当前位置:网站首页>Huawei router clock near the drainage experiment (using stream strategy)
Huawei router clock near the drainage experiment (using stream strategy)
2022-08-10 21:26:00 【Lay Master Wen Tao】
Router bypass experiment.
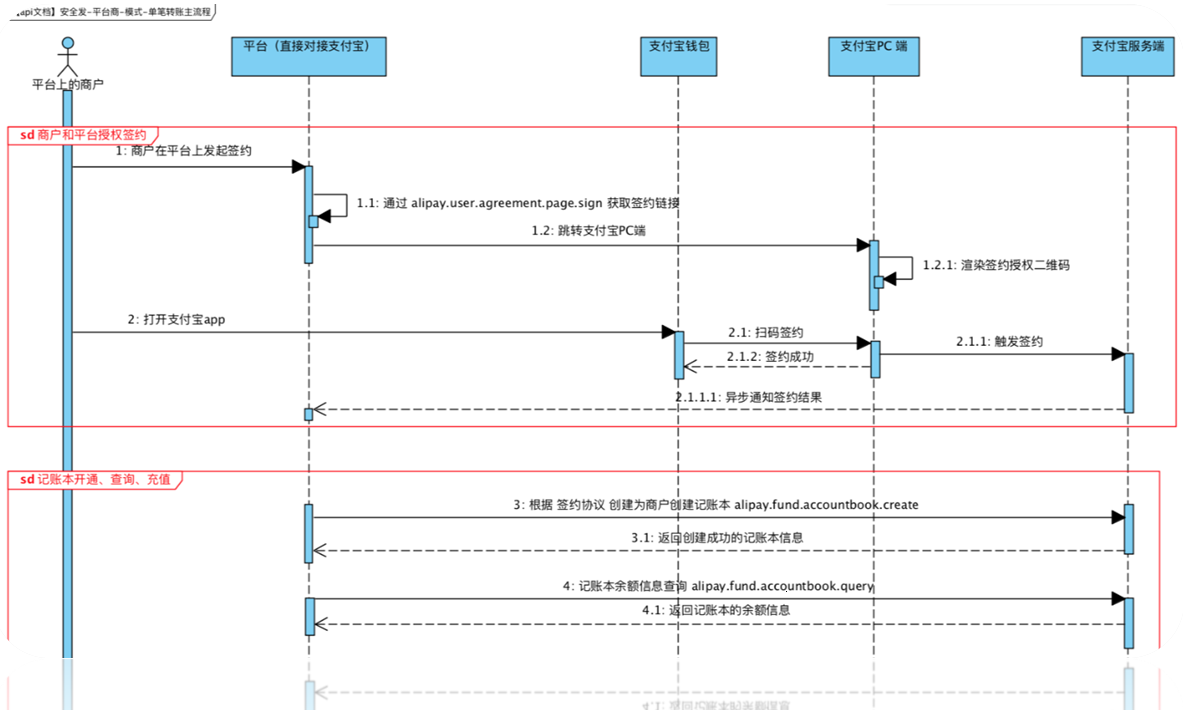
The purpose of the experiment, as shown in the figure, this experiment needs to draw the traffic from the address 10.1.2.1 to the side-mounted AR1 device when accessing two PCs, and then the AR1 device will be injected back to the AR3equipment.
The method of drainage can be used flexibly according to the specific environment. This experiment adopts the method of flow strategy.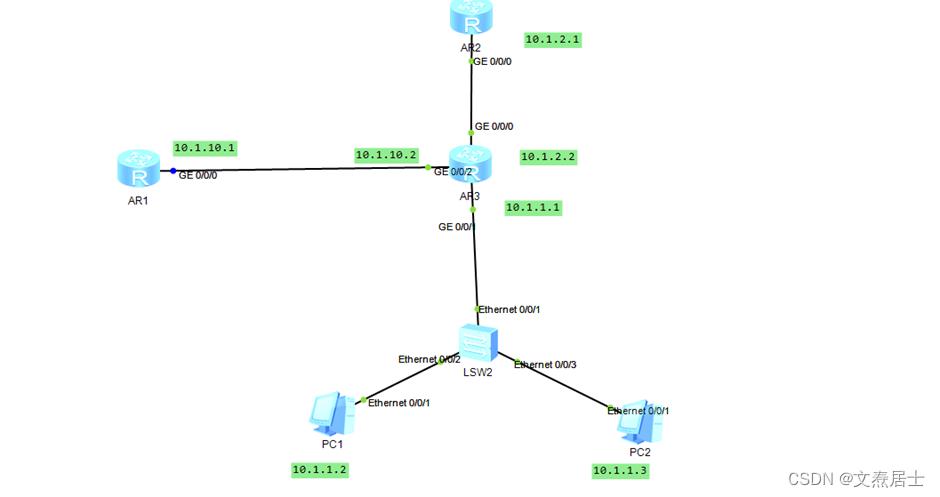
Specific configuration:
AR1:
interface GigabitEthernet0/0/0ip address 10.1.2.1 255.255.255.0ip route-static 0.0.0.0 10.1.2.2AR2:
interface GigabitEthernet0/0/0ip address 10.1.10.1 255.255.255.0ip route-static 10.1.1.0 24 10.1.10.2ip route-static 10.2.1.0 24 10.1.10.2It is also possible to use a default route for the connected device.AR2:
traffic classifier c1 operator or Create a traffic classifier to match traffic characteristics.The or guess here should be similar to the OR operation in programming, which is used to specify how to match the flow classification.(corrections are welcome)if-match anytraffic behavior b1 Creates a flow behavior that changes the direction of data flow.redirect ip-nexthop 10.1.10.1traffic policy p1 Creates a traffic policy and associates the created traffic classification with traffic behavior.classifier c1 behavior b1interface GigabitEthernet0/0/0ip address 10.1.2.2 255.255.255.0traffic-policy p1 inbound Finally, you need to apply this policy to the interface, paying attention to the direction.AR2 device address planning is as follows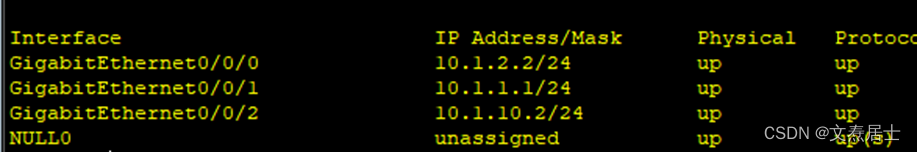
Finally, twoThe address and gateway are configured on a PC and it is OK.
Verification:
Use the device of 10.1.2.1 to ping two PCs, and perform packet capture verification on the interface of the connected device.
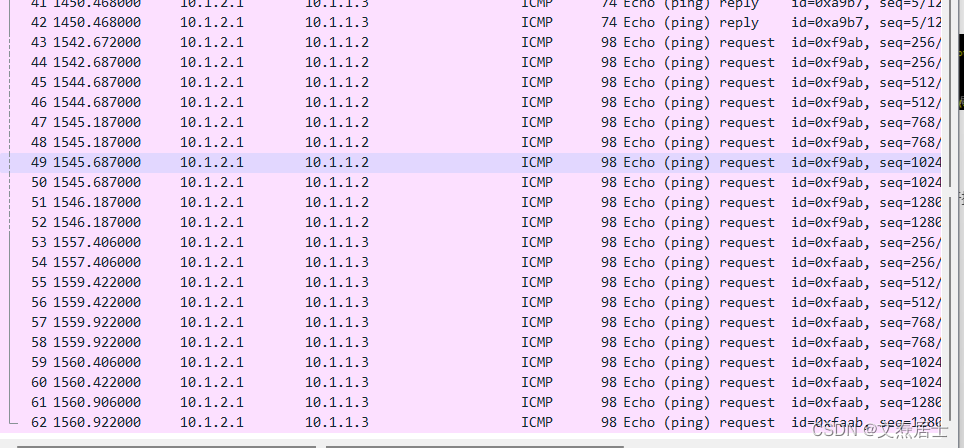
It can be seen that the drainage strategy is successful, and the device is attachedThe packet was successfully captured on the interface.
When the packet is returned, the data does not pass through the bypass device.If you want the return packet to also pass through the side-connected device, you should also need a flow strategy.
边栏推荐
猜你喜欢
随机推荐
kuberentes Auditing 入门
CGO 初步认知和基本数据类型转换
win10 xbox录屏功能不能录声音怎么办
[SWPUCTF 2021 新生赛] web
svg+元素js实现在图片上描点成框,并获取相对图片的坐标位置
PostgreSQL 介绍
Introduction to PostgreSQL
【Windows】你不能访问此共享文件夹,因为你组织的安全策略阻止未经身份验证的来宾访问,这些策略可帮助保护你的电脑
C. Rotation Matching
[Golang]如何优雅管理系统中的几十个UDF(API)
扩展中国剩余定理
paddle 35 paddledetection保存训练过程中的log信息
自建函数 测试例和语法——《mysql 从入门到内卷再到入土》
Uniapp编译后小程序的代码反编译一些思路
查询:复杂查询的语法和使用例——《mysql 从入门到内卷再到入土》
组合导航精度分析
Redis Command Manual
PostgreSQL — Installation and Common Commands
DELETE:删除操作语法&使用例——《mysql 从入门到内卷再到入土》
ACM模板笔记:最长不下降/上升子序列