当前位置:网站首页>Meteor accelerator Trojan analysis and disposal plan
Meteor accelerator Trojan analysis and disposal plan
2022-08-10 03:32:00 【Thousands of miles :)】
0x01 背景
2020年,一款名为“流星加速器”The software is being silently promoted and disseminated through the downloaders of major download sites,It also carries malicious proxy modules and backdoor modules.After the user runs the software,These virus modules will be activated.A virus can take control of a user's computer,执行任意命令.
由于“流星加速器”用户数量较多,Resulting in a wider range of virus impact,Millions of users have been infected so far,And the number of infections is still more than a single day10The number of thousands has grown.
0x02 详细分析
样本列表
根据分析,“流星加速器”Two virus modules are released after running,One of them has malicious proxy capabilities(LocalNetwork.exe),可控制用户电脑作为流量跳板;Another module has backdoor functionality(SecurityGuard.exe),Can execute arbitrary remote commands,危害严重.此外,当用户卸载“流星加速器”后,The above virus modules will still reside on the user's computer,keep doing evil.
The Meteor Accelerator installation package with malicious modules is silently promoted by the downloader,The download station involved this time is Zhongguancun Online(zol.com.cn)等.相关信息如下图所示:

释放文件:
1. 288da3a2dd5154125187bf05a7172dedae9e13a0ebaf66c2b81e3d7d771e6c72

2.426b7a6c14379d2a81e0924436a30c87389e717ce90e51e2a28e3b4b4d4a1e88

行为监控
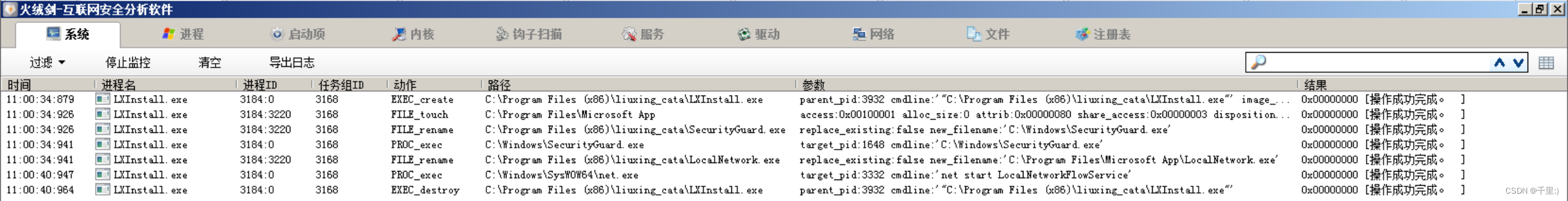
When Meteor Accelerator is silently promoted and installed by the downloader,The malicious agent module will be released in the installation directoryLocalNetwork.exewith the backdoor moduleSecurityGuard.exe.释放完成后,LXInstall.exe将创建C:\Program Files\Microsoft App文件夹并将LocalNetwork.exe移动到其中,随后启动LocalNetworkFlowService服务.同时LXInstall.exe会将SecurityGuard.exe移动到C:\Windowsdirectory and start the execution.The related actions are shown in the figure below:
LocalNetwork模块
LocalNetwork.exewill be receivedC&C服务器(58.218.92.196)的代理策略,Execute the proxy logic to forward the data traffic sent by the server,Occupy the user's network resources without the user's permission,The user's machine is reduced to a tool to help it profit.LocalNetwork.exeAfter running as a service,The user's host system information is first collected and sent encrypted toC&C服务器(yxjs.diaodu.ssot.net).随后C&CThe server returns the address information of the proxy communication server,相关代码如下图所示:

获取到的信息如下:

连接C&C服务器:

The obtained proxy communication server address
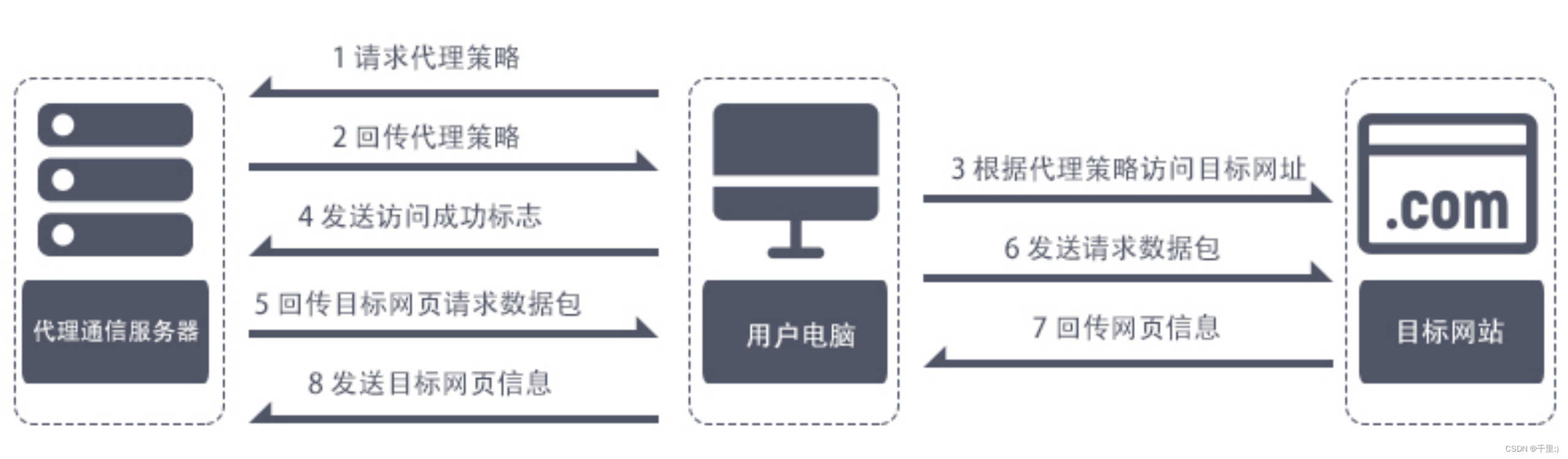
 After getting the proxy communication server address,LocalNetwork.exewill connect to it,Get the desired proxy policy.之后,LocalNetwork.exeThe target web page is accessed according to the delegated proxy policy,若访问成功,Returns information about the target page.Detailed communication process,如下图所示:
After getting the proxy communication server address,LocalNetwork.exewill connect to it,Get the desired proxy policy.之后,LocalNetwork.exeThe target web page is accessed according to the delegated proxy policy,若访问成功,Returns information about the target page.Detailed communication process,如下图所示:
Received proxy policy and data transfer content,如下图所示:


此外,Meteor accelerator main program(liuxing.exe)Threads will be created every other2will be detected in secondsLocalNetwork.exe进程是否存在,如果不存在,Will execute its software installation directoryLocalNetwork.exe.Released due to the current version of Meteor AcceleratorLocalNetwork.exeThe malicious agent module is no longer in its software installation directory,The above execution logic has failed,Updates to its main program modules are continuously tracked.相关逻辑,如下图所示:


SecurityGuard模块
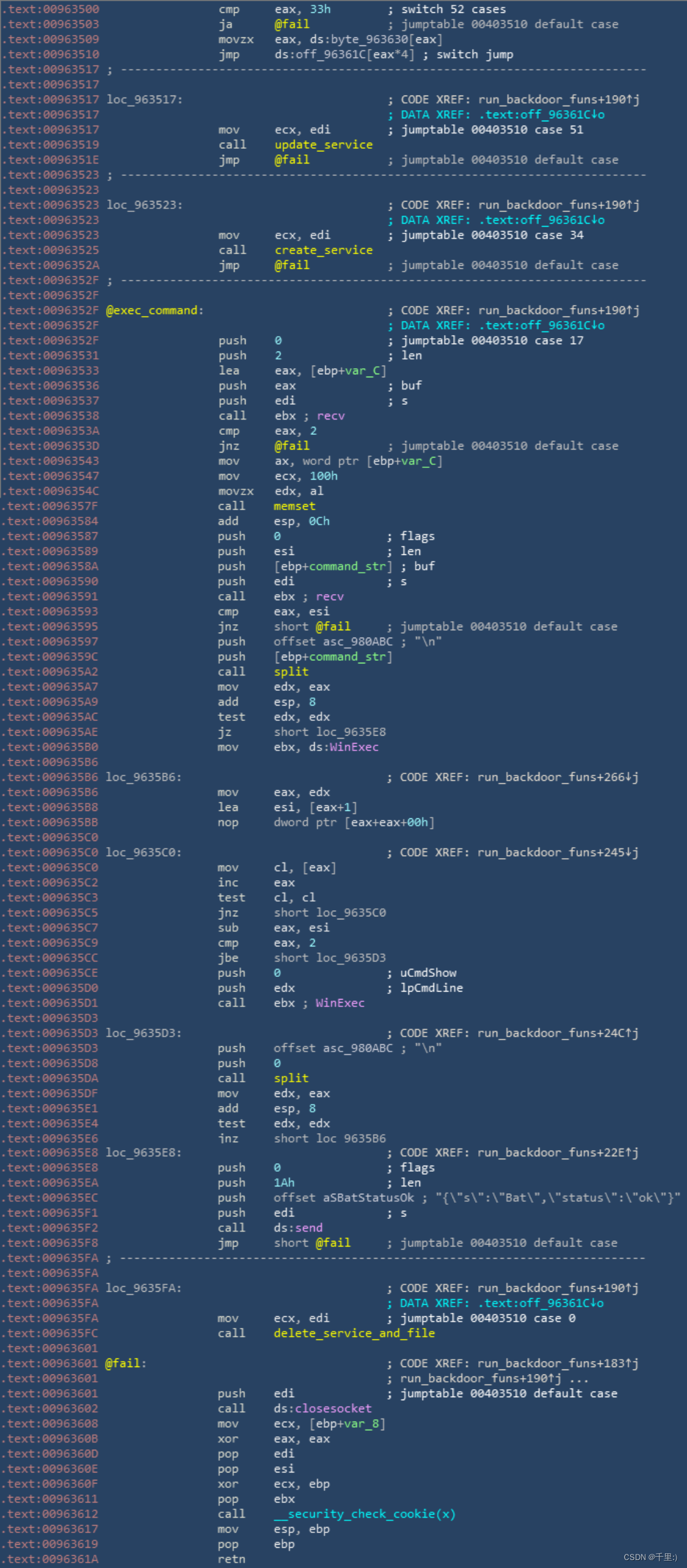
SecurityGuard.exeThe main function of a module is to register itself as a service and receive itC&C服务器(api.jm.taolop.com)The issued backdoor command control codes are used to execute different backdoor functions,如:更新模块,创建、删除服务,运行远程命令.相关代码如下图所示:

Execute the backdoor function
0x03 处置方法
Download velvet or other virus killing tools to clean and kill.
边栏推荐
猜你喜欢
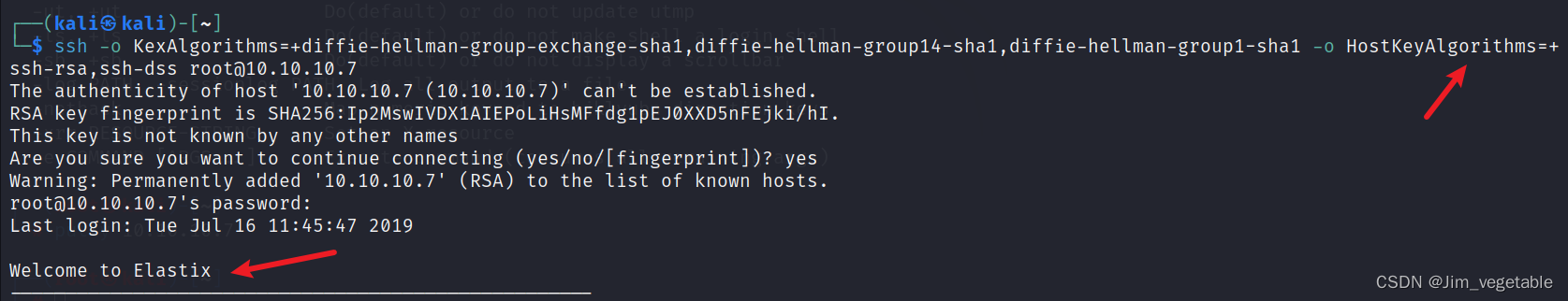
HackTheBox——Beep
实例045:求和
![[Kali Security Penetration Testing Practice Course] Chapter 9 Wireless Network Penetration](/img/7d/c621680ac73e2987f023a2e98e01df.png)
[Kali Security Penetration Testing Practice Course] Chapter 9 Wireless Network Penetration
In automated testing, test data is separated from scripts and parameterized methods
实例048:数字比大小
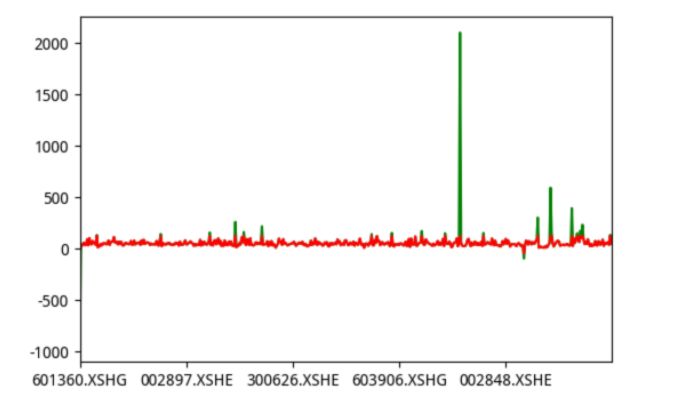
Introduction and application of quantitative trading strategies

sqlmap dolog外带数据

【二叉树-中等】1261. 在受污染的二叉树中查找元素

数据在内存中的存储

OpenCV图像处理学习一,加载显示修改保存图像相关函数
随机推荐
【语义分割】2022-HRViT CVPR
Shell编程--awk
Screen 拆分屏幕
《GB39707-2020》PDF download
Go语言JSON文件的读写操作
基于C51的中断控制
中级xss绕过【xss Game】
Open3D 中点细分(网格细分)
剑指offer专项突击版第25天
量化交易策略介绍及应用市值中性化选股
MMDetection框架的anchor_generators.py解析
sqlmap dolog外带数据
2022 Top Net Cup Quals Reverse Partial writeup
浅写一个下拉刷新组件
数据挖掘和数据仓库之间的区别
【Kali安全渗透测试实践教程】第6章 密码攻击
OpenCV图像处理学习四,像素的读写操作和图像反差函数操作
实例043:作用域、类的方法与变量
The flask to add and delete
MySQL: What MySQL optimizations have you done?