当前位置:网站首页>On the three paradigms of database design
On the three paradigms of database design
2022-04-23 20:45:00 【Jan York】
My blog  https://www.ideaopen.cn/
https://www.ideaopen.cn/
normal form ?
Namely specification !
* The paradigm is “ A set of relational patterns that conform to a certain level , Indicates the degree of rationalization of the relationship between attributes within a relationship ”. * It's obscure, isn't it ? In fact, you can roughly understand it as the level of some design standard that the table structure of a data table conforms to .
The database paradigm is also divided into 1NF,2NF,3NF,BCNF,4NF,5N Generally when we design a relational database , At best, consider BCNF Is enough .
Design that conforms to the higher paradigm , Certainly Conform to the lower paradigm , For example, in line with
2NFRelationship model of , It must be in line with1NF.
1NF- First normal form
Each column of the data table should maintain its atomic properties , That is, columns can no longer be split .
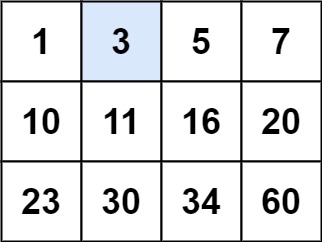
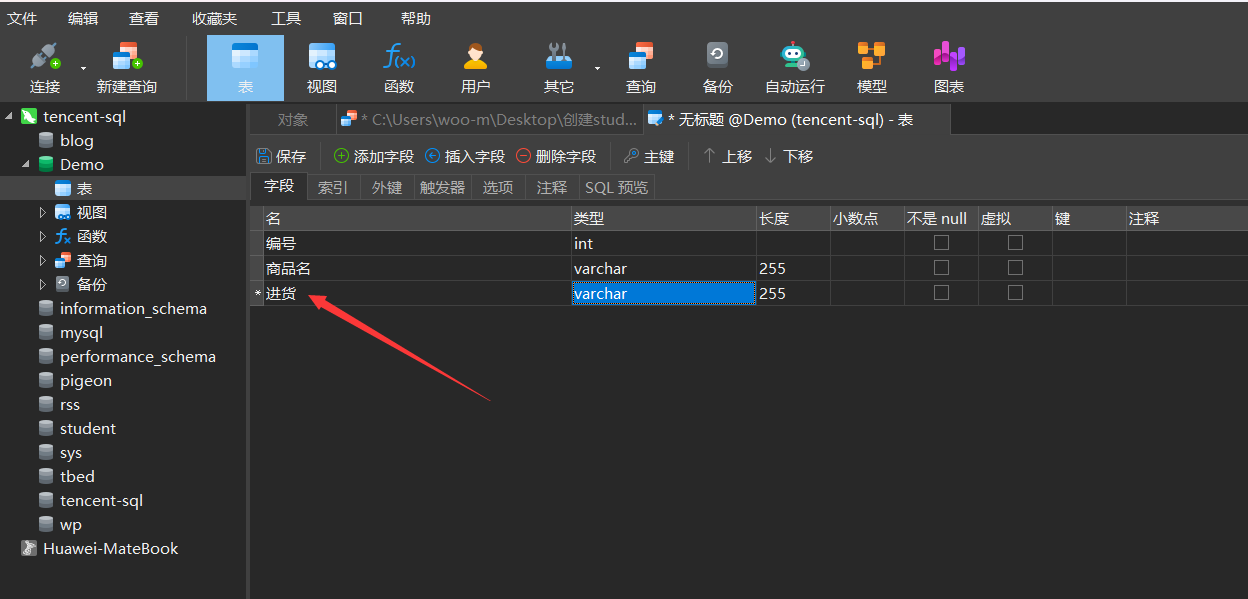
Such as this :

Stock it can also be divided into the quantity of stock , Purchase price and other attributes . So this is not in line with the first paradigm .

2NF- Second normal form
Second normal form (
2NF) It's in the first paradigm (1NF) Based on , That is to meet the second paradigm (2NF) We must first satisfy the first paradigm (1NF).
- That is to meet the premise of the first paradigm , When There are multiple primary keys When , That's what happens when it doesn't fit the second paradigm !!!.
- For example, there are two primary keys , There can't be such an attribute , It only depends on one of the primary keys , This is not in line with the second paradigm .
- The popular understanding is that any field only depends on the same field in the table .
rely on
In the data sheet , attribute ( Attribute group )X In certain cases , Can completely exit the attribute Y Depend entirely on X.
Completely dependent on
Complete dependency is for attribute groups , When a set of attributes X Can push it out Y Say when you are Y Depend entirely on X.
Part of it depends on
A set of attributes X One or more of the properties in can deduce Y Just say Y Depend in part on X.
3NF- Third normal form
First , To meet the third paradigm (3NF) must First satisfy the second paradigm (2NF).
in other words , Require a database table It doesn't contain Already included in other tables Non primary key Field .
Three paradigms must be ?
Our three paradigms are general norms . That is to say , It's just that I usually follow this specification .
however !!! It doesn't have to be observed , For example, sometimes , It's not a good thing that data is not redundant . therefore , We need to define , Build on requirements .
No redundant database is not necessarily the best database , Sometimes in order to improve operation efficiency , Improve reading performance , We must lower the standard of paradigm , Keep redundant data in place .
Other paradigms
BCNF-BC normal form
Relationship model R<U,F> in , If every determinant contains a code , be R<U,F> Belong to BCFN.
namely :
- All non primary attributes are fully function dependent on each code ;
- All primary attributes are also fully function dependent on each code that does not contain it ;
- No attribute completely depends on any set of non code attributes .
4NF- Fourth normal form
It is not allowed to have nontrivial and non functional multivalued dependencies between attributes of relational schema .
5NF- The fifth paradigm
- The fourth paradigm must be satisfied .
- Tables must be decomposable into smaller tables , Unless those tables logically have the same primary key as the original table .
Generally when we design a relational database , At best, consider
BCNFIs enough .!!!
版权声明
本文为[Jan York]所创,转载请带上原文链接,感谢
https://yzsam.com/2022/04/202204232039375929.html
边栏推荐
- Solution: NPM err! code ELIFECYCLE npm ERR! errno 1
- go slice
- 41. 缺失的第一个正数
- vulnhub DC:1渗透笔记
- Awk print special characters
- go reflect
- go array
- Install MySQL 5.0 under Linux 64bit 6 - the root password cannot be modified
- The more you use the computer, the slower it will be? Recovery method of file accidental deletion
- DOS command of Intranet penetration
猜你喜欢

The more you use the computer, the slower it will be? Recovery method of file accidental deletion
内网渗透之DOS命令
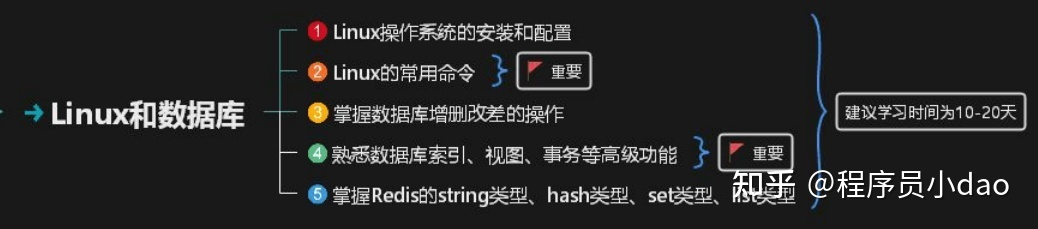
100天拿下11K,转岗测试的超全学习指南
LeetCode 74、搜索二维矩阵
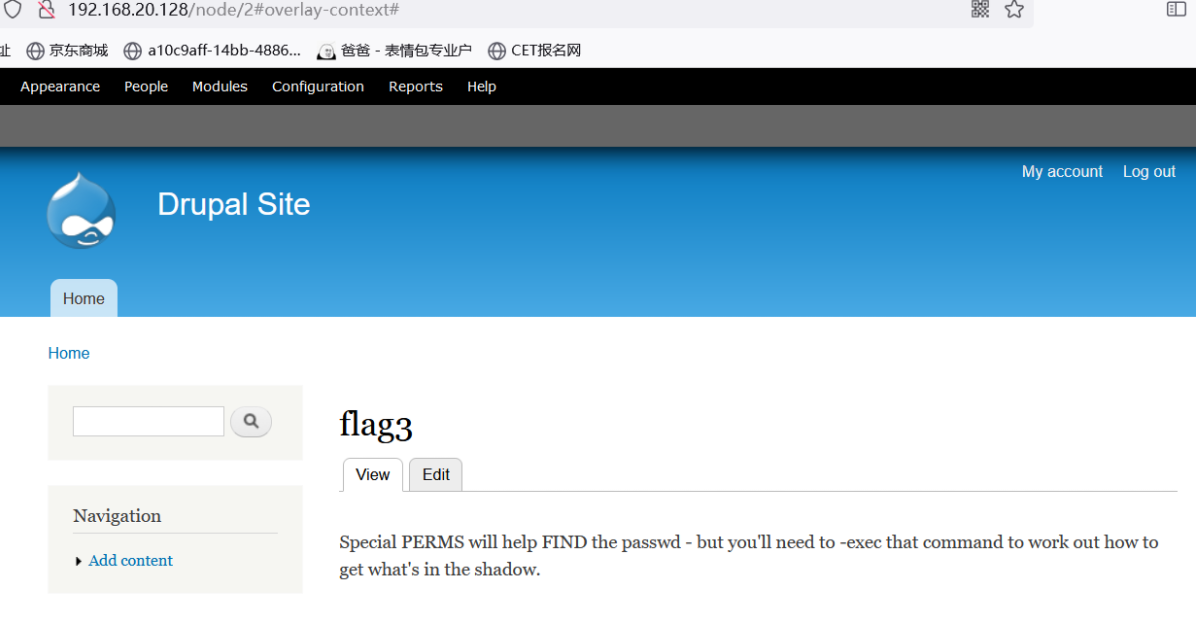
vulnhub DC:1渗透笔记
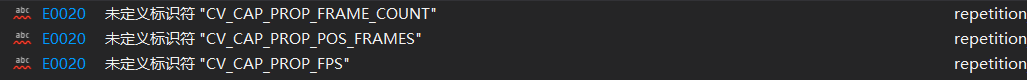
Identifier CV is not defined in opencv4_ CAP_ PROP_ FPS; CV_ CAP_ PROP_ FRAME_ COUNT; CV_ CAP_ PROP_ POS_ Frames problem
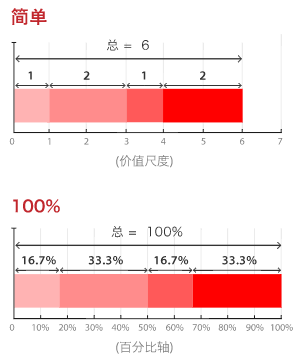
常用60类图表使用场景、制作工具推荐
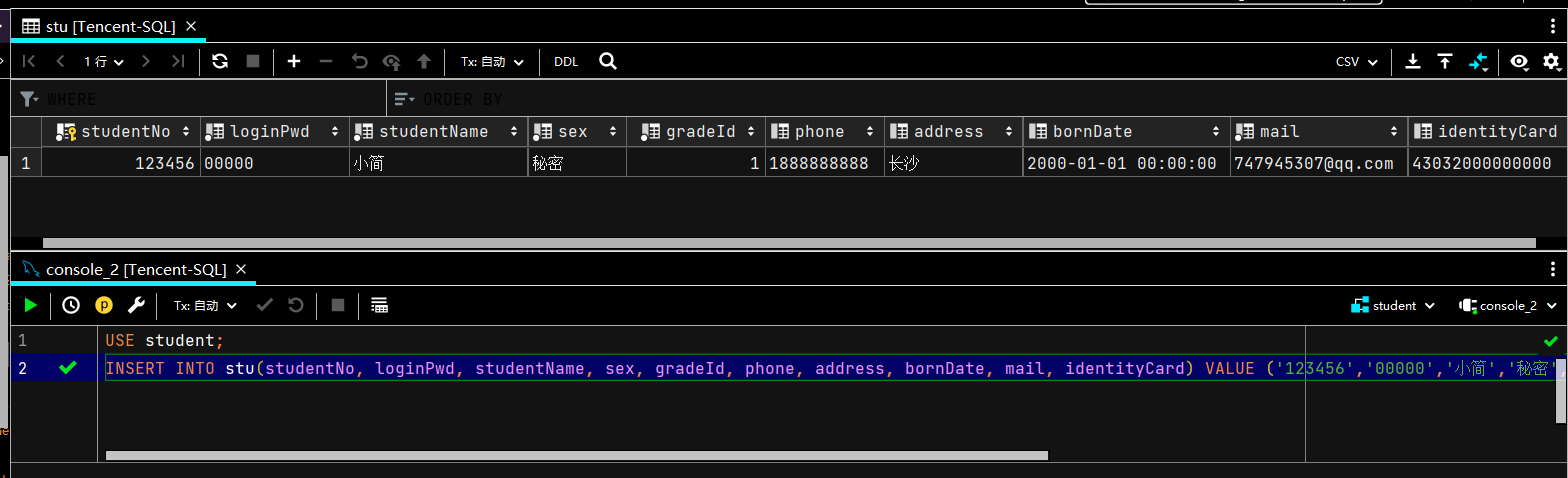
MySQL进阶之数据的增删改查(DML)
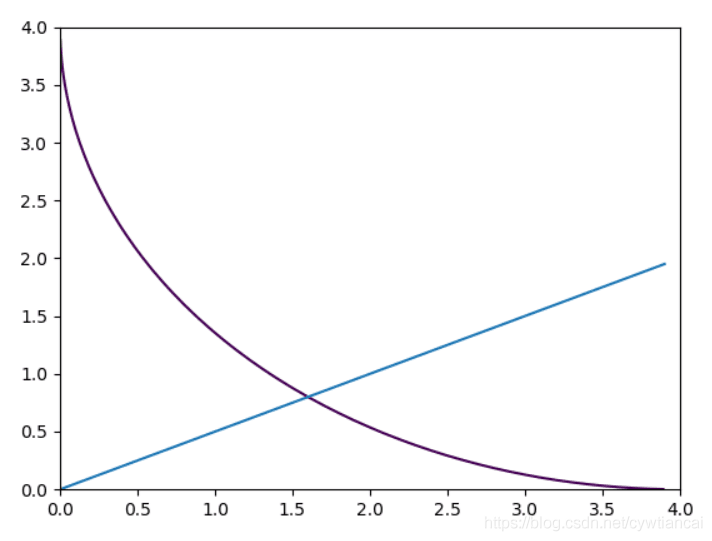
Monte Carlo py solves the area problem! (save pupils Series)
浅谈数据库设计之三大范式
随机推荐
Easy to use nprogress progress bar
SQL gets the latest record of the data table
LeetCode 1337、矩阵中战斗力最弱的 K 行
Psychological formula for converting RGB to gray value
go reflect
[PTA] l1-006 continuity factor
上海回應“面粉官網是非法網站”:疏於運維被“黑”,警方已立案
Install MySQL 5.0 under Linux 64bit 6 - the root password cannot be modified
MySQL 存储过程和函数
DOS command of Intranet penetration
Learn to C language fourth day
Vscode download speed up
又一款数据分析神器:Polars 真的很强大
Bracket matching -- [implementation of one-dimensional array]
LeetCode 709、转换成小写字母
[PTA] l1-002 printing hourglass
bounding box iou
Come in and teach you how to solve the problem of port occupation
Go zero framework database avoidance Guide
MySQL基础合集