当前位置:网站首页>How many hacking methods do you know?
How many hacking methods do you know?
2022-04-23 20:26:00 【Huacheng bag】
Preface
- Blog home page : Huacheng bag
- Welcome to focus on the likes collection ️ Leaving a message.
- This article is included in the full stack column of hacker attack and defense technology : Intranet Security . It will be updated in the future , Coming soon !
- This column is specifically aimed at Xiaobai who wants to get started in the field of network security , Plan to finish in a month !
- One can walk very fast , A group of people can go further ! Join me and study with me !- Only by continuous learning can we not be submerged by the vast sea of people !
- If an error is found , Please leave me a message in the comment area , Thank you very much !
Catalog
🥦 One 、 Hacking methods commonly used by hackers
The common penetration methods of hackers can be divided into 6 class : Get password intrusion 、 Remote control intrusion 、 Trojans invade 、 System vulnerability intrusion 、 Email intrusion 、 Network monitoring, intrusion, etc .
1. Get password intrusion
seeing the name of a thing one thinks of its function , Is to get the account of the administrator or user 、 password , And steal system information . There are several ways to obtain the password :
- Get the user password through network monitoring
This kind of method has some limitations , But the harm is great , The listener can often get the account and password of the user in the network segment , It is a big threat to LAN security . - Blow up the account number 、 password
- Get the user password file on a server Shadow After the document , Crack the user password with a brute force cracking program .
2. Remote control intrusion
Remote control is on the network , By a computer ( Main control end / client ) Remote departure control another computer ( Charged end / Server side ) Technology And remote control generally refers to the control of remote computers through the network . Intrusion methods through remote control , You can get the following contents of the target host :
- Get the target computer screen image 、 List of windows and processes ;
- Record and extract remote keyboard events ;
- open 、 Close any directory of the target computer and realize resource sharing ;
- Activate 、 Terminate the remote program process ;
- Manage files and folders on remote computers
- Shut down or restart the operating system in the remote computer
- modify Windows The registry ;
- Download Text, capture audio and video signals and other operations on the remote computer .
Remote control generally supports LAN、WAN、 dial 、 Internet and other network methods . Besides , Some remote control software also supports serial port 、 Control the remote host through parallel port .
3. Trojans invade
Trojan horse program can directly invade the user's computer and destroy it , It is often disguised as a tool program or game to induce users to open mail attachments with Trojan horse programs or download them directly from the Internet , Once the user opens the attachments of these emails or executes these programs , These Trojan viruses 🦠 The program will remain on the user's computer , And hide it in the user's computer system , When Windows Qi Dynamic time , these muma Was quietly executed . When users connect their computers to the Internet , This Trojan will notify the attacker , Report the user's IP Address and preset port . After receiving this information, the attacker , Then use this hidden program , You can arbitrarily modify the user's computer parameter settings , Copy file , Peeping at the contents of the user's entire hard disk , So as to control the user's computer .
4. System vulnerability intrusion
at present , Most computers have Windows operating system , although Windows operation The stability and security of the system are continuously improved with the improvement of its version , But there will still be different security risks , Namely vulnerability . Attackers can use professional tools to discover these vulnerabilities , After understanding the vulnerabilities and shortcomings of the target computer , Attackers can take advantage of buffer overflow and test the user's account and password , To achieve the purpose of exploratory attack on the host .
5. Email intrusion
E-mail intrusion is mainly manifested in two ways , The details are as follows : One is . E-mail bombing That is commonly referred to as the mail bomb , It refers to the use of forged IP Address and email address to the same mailbox 、 Thousands or even countless times of spam with the same content , Causing the victim's mailbox to be “ Fried ”, In serious cases, it may bring danger to the e-mail server operating system , Even paralysis . The second is electronic Email spoofing . An attacker can pretend to be a system administrator , Send an email to the user asking the user to change the password or load in a seemingly normal attachment bingdu🦠 Or other Trojan horse programs , Such deception requires users to be vigilant , Generally, the harm is not too great .
6. Network monitoring intrusion
Network monitoring is a working mode of the host , In this mode , The host can receive all information transmitted on the same physical channel , No matter who the sender and receiver of this information are . here , If the information communicated between two hosts is not encrypted , Just use network monitoring tools , Such as SpyNet Sniffer、SRSniffer etc. , You can easily intercept information including passwords and accounts .
🥦 Two 、 Conclusion
What else do you have to add , Welcome to comment area !
版权声明
本文为[Huacheng bag]所创,转载请带上原文链接,感谢
https://yzsam.com/2022/04/202204232023284441.html
边栏推荐
- Recognition of high-speed road signs by Matlab using alexnet
- Unity 模型整体更改材质
- Numpy sort search count set
- [graph theory brush question-5] Li Kou 1971 Find out if there is a path in the graph
- Installation and use of NVM
- SQL Server Connectors By Thread Pool | DTSQLServerTP plugin instructions
- Fundamentals of network communication (LAN, Wan, IP address, port number, protocol, encapsulation and distribution)
- Historical track data reading of Holux m1200-e Bluetooth GPS track recorder
- I JS deep copy and shallow copy
- Markdown < a > tag new page open link
猜你喜欢
![Azkaban recompile, solve: could not connect to SMTP host: SMTP 163.com, port: 465 [January 10, 2022]](/img/1a/669c330e64af8e75f4b05e472d03d3.png)
Azkaban recompile, solve: could not connect to SMTP host: SMTP 163.com, port: 465 [January 10, 2022]

Building the tide, building the foundation and winning the future -- the successful holding of zdns Partner Conference
【PTA】L1-002 打印沙漏
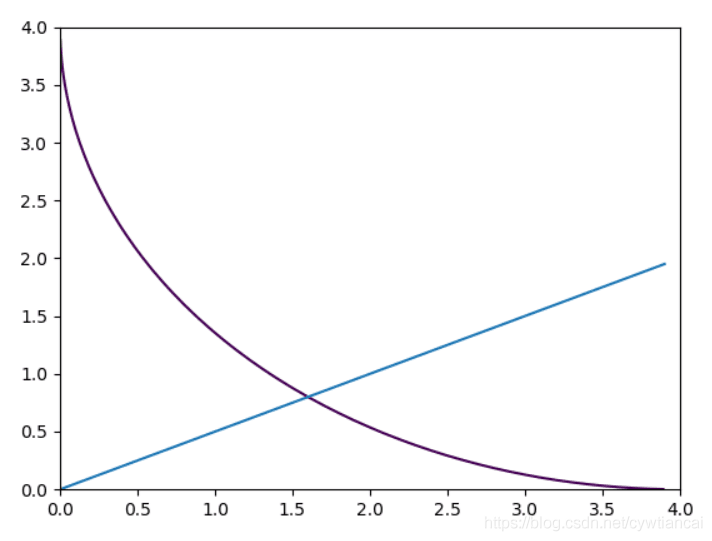
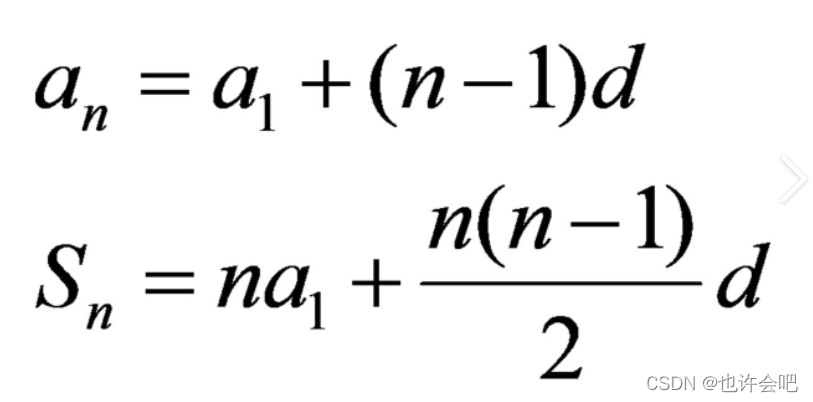
Monte Carlo py solves the area problem! (save pupils Series)
What is the difference between a host and a server?
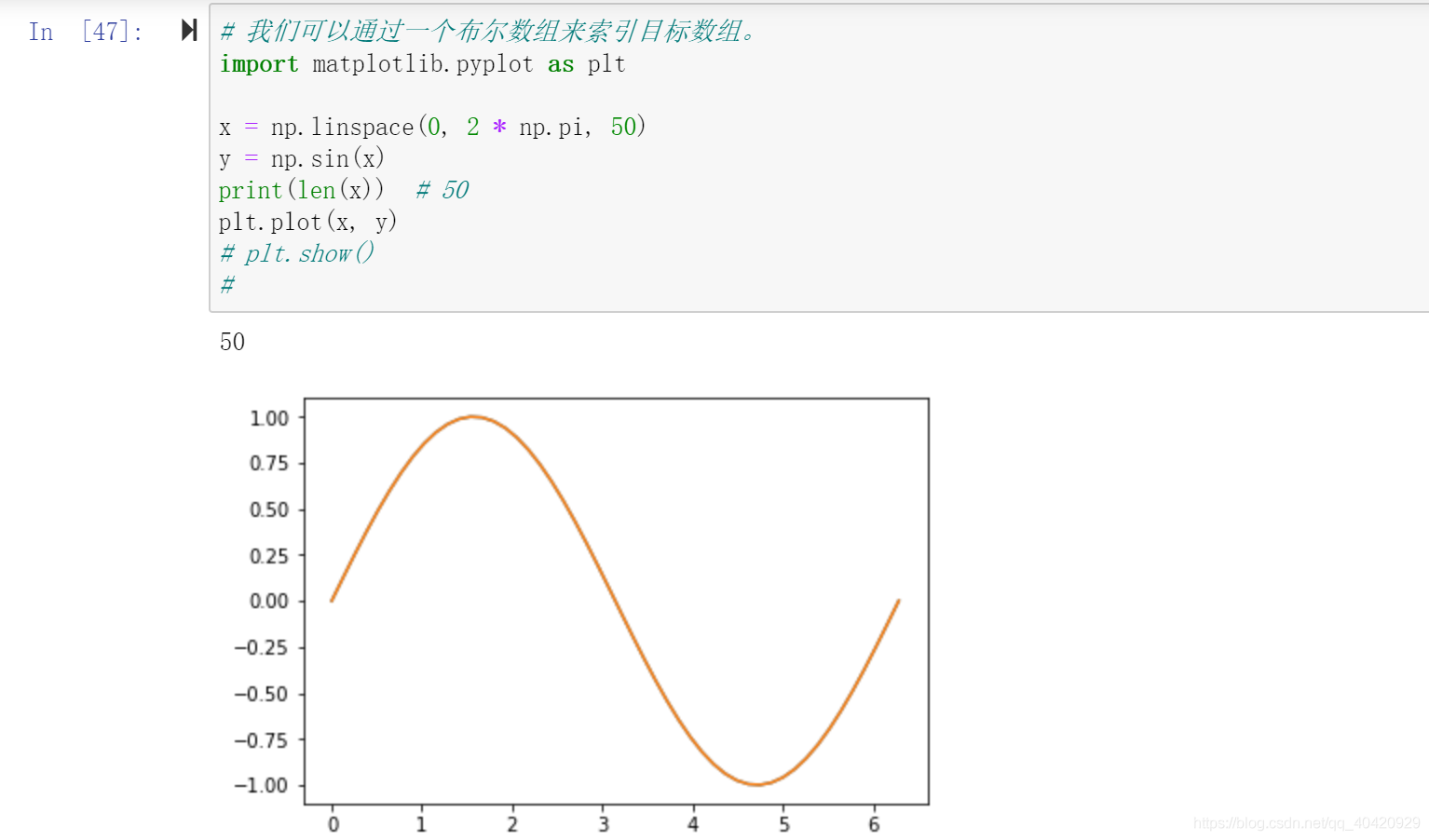
Numpy Index & slice & iteration

WordPress plug-in: WP CHINA Yes solution to slow domestic access to the official website
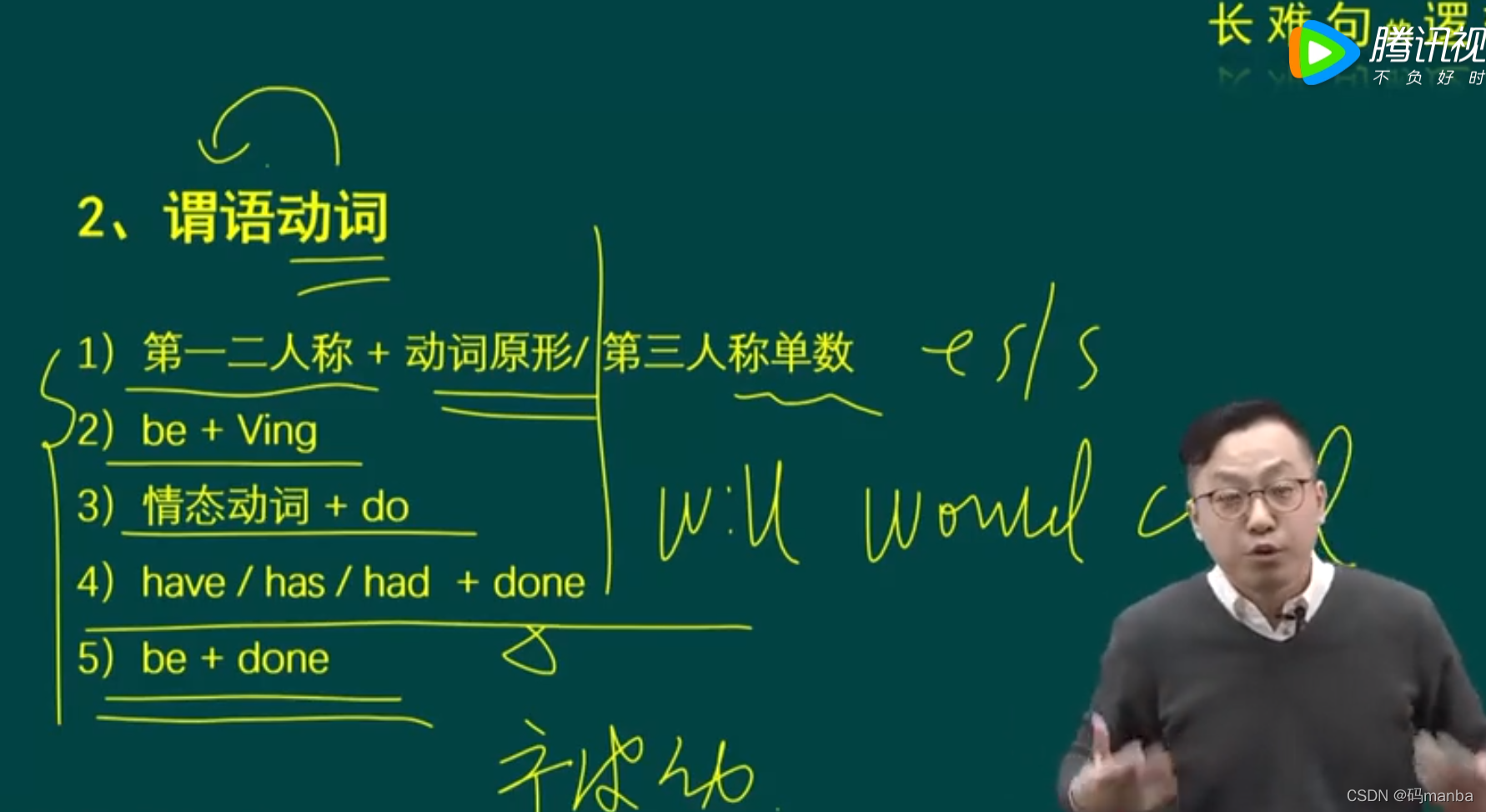
考研英语唐叔的语法课笔记

DTMF dual tone multi frequency signal simulation demonstration system
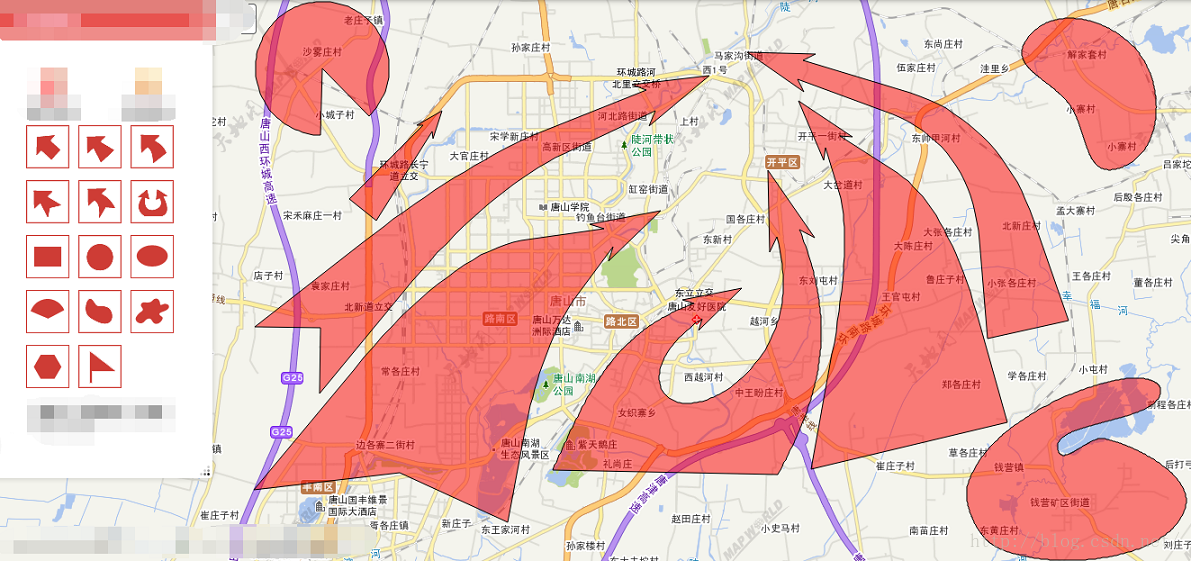
ArcGIS JS version military landmark drawing (dovetail arrow, pincer arrow, assembly area) fan and other custom graphics
随机推荐
2022DASCTF Apr X FATE 防疫挑战赛 CRYPTO easy_real
The market share of the financial industry exceeds 50%, and zdns has built a solid foundation for the financial technology network
What is the difference between a host and a server?
An error is reported in the initialization metadata of the dolphin scheduler -- it turns out that there is a special symbol in the password. "$“
Cadence Orcad Capture 批量更改元件封装功能介绍图文教程及视频演示
DNS cloud school | analysis of hidden tunnel attacks in the hidden corner of DNS
How do BIM swindlers cheat? (turn)
2022dasctf APR x fat epidemic prevention challenge crypto easy_ real
Error reported by Azkaban: Azkaban jobExecutor. utils. process. ProcessFailureException: Process exited with code 64
PCL点云处理之基于PCA的几何形状特征计算(五十二)
The construction and use of Fortress machine and springboard machine jumpserver are detailed in pictures and texts
Operation of numpy array
Commit and ROLLBACK in DCL of 16mysql
三十一. `prototype`显示原型属性和`__proto__`隐式原型属性
[PTA] get rid of singles
How about CICC fortune? Is it safe to open an account
Common form verification
PCA based geometric feature calculation of PCL point cloud processing (52)
Matlab analytic hierarchy process to quickly calculate the weight
Sqoop imports tinyint type fields to boolean type