当前位置:网站首页>Awk example skills
Awk example skills
2022-04-23 20:43:00 【baboon_ chen】
One 、 Transpose files
hypothesis file.txt The contents of the document are as follows :
name age
alice 21
ryan 30
It should output :
name alice ryan
age 21 30
convert.awk
##
## awk -f convert.awk file.txt
{
# The code in this brace is Processing of text
# NF A number of columns ,NR Indicates the number of lines read
# Be careful for Medium i from 1 Start ,i There is no type before
for (i=1; i<=NF; i++){
# For each column
if(NR==1){
# If it's the first line
# Will be the first i The value of the column is stored in res[i],$i It means the first one i The value of the column ,i Is the subscript of the array , Take the column serial number as the subscript ,
# Arrays can be used directly without definition
res[i]=$i;
}
else{
# Not the first line , Map this line to i The values of the columns are spliced into res[i]
res[i]=res[i] " " $i
}
}
}
# BEGIN{} What to do before scanning a file ;END{} What to do after file scanning .
END{
# The output array
for (i=1; i<=NF; i++){
print res[i]
}
}
版权声明
本文为[baboon_ chen]所创,转载请带上原文链接,感谢
https://yzsam.com/2022/04/202204210546351155.html
边栏推荐
- C# 知识
- I JS deep copy and shallow copy
- MySQL基础之写表(创建表)
- LeetCode 1351、统计有序矩阵中的负数
- Syntax Error: TypeError: this. getOptions is not a function
- Summary and effect analysis of methods for calculating binocular parallax
- BMP JPEG picture to vector image contourtrace
- LeetCode 994、腐烂的橘子
- 三十一. `prototype`显示原型属性和`__proto__`隐式原型属性
- Vscode download speed up
猜你喜欢
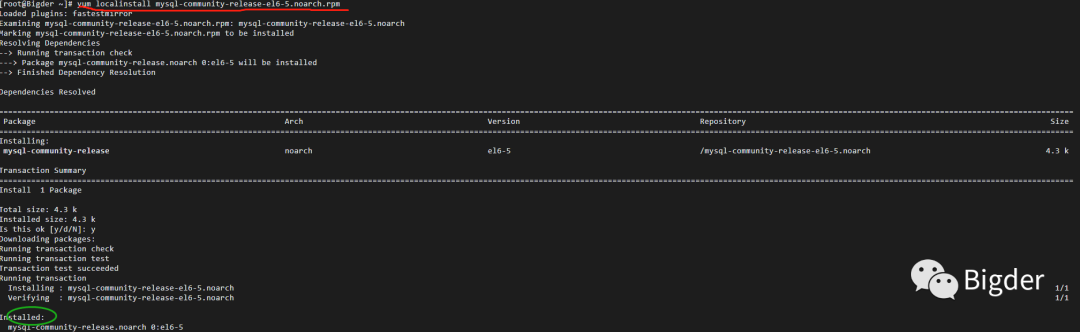
Install MySQL 5.0 under Linux 64bit 6 - the root password cannot be modified
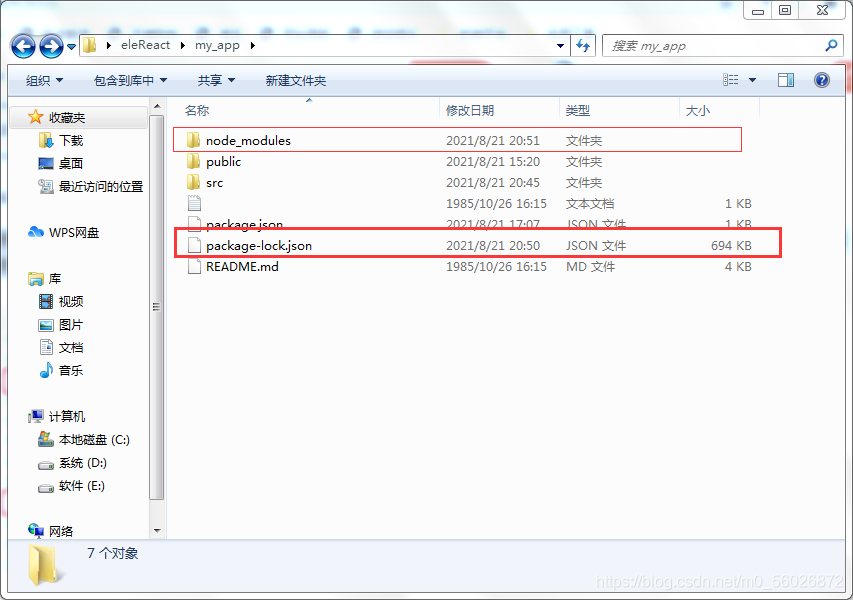
Solution: NPM err! code ELIFECYCLE npm ERR! errno 1
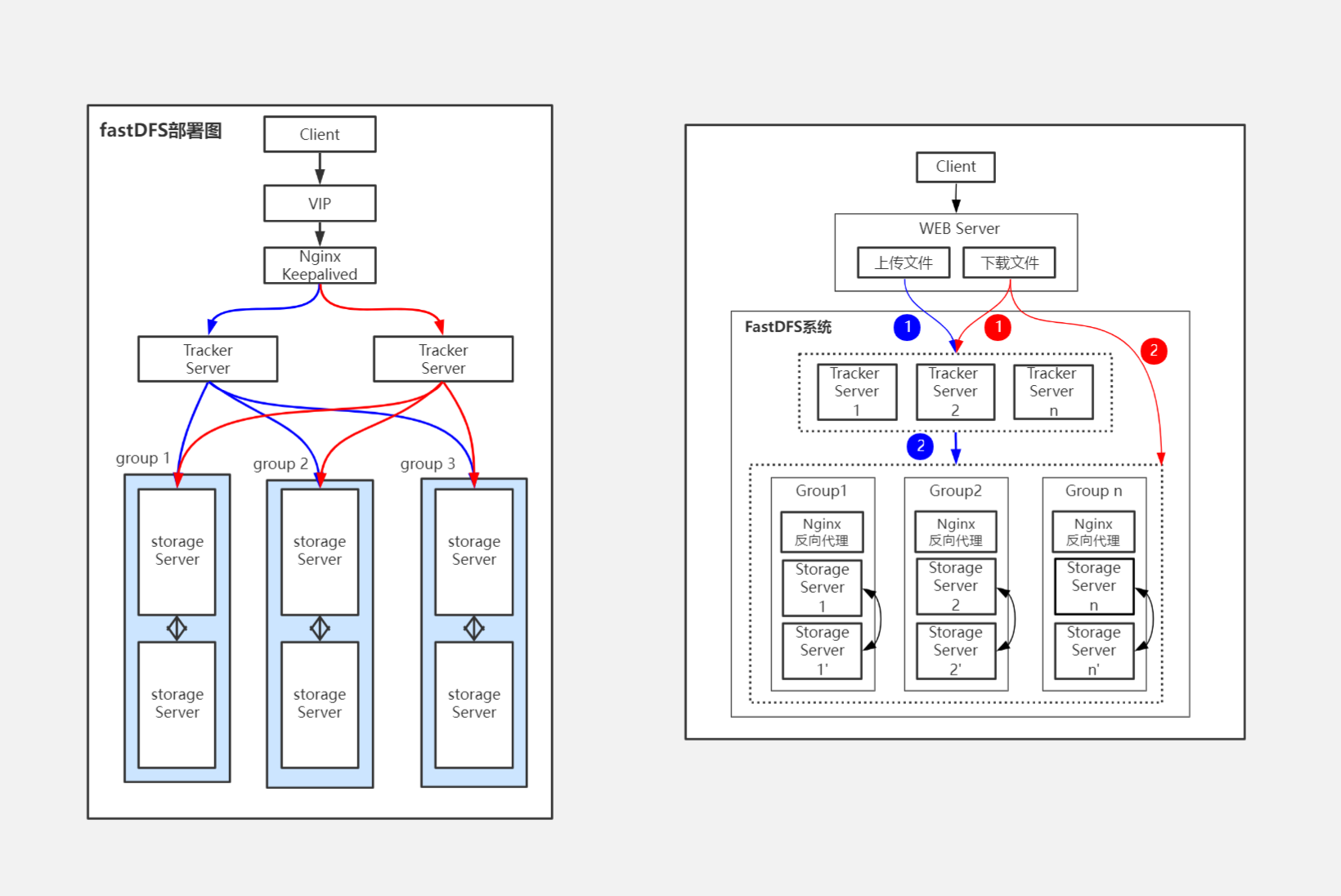
Fastdfs思维导图
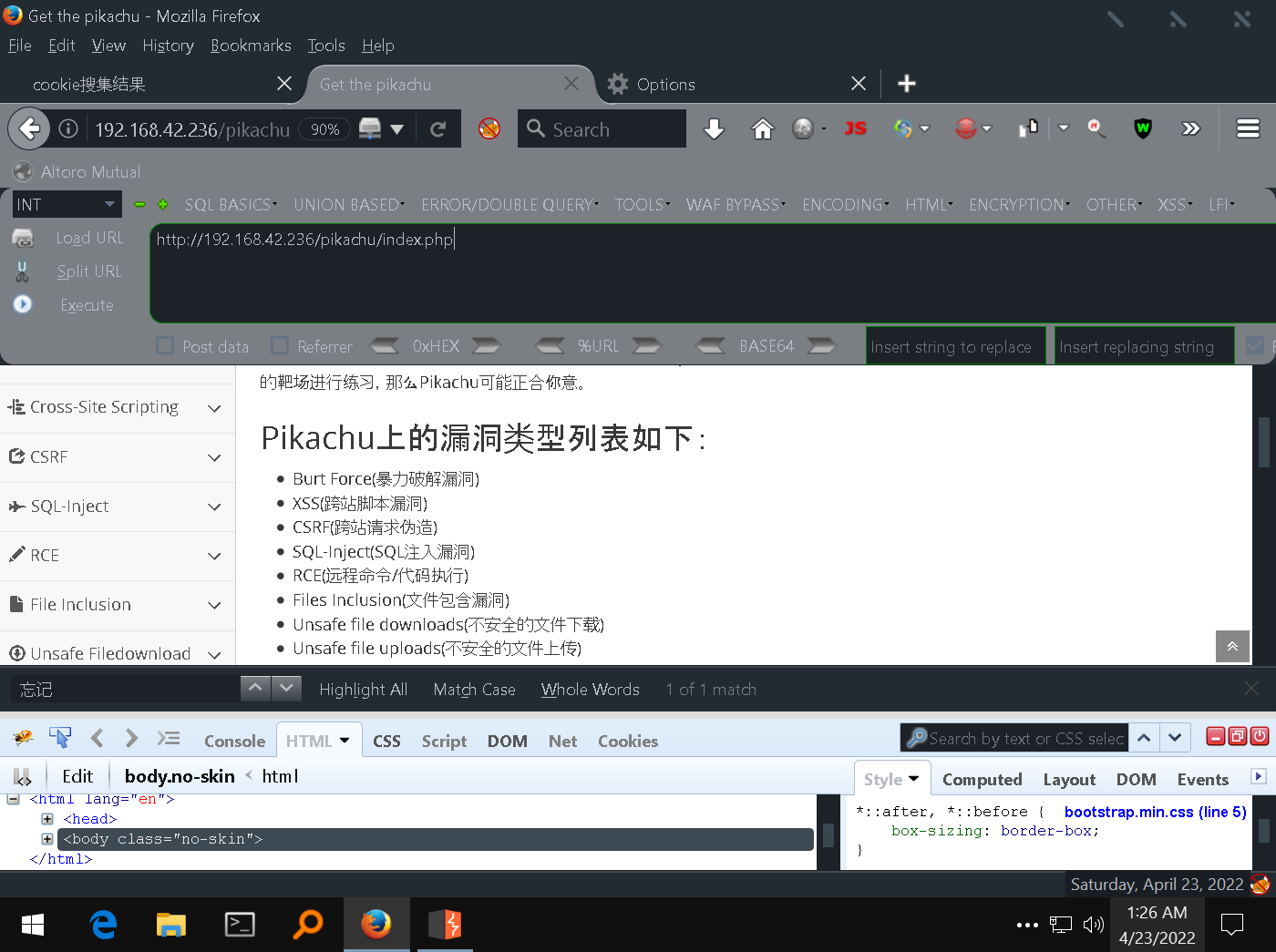
3-5通过XSS获取cookie以及XSS后台管理系统的使用
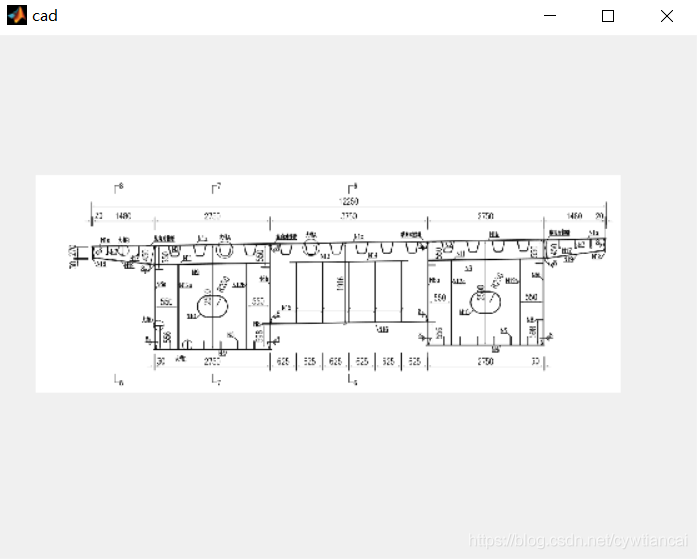
Development of Matlab GUI bridge auxiliary Designer (functional introduction)
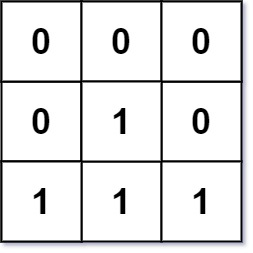
LeetCode 542、01 矩阵
![[SQL] string series 2: split a string into multiple lines according to specific characters](/img/a2/835ff6f5593fae15c70104cfb19c42.png)
[SQL] string series 2: split a string into multiple lines according to specific characters

How to configure SSH public key in code cloud
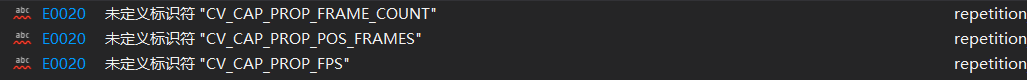
Identifier CV is not defined in opencv4_ CAP_ PROP_ FPS; CV_ CAP_ PROP_ FRAME_ COUNT; CV_ CAP_ PROP_ POS_ Frames problem
![[PTA] get rid of singles](/img/ab/b5d49f336cbfbede23b3377a9314ad.png)
[PTA] get rid of singles
随机推荐
Easy to use nprogress progress bar
Experience of mathematical modeling in 18 year research competition
Solve the Chinese garbled code of URL in JS - decoding
Analysis of the relationship between generalized Bim and CAD under the current background
RT-1052学习笔记 - GPIO架构分析
Commande dos pour la pénétration de l'Intranet
A login and exit component based on token
Create vs project with MATLAB
MySQL 存储过程和函数
LeetCode 709、转换成小写字母
go slice
Fastdfs思维导图
LeetCode 116. 填充每个节点的下一个右侧节点指针
Implementation of mypromise
Identification of bolt points in aerial photography based on perception
How to use PM2 management application? Come in and see
Matlab matrix index problem
[PTA] get rid of singles
内网渗透之DOS命令
高薪程序员&面试题精讲系列91之Limit 20000加载很慢怎么解决?如何定位慢SQL?