当前位置:网站首页>The Evolutionary History of the "Double Gun" Trojan Horse Virus
The Evolutionary History of the "Double Gun" Trojan Horse Virus
2022-08-10 03:32:00 【Thousands of miles :)】
Since it was first discovered by 360 Security in 2017, the "Double Gun" Trojan virus has undergone multiple variants, infecting more than 100,000 computer devices. Until May 2020, 360 Security and Baidu have destroyed hundreds of thousands of"The botnet composed of "broiler chickens" let us know that the scale of the botnet is so huge that the confrontation between good and evil is always fierce in places we can't see.
Next, the editor will take stock of the three-generation evolutionary history of the "Double Gun" virus.
The first appearance of "Double Gun"
In July 2017, 360 Security analyzed the structure of the first "Double Gun" Trojan and updated the virus database in time.According to the article, the infection sign of the "Double Gun" Trojan is that the browser homepage has been tampered with a URL navigation station with a number of "18299-9999"., After the MBR is loaded and executed, it will further infect the VBR (Volume Boot Record). After the VBR is started, it will release a driver and download the Trojan driver from the Internet to change the home page, and this driver will further detect the status of the MBR. If the MBR is repaired or not infected successfullyThen write-back MBR repeat infection.This is the first new type of Trojan that serially infects MBR and VBR, hence the name "Double Gun".
In addition to changing and locking the homepage of all browsers of Zhongzhao Computer, the maliciously downloaded driver of "Double Gun" also has a strong Trojan protection function, which is a powerful confrontation with anti-virus software.For example, after it starts, it points the driver name to the white driver name, so as to avoid anti-virus software; it protects the underlying device of the MBR hooked disk and resists the repair of anti-virus software; it tampers with the driver object dispatch function of the NTFS file system, and opens theThe system thread ensures that the hook on NTFS is not repaired, so as to prevent the normal process from deleting its Trojan file; at the same time, since the driver will be started first, it also makes it more difficult to clear.

2 "Double Gun" 2, shot in the secret room
In March 2018, the 360 Security Center found that the new variant of "Double Gun" began to appear, and started a comprehensive analysis from its infection behavior.Different from "Double Gun", "Double Gun 2" is mainly spread through the download station. It increases the confrontation strategy with anti-virus, and will intercept the creation of anti-virus files; at the same time, it will also lock the system registry HIVE file,As a result, normal service items cannot be written, as if a closed crime environment was set up, and a "secret room shooting" was carried out on the Zhongzhao computer.

"Double Gun" 3, violence strikes
In June 2018, 360 Security Center monitored and found that the third generation of the "Double Gun" Trojan appeared. Compared with the previous version, this version significantly enhanced the malicious locking of HIVE files in the system, making it more difficult for anti-software services to write.Like the previous "Double Gun" in the first two generations, the main behavior of the "Double Gun" Trojan 3 is to modify the MBR and VBR, and then tamper with the user's homepage for profit.Malicious driver map:

"Dual Gun" Features:
The "Double Gun" Trojan virus has infected more than 100,000 people in three years, and its malicious behavior mainly includes the following three types:
1. The malicious function of sending advertisements and spam to users, hijacking the account on the user's device, and sending and spreading advertisements;
2. Hijack traffic from legitimate e-commerce websites and direct infected users to designated websites,
3. Disable network security software.
All along, "Double Gun" uses images uploaded to Baidu Tieba (steganography) to assign configuration files and malicious drivers to botnets, and also uses Alibaba Cloud Storage to host configuration files, Baidu's data analysis platformTongji to manage the behavior of infected hosts.
Originally, "Double Gun" spread the Trojan by luring users into installing game launch software from sketchy game portals that contained malicious code in the name of patches.Once the user downloads and installs the patch, it accesses the above configuration information to download a file called "cs.dll", after that, "cs.dll" it not only creates a bot ID and reports it to the attacker's controlserver, but also injects another driver, DADELn.sys, to hijack system processes.

边栏推荐
猜你喜欢
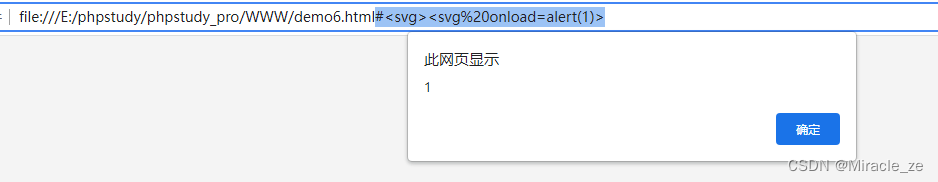
xss的DOMPurify过滤框架:一个循环问题以及两个循环问题
《GB39707-2020》PDF download

storage of data in memory
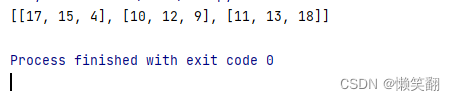
实例044:矩阵相加

OpenCV图像处理学习二,图像掩膜处理
![[Kali Security Penetration Testing Practice Course] Chapter 9 Wireless Network Penetration](/img/7d/c621680ac73e2987f023a2e98e01df.png)
[Kali Security Penetration Testing Practice Course] Chapter 9 Wireless Network Penetration
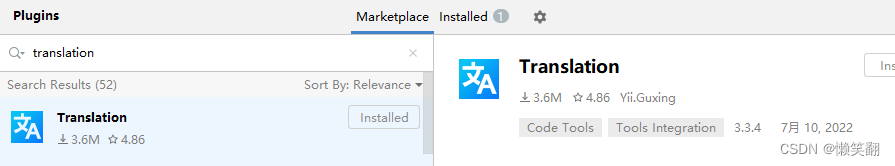
Pycharm中6个常用插件推荐
Pagoda server PHP+mysql web page URL jump problem
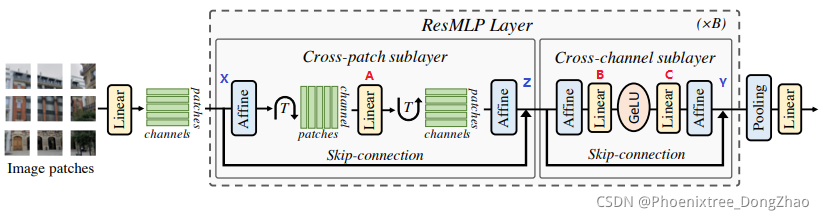
【图像分类】2022-ResMLP
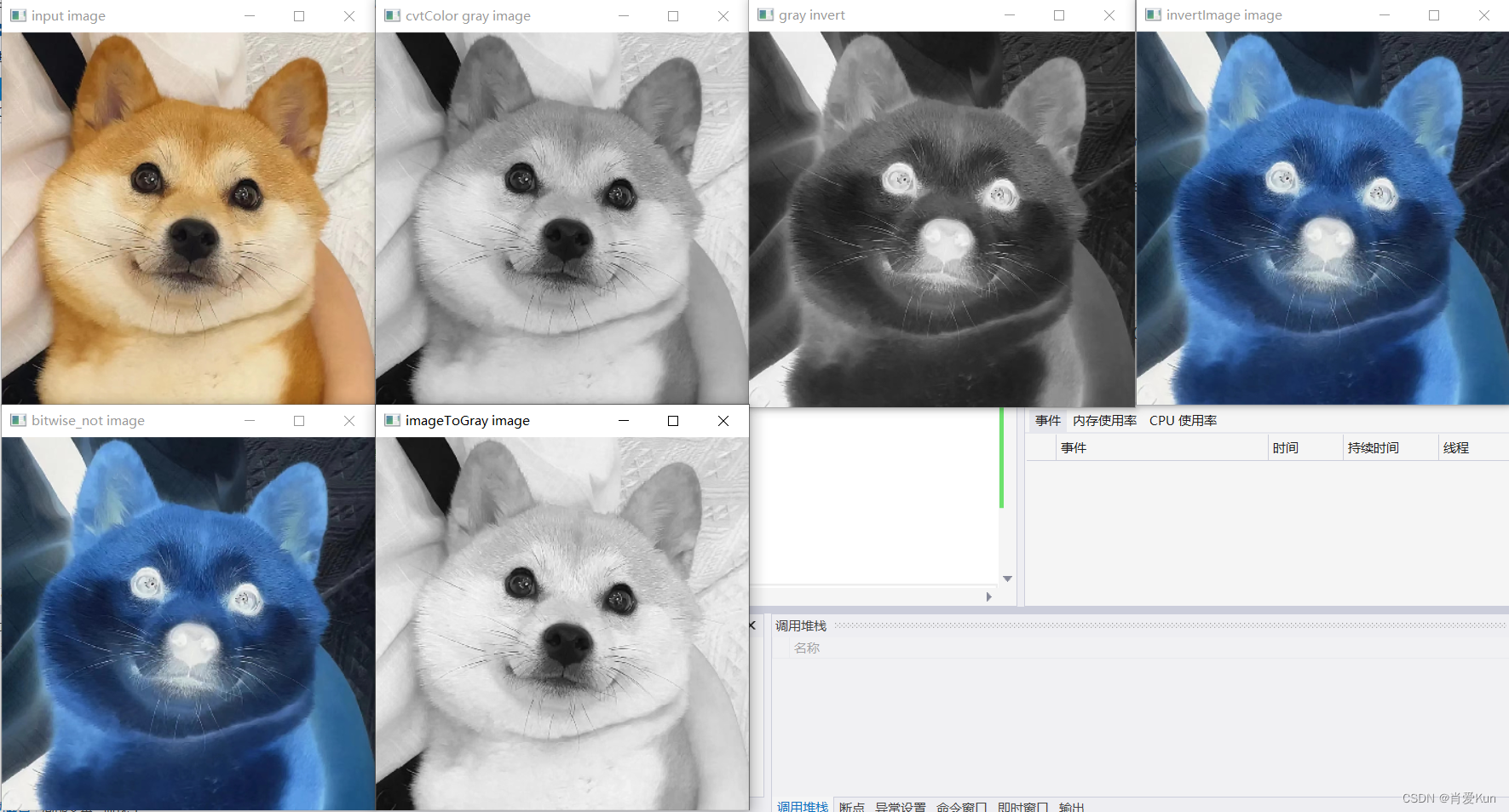
OpenCV图像处理学习四,像素的读写操作和图像反差函数操作
随机推荐
数据治理(五):元数据管理
2020.11.22 Exam Goldbach Conjecture Solution
量化交易策略介绍及应用市值中性化选股
what is a microcontroller or mcu
2022.8.9 Exam Unique Bid Auction--800 Question Solutions
Pycharm中6个常用插件推荐
将信号与不同开始时间对齐
在蓝图中给组件动态加子Actor组件
2022.8.8考试清洁工老马(sweeper)题解
Go语言JSON文件的读写操作
How Microbes Affect Physical Health
[Kali Security Penetration Testing Practice Course] Chapter 7 Privilege Escalation
[Kali Security Penetration Testing Practice Course] Chapter 9 Wireless Network Penetration
web crawler error
如何让数据库中的数据同步
GDB command basic parameters
MySQL:你做过哪些MySQL的优化?
《GB39707-2020》PDF download
【二叉树-中等】1104. 二叉树寻路
官宣出自己的博客了