, do NOT enable recursion.
- - If you are building a RECURSIVE (caching) DNS server, you need to enable recursion.
- - If your recursive DNS server has a public IP address, you MUST enable access control to limit queries to your legitimate users. Failing to do so will cause your server to become part of large scale DNS amplification attacks. Implementing BCP38 within your network would greatly reduce such attack surface
- */
- recursion no;
- dnssec-enable yes;
- dnssec-validation yes;
- /* Path to ISC DLV key
- */
bindkeys-file "/etc/named.iscdlv.key"; managed-keys-directory "/var/named/dynamic"; pid-file "/run/named/named.pid";
session-keyfile "/run/named/session.key";
};
zone "域名" IN {
type slave;
file "/var/named/named.域名";
masters {
192.168.152.xx; };
};
zone "152.168.192.in-addr.arpa" IN {
type slave;
file "/var/named/named.192.168.152"; masters {
192.168.152.xx; };
};
logging {
channel default_debug {
file "data/named.run"; severity dynamic; };
};
zone "." IN {
type hint;
file "named.ca";
};
include "/etc/named.rfc1912.zones";
include "/etc/named.root.key";
3、 到 /var/named 配置正解文件named.域名 和反解文件ip,注意正解文件把yum 和time主, time从写进去。
Ip解析
$TTL 600
@ IN SOA master.域名 root.mail.域名 ( 2016110303 3H 15M 1W 1D )
@ IN NS master.域名
@ IN NS slave.域名
129 IN PTR master.域名
131 IN PTR slave.域名
#其中129为ip最后几位
域名解析
$ORIGIN 域名
$TTL 600@ IN SOA master.域名 root.mail.域名 ( 2016110303 3H 15M 1W 1D )
@ IN NS master.域名
@ IN NS slave.域名
master.域名 IN A 192.168.152.129
slave.域名 IN A 192.168.152.131
aaa IN CNAME master.域名
bbb IN CNAME slave.域名
4、 配置完后检查配置文件看是否有语法错误:
a) named.conf: named-checkconf /etc/named.conf
b) zone文件:
i. named-checkzone 域名 /var/named/named.域名
ii. named-checkzone IP /var/named/named.IP
检查完更正语法错误。
注意文件的属主属组named
5、 启动named服务。主备服务器都启动:
systemctl enable named
systemctl start named
6、 检查dns是否正常:
cat << EOF > /etc/resolv.conf
search 域名
nameserver $dns1
nameserver $dns2
EOF
主从一致
配置hosts文件
添加
Ip 主机名.域名
Ip 主机名.域名
然后nslookup 主机名看看是否能正常解析。nslookup ip 看是否能反解。
dns master 的服务器正常后, 把/etc/resolv.conf的nameserver 改成$dns2的地址。看 dns slave是否解析正常。
调试到都正常为止。
边栏推荐
- 逐步揭示makop.mkp勒索病毒中毒防范恢复解密
- 无胁科技-TVD每日漏洞情报-2022-8-3
- (二)软件测试理论(*重点用例方法编写)
- 无胁科技-TVD每日漏洞情报-2022-7-22
- uboot设置默认的bootdelay
- Threatless Technology-TVD Daily Vulnerability Intelligence-2022-8-6
- 记录一个刚写的Makefile
- Deep Learning Matlab Toolbox Code Comments
- HPC平台搭建
- (1) Software testing theory (0 basic understanding of basic knowledge)
猜你喜欢
随机推荐
mongo-express 远程代码执行漏洞复现
deepin v20.6+cuda+cudnn+anaconda(miniconda)
FusionCompute8.0.0实验(0)CNA及VRM安装(2280v2)
(二)软件测试理论(*重点用例方法编写)
vulnhub靶机--6Day_Lab-v1.0.1
无胁科技-TVD每日漏洞情报-2022-7-27
内存调试工具Electric Fence
VMware workstation 16 installation and configuration
Numpy_备注
Django QuerySet.order_by() SQL注入漏洞复现
无胁科技-TVD每日漏洞情报-2022-7-25
使用路由器DDNS功能+动态公网IP实现外网访问(花生壳)
无胁科技-TVD每日漏洞情报-2022-7-29
SECURITY DAY03(一键部署zabbix)
智能合约 ——— app评分合约
项目笔记——随机2
TCP 三次握手、四次断开
CLUSTER DAY01 (Introduction to cluster and LVS, LVS-NAT cluster, LVS-DR cluster)
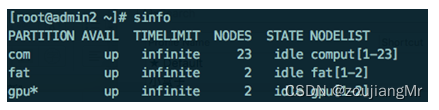
Basic use of Slurm
文本三剑客——grep过滤