当前位置:网站首页>How to protect ECs from hacker attacks?
How to protect ECs from hacker attacks?
2022-04-23 20:16:00 【Green fruit network gatu】

Methods to protect ECs from hacker attacks :1、 Check the services and applications on the ECS , Turn off unnecessary reports and get rid of unused Services ;2、 Check the security log regularly , Use DDoS Protection provider and the latest version of Apache, Disable compiler .
The details are as follows :
1、 Turn off unnecessary reports and get rid of unused Services
Spend some time checking cloud servers and services . Ask yourself , In order to make ECS work normally , Whether all these things are necessary ? If you are running unnecessary applications , Will make the server more vulnerable . For ports , You should use IP Table the port required to open the ECS . And then INPUT The default policy on the chain is set to drop . such , Any port you do not explicitly indicate to open will be ignored .
2、 Check for common security threats
We are always ready to deal with the latest security threats . however , Some of the most effective security threats are persistent threats . Protect your ECS in the following ways : Check the security log regularly , Use something like Cloudflare In this way DDoS Protection provider , Disable compiler , Use the latest version of Apache, But don't confuse your version number .
版权声明
本文为[Green fruit network gatu]所创,转载请带上原文链接,感谢
https://yzsam.com/2022/04/202204210554158301.html
边栏推荐
- Mysql database - single table query (II)
- NC basic usage 1
- 【文本分类案例】(4) RNN、LSTM 电影评价倾向分类,附TensorFlow完整代码
- STM32基础知识
- Alicloud: could not connect to SMTP host: SMTP 163.com, port: 25
- Unity创建超写实三维场景的一般步骤
- WordPress插件:WP-China-Yes解决国内访问官网慢的方法
- DTMF dual tone multi frequency signal simulation demonstration system
- PHP reference manual string (7.2000 words)
- JDBC tool class jdbcfiledateutil uploads files and date format conversion, including the latest, simplest and easiest way to upload single files and multiple files
猜你喜欢
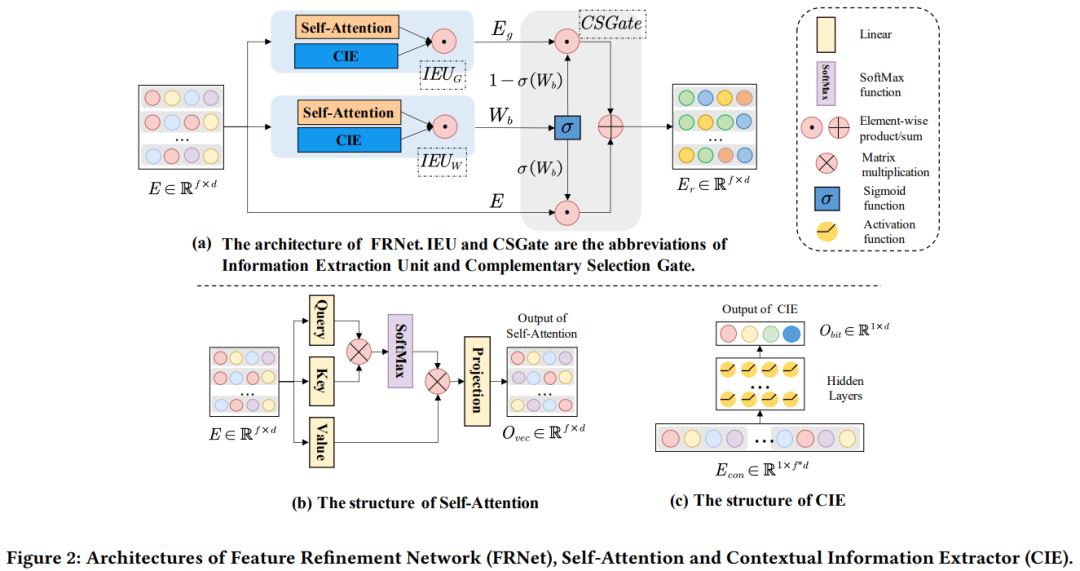
SIGIR'22「微软」CTR估计:利用上下文信息促进特征表征学习
![Azkaban recompile, solve: could not connect to SMTP host: SMTP 163.com, port: 465 [January 10, 2022]](/img/1a/669c330e64af8e75f4b05e472d03d3.png)
Azkaban recompile, solve: could not connect to SMTP host: SMTP 163.com, port: 465 [January 10, 2022]
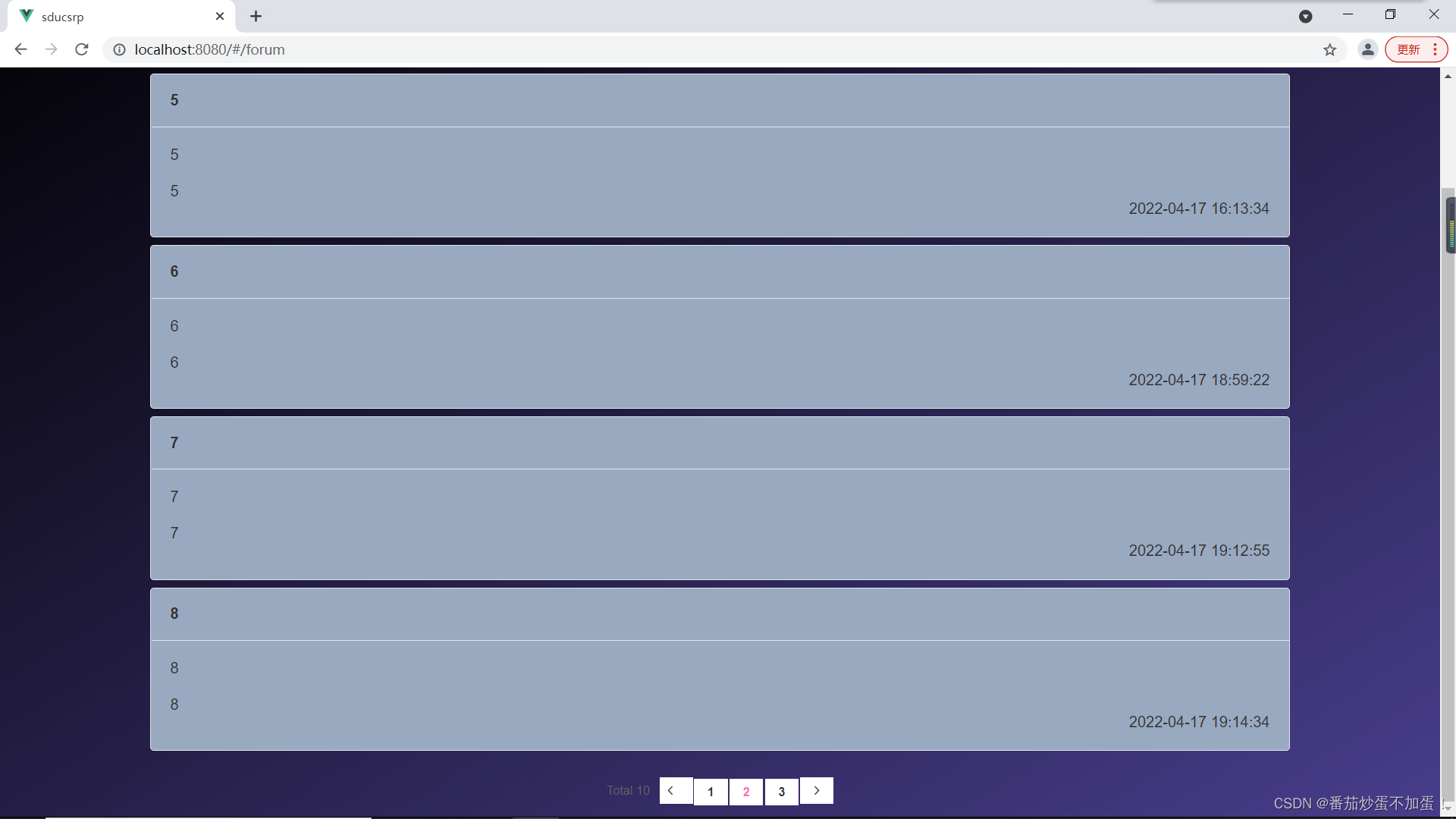
山东大学软件学院项目实训-创新实训-网络安全靶场实验平台(七)

DTMF dual tone multi frequency signal simulation demonstration system

antd dropdown + modal + textarea导致的textarea光标不可被键盘控制问题

Openharmony open source developer growth plan, looking for new open source forces that change the world!
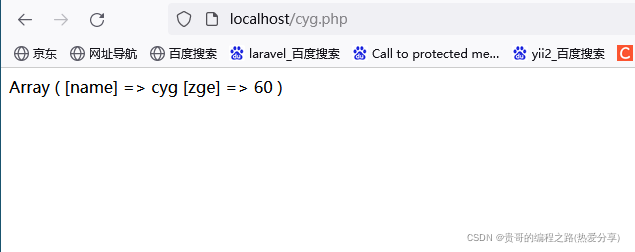
PHP reference manual string (7.2000 words)
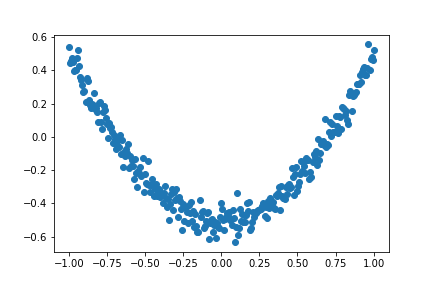
Don't bother tensorflow learning notes (10-12) -- Constructing a simple neural network and its visualization
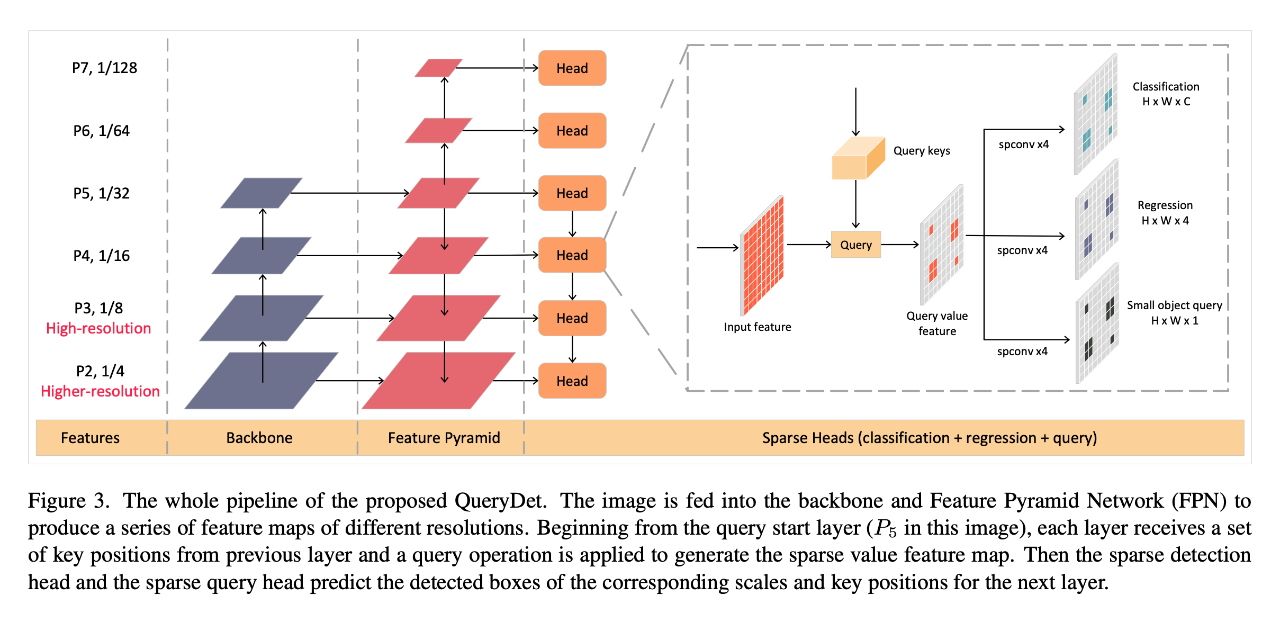
CVPR 2022 | querydet: use cascaded sparse query to accelerate small target detection under high resolution
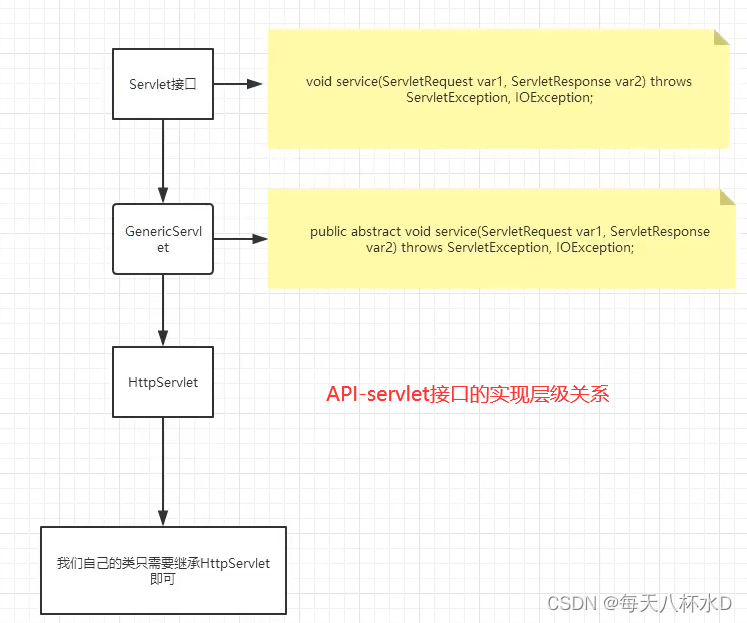
Servlet learning notes
随机推荐
NC basic usage 4
nc基础用法4
Paper writing 19: the difference between conference papers and journal papers
SQL Server Connectors By Thread Pool | DTSQLServerTP plugin instructions
Introduction to electron tutorial 3 - process communication
NC basic usage
R语言使用timeROC包计算存在竞争风险情况下的生存资料多时间AUC值、使用cox模型、并添加协变量、R语言使用timeROC包的plotAUCcurve函数可视化多时间生存资料的AUC曲线
An error is reported when sqoop imports data from Mysql to HDFS: sqlexception in nextkeyvalue
Openharmony open source developer growth plan, looking for new open source forces that change the world!
Servlet learning notes
Shanda Wangan shooting range experimental platform project - personal record (V)
Cadence OrCAD capture batch change component packaging function introduction graphic tutorial and video demonstration
JDBC database addition, deletion, query and modification tool class
Confusion about thread blocking after calling the read () method of wrapper flow
Mysql database - connection query
DTMF双音多频信号仿真演示系统
【数值预测案例】(3) LSTM 时间序列电量预测,附Tensorflow完整代码
Unity创建超写实三维场景的一般步骤
网络通信基础(局域网、广域网、IP地址、端口号、协议、封装、分用)
NC basic usage 3